Indian Banks and Finance Companies Targeted by Multi-Staged JSOutProx RAT Malware
- Indian banks and financial institutions are being targeted by a multi-tier JSOutProx RAT that acts in two stages.
- The malware uses spear-phishing emails with compressed attachements that have a transaction-related name.
- The specific RAT was discovered in 2019, and since then it grew to include new functions but kept the hiding pattern similar.
Quick Heal Security Labs has revealed it has been noticing JSOutProx RAT-based cybersecurity attacks on Indian SMBs in the Banking and Finance sector since early 2021. This is a JScript-based RAT stored on a target device as a .hta file and first executed by the mshta.exe process.
The first mode of infection is via a spear-phishing email with a “.hta” compressed attachment named for a financial transaction. These hold a double-extension-like format, for example, “_pdf.zip”, “_xlsx.7z”, “_xls.zip”, “_docx.zip”, “_eml.zip”, “_jpeg.zip”, “_txt.zip” etc.
The RAT itself is a 2019 discovery in the cybersecurity space where it has grown since then to include new functions, commands, and process obfuscation. Now, this also includes over 1 MB of obfuscated code, base64-like string array sets, configuration data for malware executables, and rc4 string decryption functions. Meanwhile, the concealment pattern remains similar across all versions and both stages.
According to Quick Heal’s official statement, the infection is delivered in two phases. The first has a very elementary and limited functioning version, further bolstered by a second phase payload delivery. The first phase usually targets low-access privilege individuals in a small-scale BFSI business and then uses their contacts directory entries to proliferate the infection further.
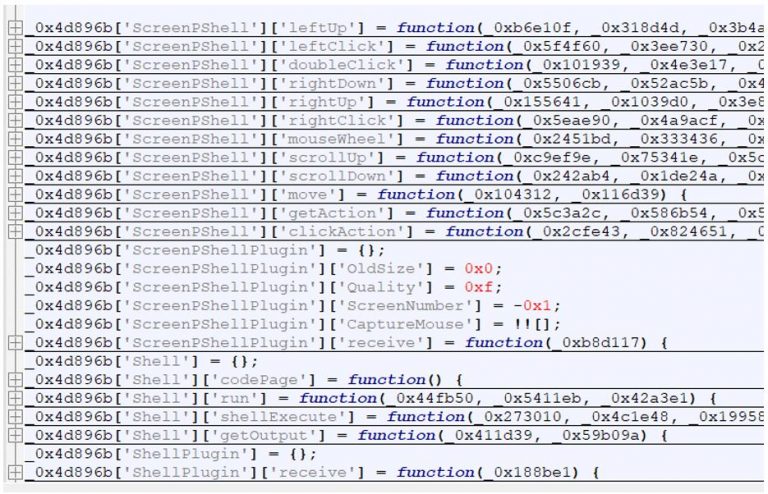
The very first step involves delivering a .hta file and executed by the mshta.exe process that creates entries in registry and startup, can create or terminate a process, perform file operations, and download plugins. It also has the functions needed to conduct limited mouse and keyboard operations via “ScreenPShell” command-based PowerShell script executions. The actors would send out hundreds of emails per day using different attachment names to rope in individual targets.
Upon config data decryption, we see the malware using a C2 domain “BaseUrl” and HTTP protocol communicated via port number. It uses the “Password” parameter for downloading plugins for C2 assembly while the ”Tag” parameter holds the campaign ID. There are other fields like “ViewOnly” that are used for monitoring target activity exclusively. This enables virtually digital noise-free observation to prevent intervention before the attacker executes their attack.
In the second stage, the RAT uses a “.js” startup file or a “.tmp” file in the %temp% folder executed via wscript.exe, and it has a different C2 from the first stage. These samples have about a 3 MB size and include DotUtil functions to download and execute .NET assemblies in the device memory. The second-stage RAT also drops a C++-based Netwire RAT operating with the distinct C2 address.
This RAT malware application uses several commands, config parameters, and similar user-agent strings across JSOutProx and Adwind RATs variants. It is possible that these agents are the same as JSOutProx RAT, with their tactics changing from dropping detectable initial vectors to jar files dropped at the second stage to hide their activities for longer and bypass antivirus sweeps.
The C2 domains examination indicates that this attack is focused exclusively on Indian BFSI companies. Such JavaScript or similar malware evolve rapidly, but their process patterns often remain the same and easy to recognize after the initial vector is detected. However, it is not the only RAT discovered targeting India this year.