A Bug Disguises Malware as Apple Software
- Despite Apple being lauded as the most secured OS provider to its users, hackers have been misusing the third party tools to get past Apple’s scrutiny.
- Since 2007, hackers have been using a bug to make third-party security tools believe that Apple has signed malicious wares.
- This way, hackers could easily portray a file or an app as trusted.
Apple is very well known for its security when compared to other operating systems such as Android or Windows. Whether it is iPhone, iWatch, iPad, or MacBook – the tech giant is second to none when it comes to Apple software security. However, according to the recent findings of a cloud software Okta, it is believed that third-party software and applications have failed Apple’s stringent security and signing checks. However, the finding is only ‘recent’, this is happening for over 11 years now where hackers and online criminals have found an easy way to bypass Apple software security.
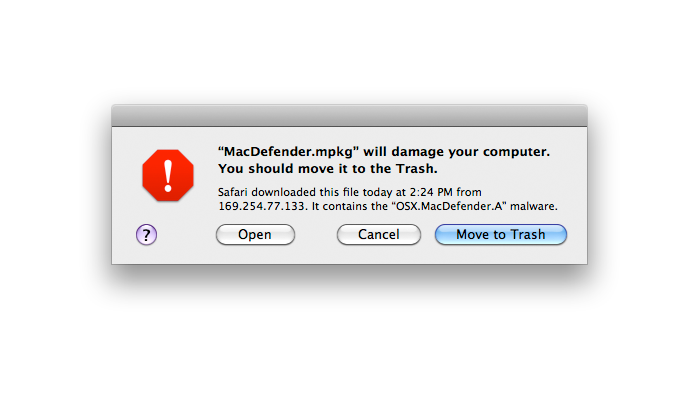
Courtesy of Apple
Even though the fault does not lie within MacOS, hackers somehow got past the scrutiny. The problem is within the third-party security tools and their implementation via Apple APIs. Hackers could easily trick the security tools hosted by third parties by making them believe that Apple has signed the ‘malicious wares.’ According to the Staff Engineer, Research and Exploitation at Okta, Josh Pitts said, “I can take the malicious code and make it look like it’s signed by Apple.”
Modern operating systems rely on digital signature and over the past few years, it has become a key security function. It goes without saying that you are bound to trust a file or an app that is cryptographically signed by Apple. How about if YOUR security tool tells you the same? For years now, hackers have been using this bug to sign certain apps with a private key of trusted parties.
Hence, in a nutshell, Apple’s APIs are indeed confusing.