Apple Mail Has Been Exposing Encrypted Email Content Since July
- A researcher unveils a severe security bug in Apple Mail, which exposes encrypted content in plaintext form.
- The researcher informed Apple via email numerous times, starting on July 29, 2019.
- There are three ways to mitigate the problem, but Apple stated they plan to release a fix that deals with it soon.
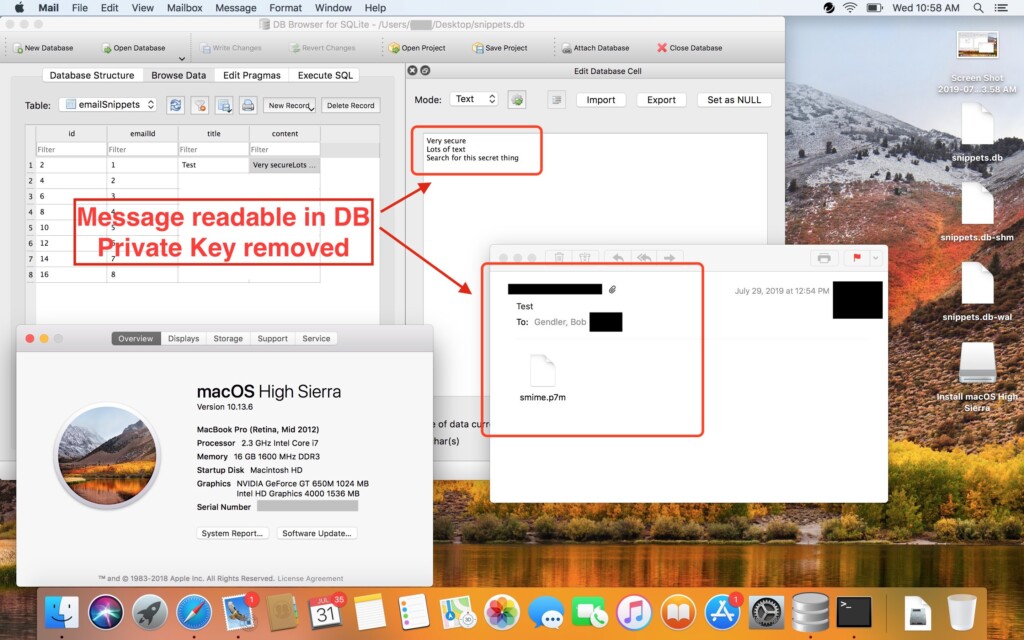
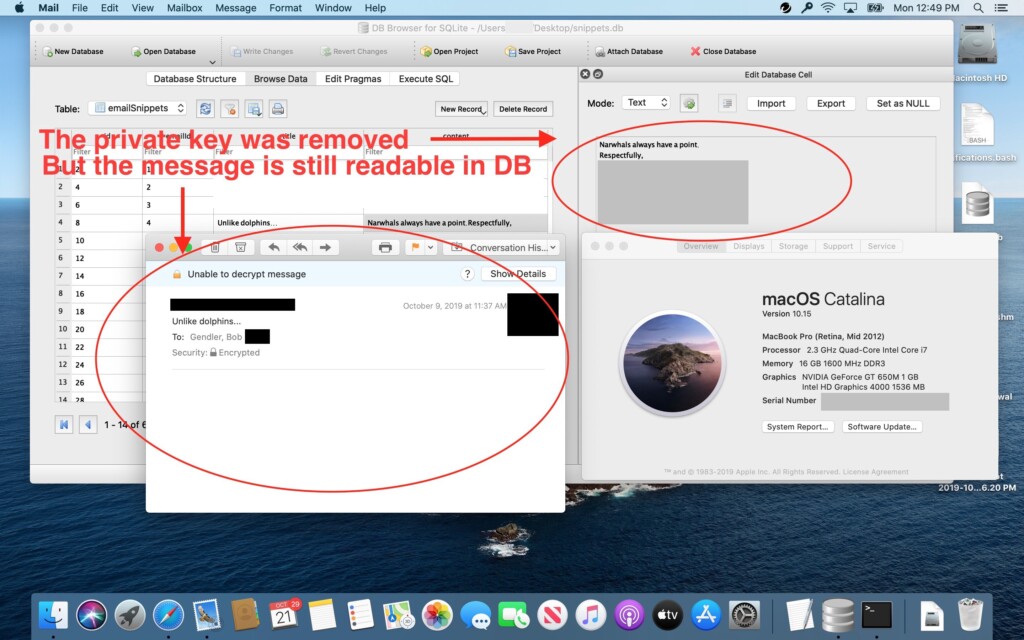
According to The Verge, Apple Mail has been exposing parts of encrypted email content for many months now, in plaintext form. The discovery was made by Mac specialist Bob Gendler, who was casually investigating how macOS and Siri suggest contacts and information to the user. The researcher discovered that the snippets.db database, which is supposed to store encrypted Apple Mail messages, is instead hosting this information completely unencrypted and without requiring a private key. Disabling Siri doesn’t stop this behavior. Apple was informed of this problem immediately, but the vulnerability remains unfixed.
Source: medium.com
Source: medium.com
The issue affects those who use Apple Mail on the macOS and use the email software to encrypt their messages. It does not affect those who are using FileVault to encrypt their entire filesystem. That said, we’re talking about a relatively small number of affected users, but the flaw remains critical nonetheless, especially since Apple knew about it for so long and is yet to fix it. The company now states that they have a plan to address the flaw in a future software update, however, they did not provide any specific timelines for it.
To mitigate the problem while we’re waiting for a fix, Gendler gives us the following three ways:
1. Manually select what Siri can learn from your apps, and uncheck the Mailbox. To do so, go to “System Preferences → Siri → Siri Suggestions & Privacy”
2. Run the following command in the Terminal: “defaults write com.apple.suggestions SiriCanLearnFromAppBlacklist -array com.apple.mail”
3. Deploy a System-Level configuration profile that applies to all users, and which turns off Siri from learning anything from Apple Mail. You may pick the profile from this GitHub repository.
Obviously, these are all temporary solutions, and won’t stop new emails from being stored in snippets.db. Deleting this file is the only way to ensure that it cannot be scanned by a hacker. If you are deploying macOS on a highly critical environment, using the FileVault would be your best bet right now. Gendler was so impressed by the existence of this flaw, as well as Apple’s negligence, that he sent multiple emails to the company including one towards Tim Cook himself on October 31. As the researcher points out: “For a company that prides itself on security and privacy, the lack of attention to detail on an issue like this completely and totally surprises me. It brings up the question of what else is tracked and potentially improperly stored without you realizing it.”
Has your trust in Apple Mail or even macOS been shaken? Let us know in the comments section down below, or on our socials, on Facebook and Twitter.