Over 20,000 Infected WordPress Websites are Launching Botnet Attacks
- A number of infected WordPress websites are trying to break into other secured websites on the platform.
- Security firm Defiant was the first to spot the malicious activity, and the attackers are taking advantage of dictionary attacks.
- WordPress website owners can avoid being attacked through security plugins.
The company behind popular WordPress security plugin Wordfence discovered large-scale attacks being conducted by over 20,000 infected websites on the platform. The infected websites have implemented dictionary attacks on various websites, a method that repeatedly tries a combination of usernames and passwords until it successfully breaks into a website using the tactic.
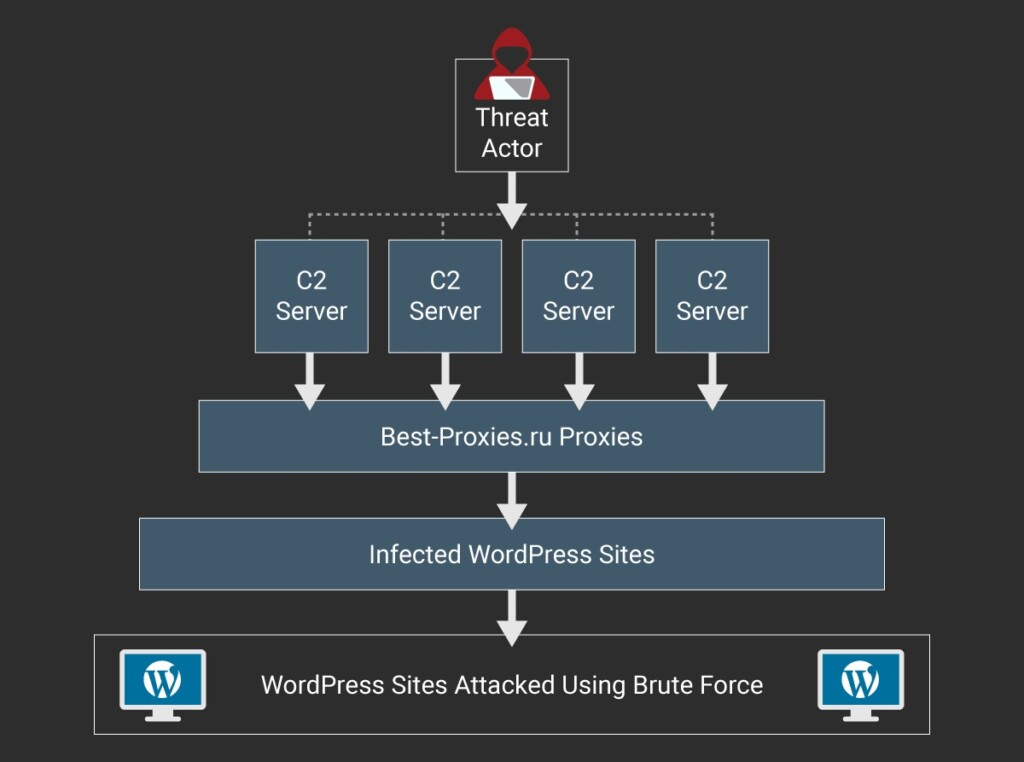
Image Courtesy of Wordfence
Mikey Veenstra from Defiant Security released a report that offers more insight about the ongoing attacks. It has been discovered that the botnet used by the infected websites is run by command control servers that make the infected websites attack other secure WordPress sites.
There are over 14,000 proxy servers deployed to relay information across the servers. There is a list of WordPress targets that the infected sites are currently attacking. According to Veenstra “If the brute force script was attempting to log on to example.com as the user Alice, it will generate passwords like example, alice1, alice2018, and so on. While this tactic is unlikely to succeed on any one given site, it can be very effective when used at scale across a large number of targets."
Fortunately, the WordPress botnet is not foolproof, and there are means of preventing it from getting into your website. Security researchers have been able to expose the infrastructure that is supporting the attacks, and there are flaws in the authentication systems as well.
If you own a WordPress website, the best course of action is to install any security plugin capable of preventing brute-force attacks or dictionary attacks. The XML-RPC service cannot bypass such security plugins and even if you notice an unnatural amount of login attempts on your website attackers will not be able to break into your website’s backend.
What do you think about the WordPress botnet attacking other websites? Let us know in the comments below. Share your thoughts below or on our socials at Facebook and Twitter.