Previewing a Word Document is Enough to Infect you with Malware
- A malicious MS Word document that can run PowerShell code through preview has been spotted.
- The document is based on the parsing of the Explorer or Outlook code to execute its phishing attack.
- Users are advised to disable the Office Preview feature, as this will get increasingly risky.
As reported by Bromium’s threat intelligence researchers, there’s a new Microsoft Word document that can infect the victim’s machine even without the user actually opening the file. The “unusual” document can download its malicious payload after the user is merely previewing it, while it can successfully avoid detection by many anti-virus tools. This makes it especially dangerous, as most people would think that previewing the document that comes as an email attachment is a safe step to assess it further, but in this case, it would be enough to get the mill of problems rolling.
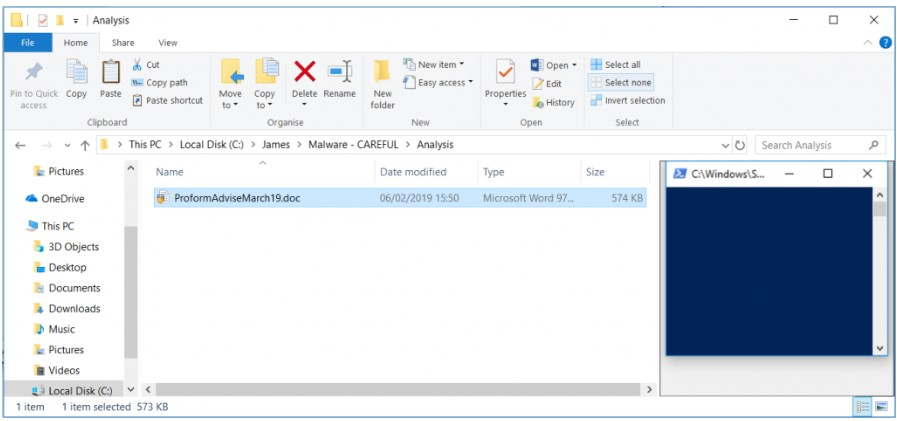
Windows Explorer and MS Outlook both offer users the convenience of previewing a document on a special pane in the right side, displaying an image of what is inside it. However, to provide this useful feature, the document is actually parsed with the macros being switched off for added safety. In this particular case, the document does not rely on macros, but instead it is using PowerShell to inflict the damage to the victim’s machine. More specifically, it contains five embedded Excel workbooks that sport a base64 encoded text that is converted into a PowerShell script and executed upon the file preview.
source: bromium.com
If previewed right from the browser, the document is tagged as “untrusted” by the ADS zone identifier, while the default Office configuration should display a warning dialog about the document. However, and as Bromium researchers point out, many people chose to disable this proactive measure on their office suite in order to avoid the multiple false alarms that stem from it. Since the Excel file is opening without the user clicking the file for execution, it will be easy to miss in systems where a lot of Excel documents are open at any given time.
The recommendation is never to trust documents that come as email attachments from unexpected and untrustworthy sources. Moreover, and since we see attacks that work through the preview function, it is also suggested that the Office Preview feature is disabled at all times. As more of this type of documents are bound to empower malware campaigns, it is likely that we’ll see variations that are entirely free of having to use macros in the near future.
Do you have anything similar to report? Share your experience with macro documents in the comments section below, and feel free to warn others on our socials, on Facebook and Twitter.