Indian Sikhs Are Being Targeted by Spyware Android and Windows Apps
- A pro-India group of actors is targeting Sikhs in the country using fake Android and Windows apps.
- The apps are a spyware and a trojan, created to steal sensitive information by working in the background.
According to reports from the Qihoo 360 Core Security team in China, there’s an ongoing phishing and spyware distribution campaign targeting Sikhs in India. There are approximately 30 million Sikhs, followers of a 15th-century monotheistic religion, and most of them (83%) live in Punjab, India.
Many people in this religious group seek political and regional independence, so they have been accused of pro-separatism and anti-India propaganda. This malware distribution campaign exploits precisely that aspect of Sikhism, so it’s highly targeted and has very specific motives.
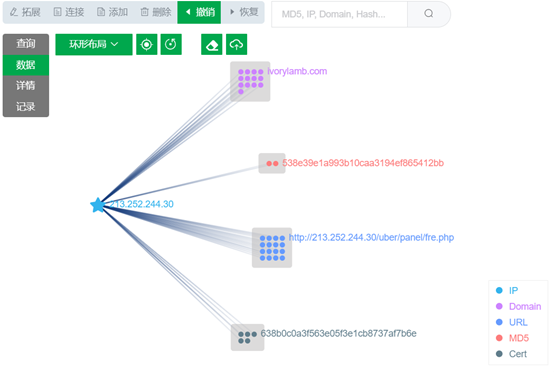
The Chinese researchers found out that the app named “2020 Sikh Referendum,” which is free to download and supposedly attempts to organize Sikhs in voting for the secession of Punjab, is associated with two phishing websites. Based on these websites' certificate, it appears that the attacks started in January 2021 and are still ongoing.
The app itself is focusing on the Khalistan movement, which is the proposed Sikh sovereign state in the Punjab region, but under the hood, it deals with spyware functions. More specifically, the following stuff:
- GPS recording
- Microphone recording
- View contacts
- SMS record
- send messages
- call records
- View installed apps
- View for permissions
- Real-time clipboard recording
- Real-time notification record
- View WiFi network records
- File browser and download
The researchers report that there’s also a Windows app, basically a variant of the “Pony” trojan, which can collect data from the compromised machines. This application is distributed via spear-phishing emails that reach practitioners engaging in the foreign trade industry. Thus, we can deduce that the PC trojan is more active and targeted while the Android app is passive, relying on the action of Sikhs themselves.
As for who may be behind the campaign, Qihoo 360 mentions APT-C-35, a group that has been previously linked with attacks against the Pakistan government and prominent businesses in the country.
The malicious app is not to be found on the Play Store, although it had made its appearance there initially but was promptly removed. Instead, it is distributed through the URLs “pro-khalistan[.]app” and “sikhsangarsh[.]com”, so beware. These URLs may change of course, so it’s good to remember that generally, you shouldn’t trust anything that comes from outside the Play Store.