Cybercrime is evolving into structured operations, with organized workflows and repeatable attack models. Access remains a key lever, with third-party abuse witnessed throughout the month.…

Key TakeawaysPersistent threat access: A critical US agency breach occurred via a Cisco vulnerability, enabling attackers to maintain unauthorized network access for months.Malware deployment tactics:…

Key TakeawaysDeceptive methodologies: The UNC6692 threat actor leveraged Microsoft Teams impersonation to masquerade as legitimate internal IT support infrastructure.Malware deployment: The UNC6692 SNOW malware was…
Key TakeawaysSurfshark Dausos audit findings: Cure53 audit found no critical or high severity vulnerabilities within Dausos protocol scopeOut-of-scope risks identified: High severity issues found in…

Key TakeawaysExpanded investigation: Vercel uncovered additional compromised accounts linked to the recent Context.ai security incident.Secondary findings: During the investigation, a separate incident came to light,…

Key TakeawaysTreasury enforcement: The US Treasury imposed sanctions on Cambodian Senator Kok An and 28 affiliates operating a massive international cybercrime and extortion network.Financial impact:…

Key TakeawaysState-sponsored: A new China-aligned APT group deployed the GopherWhisper malware to execute a highly targeted Mongolian government cyberattack.Cyberespionage: The operators utilize a sophisticated arsenal…

Key TakeawaysAttack vector: Tropic Trooper utilized a trojanized SumatraPDF loader to deploy an AdaptixC2 Beacon agent against Asian targets.Covert C2 infrastructure: The operators engineered a…

Key TakeawaysSecurity vulnerability: An Apple bug fix addresses a flaw where deleted chat messages remained in the notification database.Forensic extraction: Law enforcement agencies exploited this…

Key TakeawaysMassive data exposure: A Rituals Cosmetics data breach may have compromised sensitive customer membership records, including personal contact details.Global customer impact: This cybersecurity incident…

Key TakeawaysAgency targeted: The French government data breach compromised ANTS, exposing sensitive personal identity and administrative records.Extensive exposure: A threat actor claims to possess 19…

Key TakeawaysNovel attack vector: A new NGate malware variant is distributed through a maliciously modified version of the legitimate HandyPay Android application.Financial data theft: The…

Key TakeawaysOrganizations sanctioned: The European Union imposed sanctions on Euromore and Pravfond for disinformation and hybrid warfare activities aligned with Russia.Asset freeze enacted: All EU-based…

Key TakeawaysData Collection: Meta tracking software captures employee keystrokes and mouse movements to train autonomous artificial intelligence models.Project MCI: The Model Capability Initiative gathers real-time…

Key TakeawaysSubstantial regulatory penalty: The Italian Data Protection Authority imposed a €12.5 million fine on Poste Italiane and Postepay for unauthorized data processing violations.Non-compliant application:…

Key TakeawaysCritical infrastructure compromise: The KelpDAO incident resulted in the unauthorized extraction of over $290 million in rsETH tokens from the decentralized finance (DeFi) protocol.Advanced…
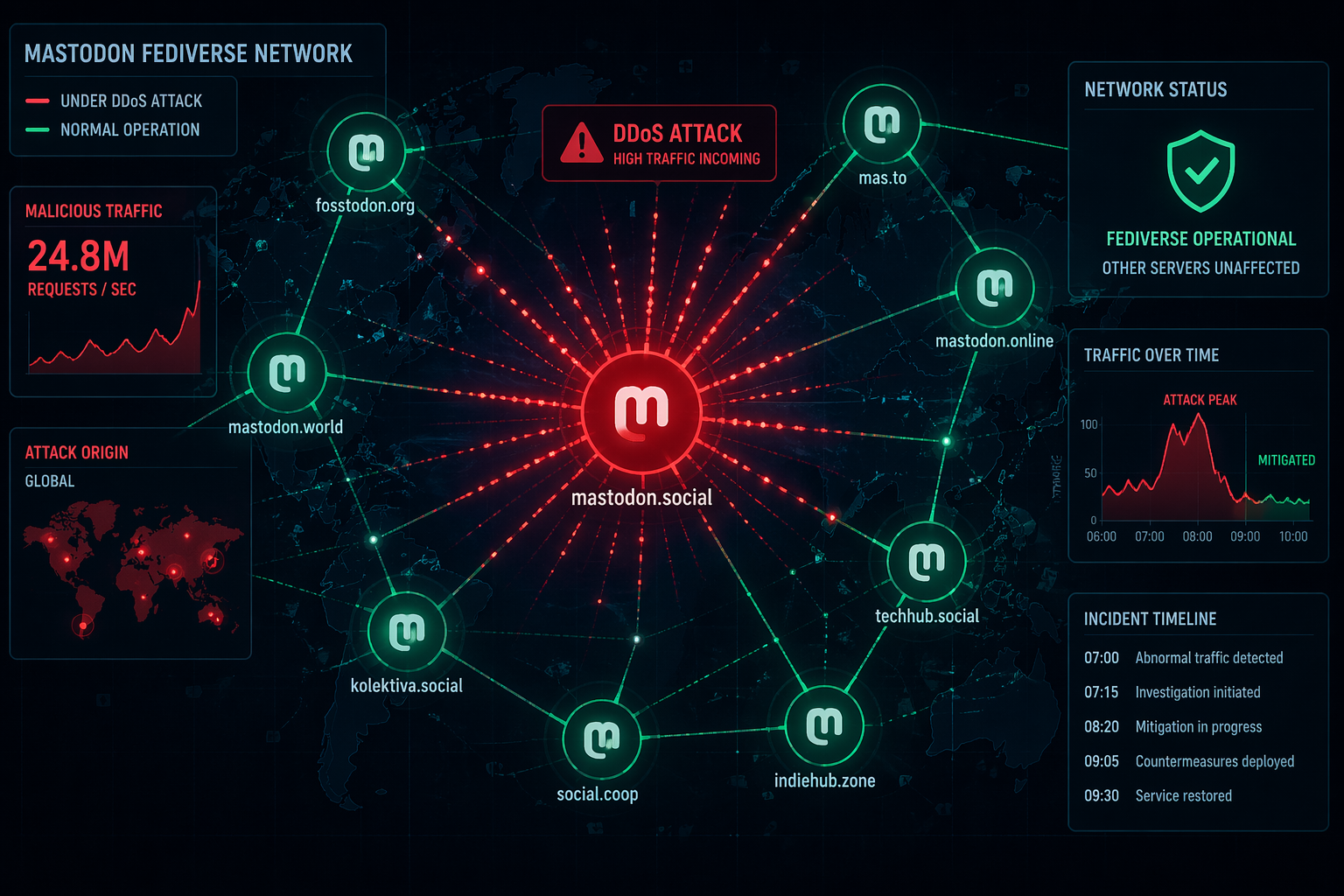
Key TakeawaysServer targeted: A massive Mastodon DDoS attack hit the platform's flagship server, causing a temporary “mastodon.social” outage and error messages early Monday.Limited impact: Because…

Key TakeawaysIdeological framework: The Palantir mini-manifesto summarizes CEO Alex Karp's book, defending Western technological superiority and aggressive military artificial intelligence integration.Corporate philosophy: The document sharply…

2024 NHS Ransomware Attack Still Causes Healthcare Disruption, 122 Patient Safety Incidents Recorded
Key TakeawaysSystem outages: More than 18 months later, the NHS ransomware attack continues to cause severe cyberattack healthcare disruption across South East London hospitals.Pathology delays:…