Apple’s Notarization Apparently Includes Malware Too
- The macOS software notarization process has been broken by at least an adware author.
- Apple is refusing to share how the software checking system works, but it appears to be based on automated scanners.
- Apple users should still use an anti-virus, even if these have gotten hard to install on macOS today.
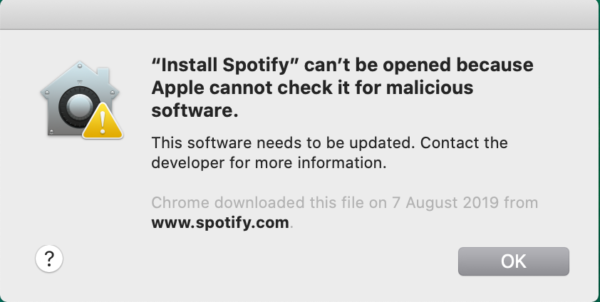
When Apple introduced the “notarization” process as an additional safety net meant to protect users against malicious software, everyone wondered how effective it would be. As Malwarebytes reports now, they have seen more than a single isolated case of a malware managing to somehow get notarized, so there’s clearly a hole in the system. It is entirely unknown if fixing it is easy or complicated for Apple, considering that the actors’ exact methods remain elusive.
Notarization is a process that was introduced by Apple as an additional step to code signing. Because malware authors have repeatedly demonstrated their capacity to steal valid code signing certificates from Apple, the tech giant figured that they needed to add another layer of checks.
So, notarization requires sending an executable to Apple, who then tests the software by running in-depth automated scans. If anything suspicious is found, the software gets rejected. Starting with macOS Catalina, no software is allowed to run unless it is notarized, preventing malware infections.
Source: Malwarebytes
As great as this may sound, malware authors have found a way to bypass the system. One way to do this is by not bothering to sign the software in the first place, which would absolve them from having to take the notarization step. This is how most of the Shlayer and Bundlore adware variants do it, for example.
The other way is to actually notarize the malware executable, which Malwarebytes believe is based on the tricking of the automated scanners. Apple isn’t willing to openly share how notarization works to prevent abuse risks. It appears, though, that malware authors have already figured it out nonetheless.
Source: Malwarebytes
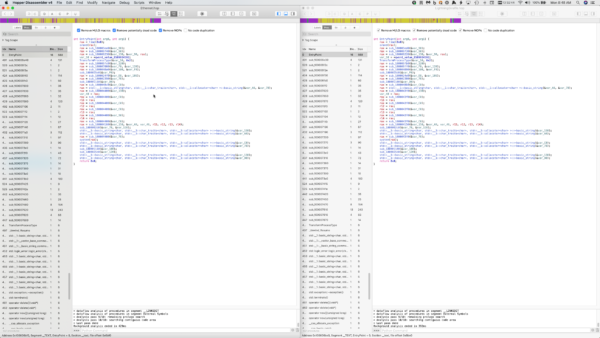
A sample of the Shlayer adware that has been notarized has intrigued the researchers, who carried out a code comparison to figure out how they did it. What they found were minor differences between notarized and the rejected versions, so the results are inconclusive.
Malwarebytes would love to test Apple’s scanners themselves by pushing various samples through the notarization process. Still, they claim to fear account bans, which Apple is known for delivering all too easily.
The story’s takeaway is that the notarization stamp doesn’t equal safety, and macOS users should be careful and think twice before they run anything on their systems. Apple OS users should still use some form of an AV/AM solution, even if installing these on the macOS has gotten annoyingly complicated.
Read More:
- Tesla Confirmed Cyberattack Attempt From Russian Hackers
- Apple Terminates Epic Games’ App Store Account Following Fortnite Dispute
- A Set of iPad Schematics Reveal Thinner Bezels, Face ID & USB-C