What’s Wrong with Hollywood Hacking?
Who doesn't love a good bit of Hollywood hacking? Movies like The Matrix and Swordfish are exciting techno-thrillers. They show us a nail-biting world full of action and excitement. Hollywood hackers are like action heroes who are also incredibly smart. Computers in movies behave as no real computer does. You'd think that an audience who uses real computers on a daily basis would have an issue with this. Yet we have no problems with suspension of disbelief at all.
It's Way More Tedious in Real Life
In the movies, hackers work frantically along to pulse-pounding music. The scenes are editing to be like an action sequence. You can almost taste the adrenaline coursing through the hacker's system.
Real-life hacking could be no further from this Hollywood hacking trope. It's just a person sitting in front of a computer, watching some text boxes change every now and then. If someone is hacking from a coffee shop the average person would not be able to tell them apart from any other computer user. The movies make hacking look like badass magic. It might actually be badass magic in real life, but it certainly doesn't look it.
Real Hacking is Complex and Time-Consuming
In terms of screen time, Hollywood hacking takes a minute. These fictional hackers can slice into a system so fast their keyboards can barely keep up. It's thrilling, but nothing at all like hacking in real life. That involves long periods of research, gathering information then trial and error. It's more like a hobby building model planes than being internet, Batman.
No Graphics
Hollywood hacking sure is heavy on the visuals, which makes sense since they are picture stories after all. Hacking in the movies usually involves fancy 3D graphics and cheesy VR worlds.
You probably already know this, but hacking in real life doesn't actually look anything like that. Well, maybe with the exception of the first Jurassic Park movie. That graphical interface for the computer file system is actually a real SGI workstation application.
For the rest, it's just text and more text. Maybe you'll be treated to a spinning globe animation or something or a cool piece of hacker demo scene magic, but that's about it. We all understand why a movie has to give some visual interpretation of what hacking looks like, but it's an interpretation that takes some Atari bleeps and bloops and extrapolates Tron from it. Not remotely realistic.
Real-Time Hack Detection
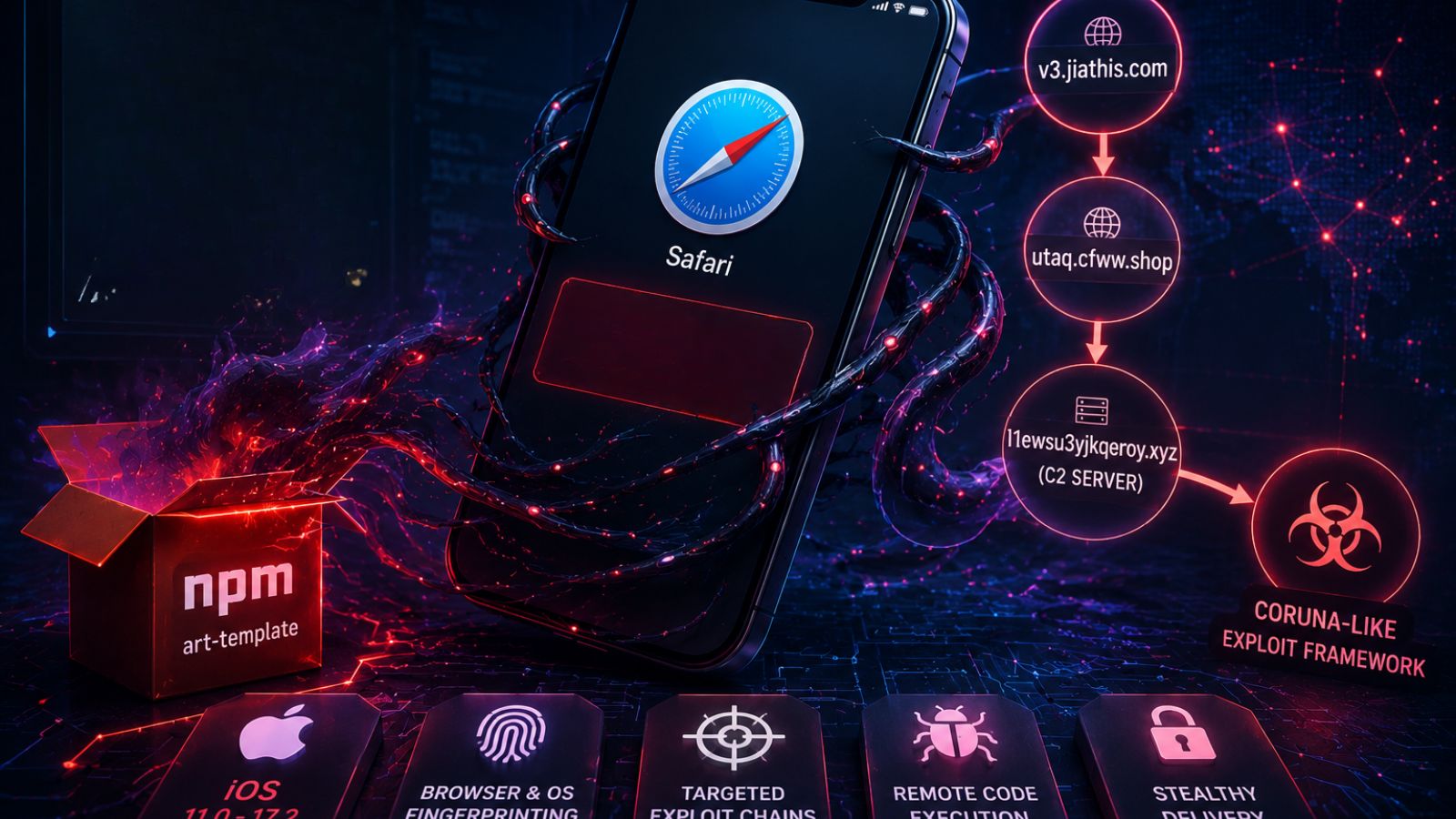
Another dumb trope is the one where our heroes detect someone hacking into their system and then trace them back to their real physical location. It's a good way to create drama, tension and move the story forward. Unfortunately, it's pretty much bunk. In real life, hacks are discovered after the fact. The way things work, people who try to intrude either get blocked by security measures, like a firewall or they make it past and raise no alarms. This is why data breaches are sometimes discovered years later. After the information that was stolen surfaces on dark web markets.
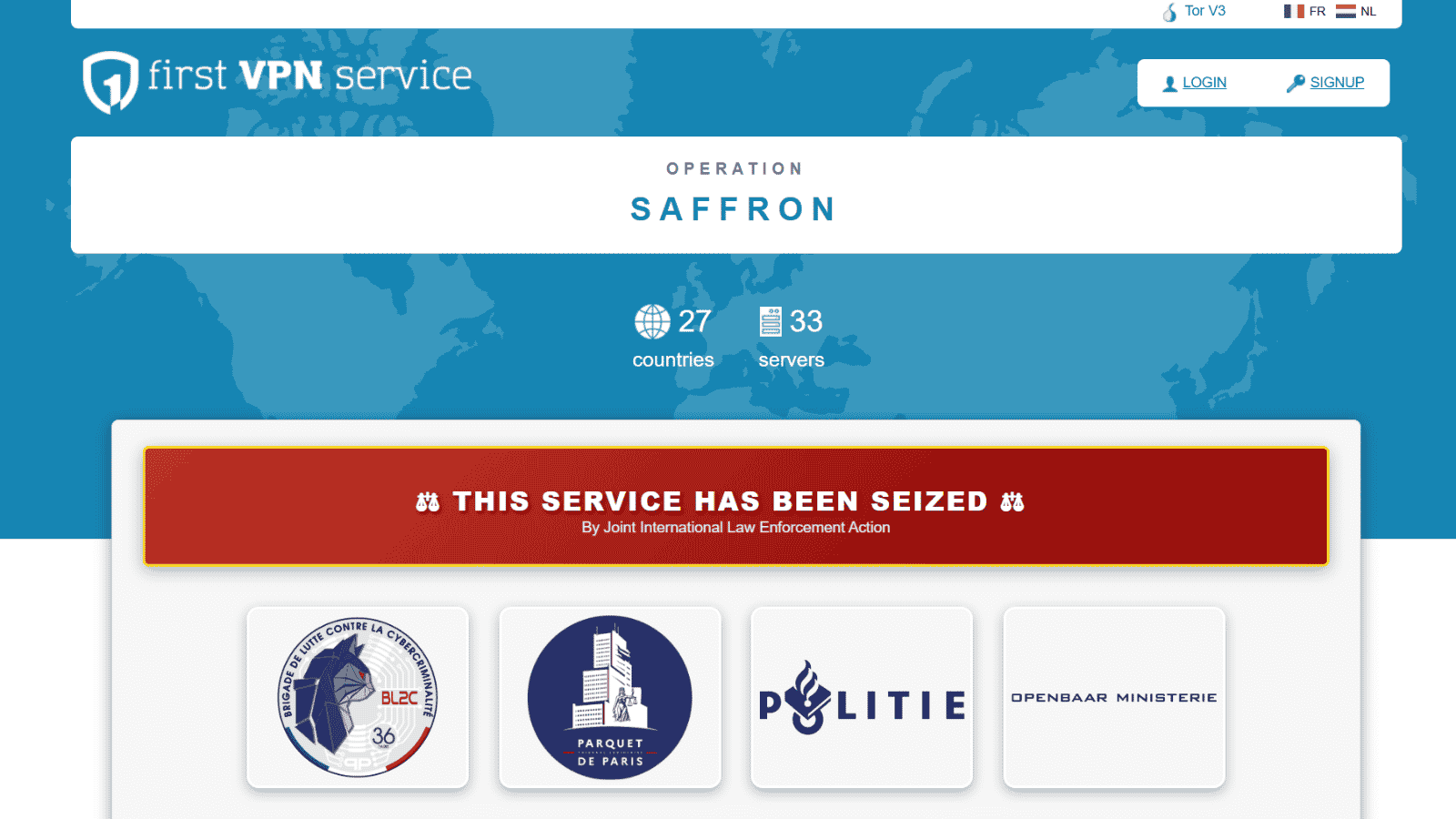
At other times the discovery happens because the hacker deliberately left a message for the system owners. If the hack cause damage, that's obvious immediately, but of course there's no way to "trace" the hacker. Especially since hackers take great pains to put an impossible amount of misdirection between their real location and the location of the hack. Tools like VPNs, Tor, and a few other tricks make it pretty unlikely that the real pros will be caught.
Real-life Hackers Look Like Everyone Else
In the movies, hackers are often portrayed as edgy kids who wear leather trench coats and smoke. While there are probably some hackers who actually do match this description, the truth is you can never tell. Apart from professional white hat hackers who are known to the public, hackers are anonymous. That guy you saw with his kids buying video games in the store could be a hacker. The teenage girl sitting in the library is just as likely to be. Hackers are all people with a strong interest in technology and the intelligence to apply that in uncommon ways, but they can look like anyone. Not just someone who looks like a character from a Gibson novel.
The Hacker Dungeon is Overkill
In movies hackers often work from special hidden locations, using intimidating equipment that could fill a basement. In reality, hackers don't need a small government data center to infiltrate computer systems. For example, at 18 the late Jonathan James hacked the US Department of Defense and NASA with just a normal Pentium-class home computer. These days hackers can do stuff with a typical smartphone that would make your head spin, so don't think ever hacker is operating from something that looks like a ship from the Matrix.
Things Are Getting Better
The good news is that the depiction of hacking (and computer geekery in general) is improving in TV and film. The people making our shows and movies are more tech-savvy and coding is the sort of thing taught in school these days. Yes, in order to make good entertainment some dramatic license still has to be taken. However, shows like Silicon Valley and Mr. Robot have a much more grounded depiction of what hacking and computer tweaking really looks like.
Does it really matter if hacking is so outlandishly inaccurate on TV or in the movies? Maybe not in a general sense, but since people actually have to face the consequence of real-life hacking, it might help to have a more realistic image of it.
What Hollywood hacking trope grinds your gears the most? Let us know down below in the comments. Lastly, we’d like to ask you to share this article online. And don’t forget that you can follow TechNadu on Facebook and Twitter. Thanks!