A Russian Defense Contractor is the Developer of the ‘Monokle’ Android Surveillanceware
- Researchers claim that there’s a definite connection between Monokle and the Special Technology Centre.
- STC is a company whose collaborations with the Russian Intelligence Agency has been long documented.
- Monokle could be the malware that enabled Russia to interfere in the 2016 U.S. Presidential Election.
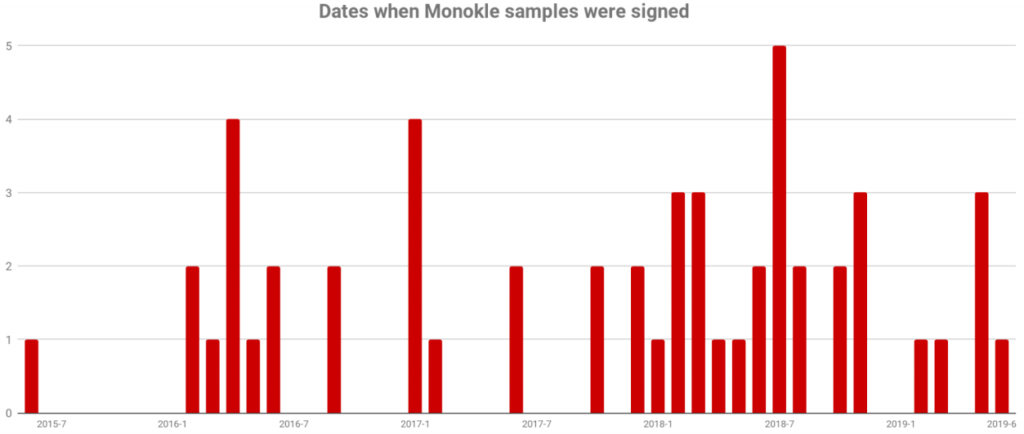
According to a report by Lookout researchers, the St. Petersburg-based company “Special Technology Centre Ltd.” (STC) is the developer of a recently discovered and sophisticated set of custom Android surveillanceware tools called “Monokle”. STC is well known in the U.S. because it is the company that provided the material that enabled the GRU (Russian Intelligence Agency) to interfere in the 2016 U.S. Presidential election. That said, Monokle could be the very thing that made the exfiltration of crucial data from high-profile targets in the U.S. possible, sending this info back to Russian C2 servers.
image source: lookout.com
Monokle is a set that features rich functionality, including remote access trojan (RAT) capabilities, data exfiltration, injection of malicious certificates to the infected device’s trusted certificates, and finally the laying of the ground for man-in-the-middle (MITM) attacks to take place. Monokle doesn’t require root access on the device and makes extensive use of the Android accessibility services to access and grab data from third-party apps. Even more impressively, it can record the device screen, steal the entered PIN or unlock pattern, and use predictive text dictionaries to figure out what topics the victim is mostly interested in. Recording or even making calls, tracking the device location, getting the password salt, and retrieving calendar information is also possible for the malware.
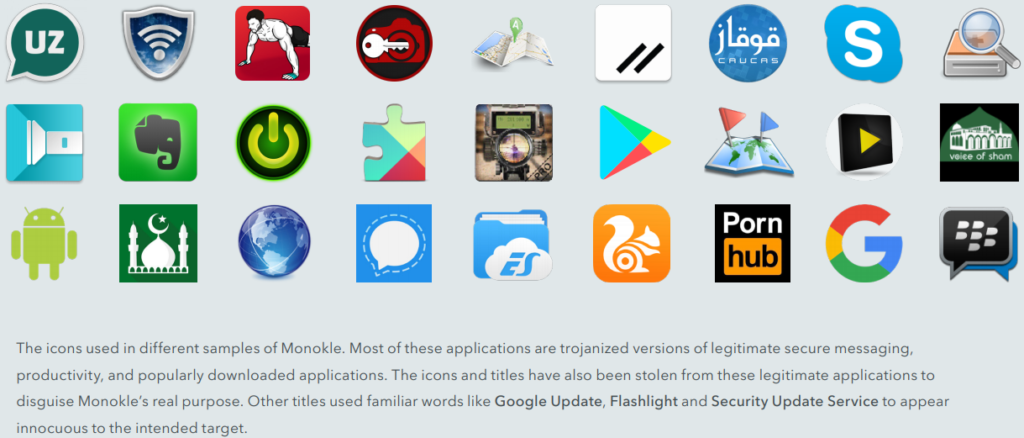
Lookout clarifies that Monokle is not to be found abundantly in the wild, but instead is a tool that’s deployed in highly-targeted attacks. As reported, the applications that contain the particular trojan remain fully functional, and there’s nothing in the functionality of the malware that could give its presence away. That said, most of the owners of the infected devices never realize that they are getting monitored by Monokle. Some of the apps that have been found to contain the trojan include Skype, Evernote, Play Store, and U.C. Browser, so anyone could have fallen to the trap.
image source: lookout.com
STC is a private defense contractor of Russian authorities and has been repeatedly involved in projects of the Russian military. For example, they have developed Unmanned Aerial Vehicles (UAV) and Radio Frequency (R.F.) equipment for the army. For this reason, the U.S. has imposed sanctions on the company since 2016, as their role was clear since then. As Lookout points out, STC is developing both offensive and defensive Android software, so the Monokle is only one of the possibly many tools that they are empowering GRU with.
Have something to comment on the above? Feel free to do so in the section down below, or join the discussion on our socials, on Facebook and Twitter.