New ‘Capesand’ Exploit Kit Targets Adobe Flash and Internet Explorer Flaws
- A new exploit kit is under heavy development but also widely deployed already.
- Capesand is targeting Adobe Flash and Internet Explorer, while using open-source components.
- The kit may be based on the older Demon Hunter kit, as it features many similarities.
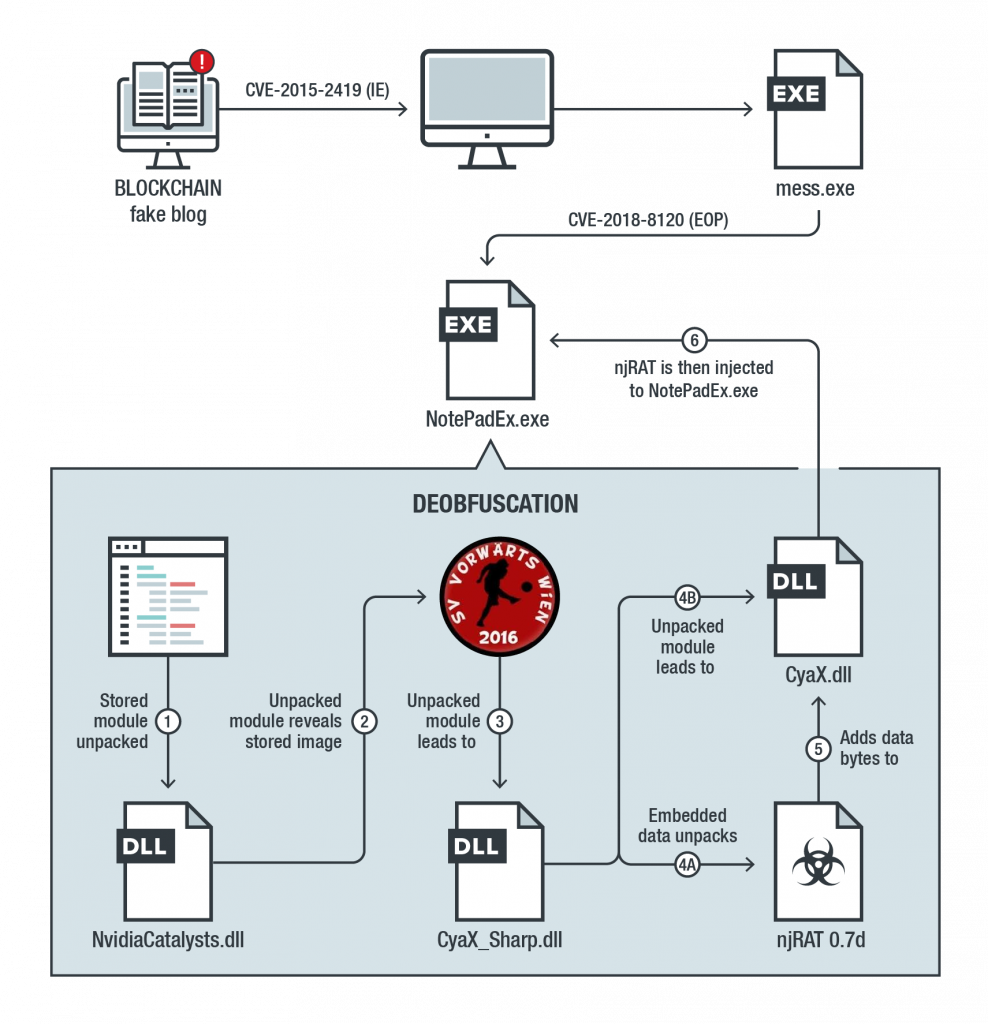
As reported by Trend Micro researchers, there’s a new malicious kit named "Capesand", trying to exploit recently discovered vulnerabilities in Adobe Flash and Internet Explorer. The researchers first noticed Capesand in October, and since then, they have seen significant development work put into it. The actors who are using it were previously relying on the Rig exploit kit but decided to change their tool with Capesand. The latter features a panel and a set of exploits, but it is generally unfinished yet. Still, it is being used extensively, and this could be attributed to a quick-development plan.
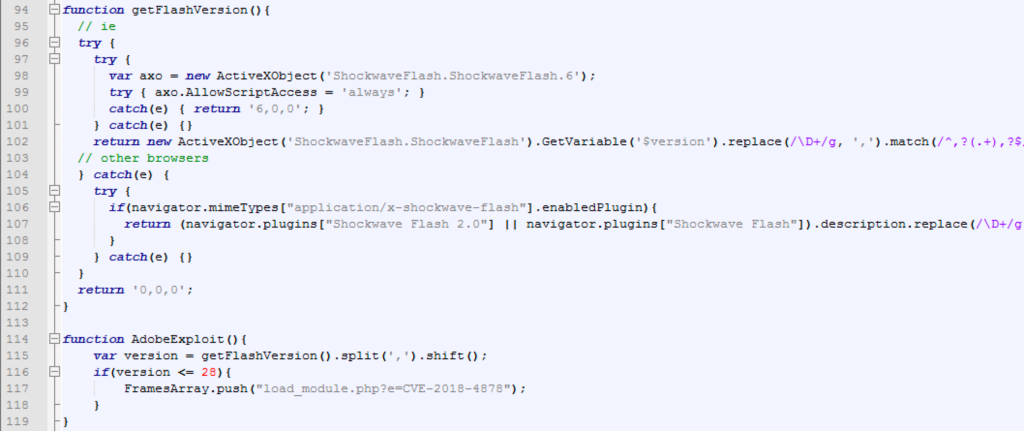
The Capesand kit is a relatively simple one that uses open-source code that is freely available. The same applies to the exploits, as there isn’t a zero-day or anything like that hardcoded into Capesand. The packing techniques and obfuscation are also based on known tools and methods. In most of the cases that were analyzed by Trend Micro, the actors used a fake blockchain malvertisement. In its current state, the kit is looking for the following flaws:
- CVE-2018-4878 (Adobe Flash)
- CVE-2018-15982 (Adobe Flash)
- CVE-2018-8174 (Microsoft Internet Explorer)
- CVE-2019-0752 (Microsoft Internet Explorer)
- CVE-2015-2419 (Microsoft Internet Explorer)
Source: Trend Micro Blog
The CVE-2019-0752 is mentioned in the source code, but it is not implemented yet. This indicates that the kit is still under active development and more vulnerabilities are bound to be added to it soon. Using what is already there, Capesand will compromise a vulnerable system and then download an additional payload to try and exploit CVE-2018-8120 (privilege escalation). During this process, one of the Capesand’s modules is checking for the presence of ESET security products, trying to avoid detection and analysis.
Source: Trend Micro Blog
To conclude, Capesand will continue to attempt deliveries as a service through a remote API, using mirrored versions of legitimate websites that have domain names that are deceptively similar to the actual ones. The kit has been noticed by Trend Micro, so it will be hard for its developers to continue what they do from now on, as the researchers will be following them closely. As for the victims, patching your Internet Explorer and Adobe Flash Player is the best way to render Capesand incapable of doing you any harm. Finally, pick a reliable internet security solution and set it up on your system so that Web-based threats like Capesand are blocked.
Have you already encountered Capesand? Let us know of the details in the comments section below, or on our socials, on Facebook and Twitter.