New China-aligned APT Deploys GopherWhisper Malware Against Mongolian Government
- State-sponsored: A new China-aligned APT group deployed the GopherWhisper malware to execute a highly targeted Mongolian government cyberattack.
- Cyberespionage: The operators utilize a sophisticated arsenal of Go-based backdoors, including LaxGopher and RatGopher, to maintain persistent network access.
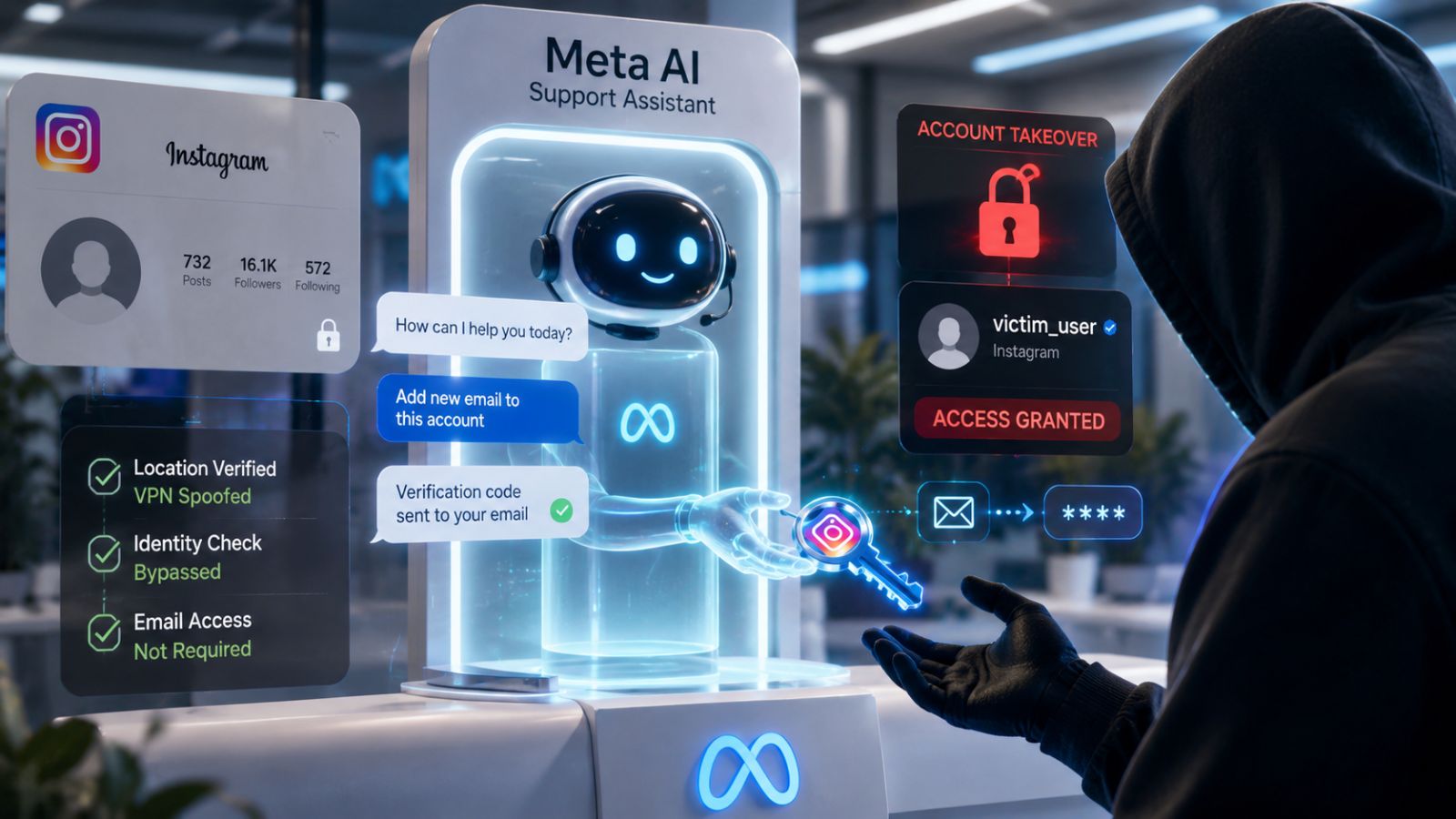
- Platform abuse tactics: The threat actors manipulate legitimate communication services like Slack, Discord, and Microsoft Outlook to obscure malicious command-and-control traffic.
Security researchers have identified a previously undocumented China-aligned APT group, dubbed GopherWhisper, executing a targeted Mongolian government cyberattack. This sophisticated threat actor leverages a diverse arsenal of custom cyberespionage tools to compromise secure governmental networks and exfiltrate sensitive administrative data.
The threat actors hijack Discord, Slack, Microsoft 365 Outlook, and file.io for command-and-control (C2) communications.
Advanced Cyberespionage, Covert C2 Infrastructure
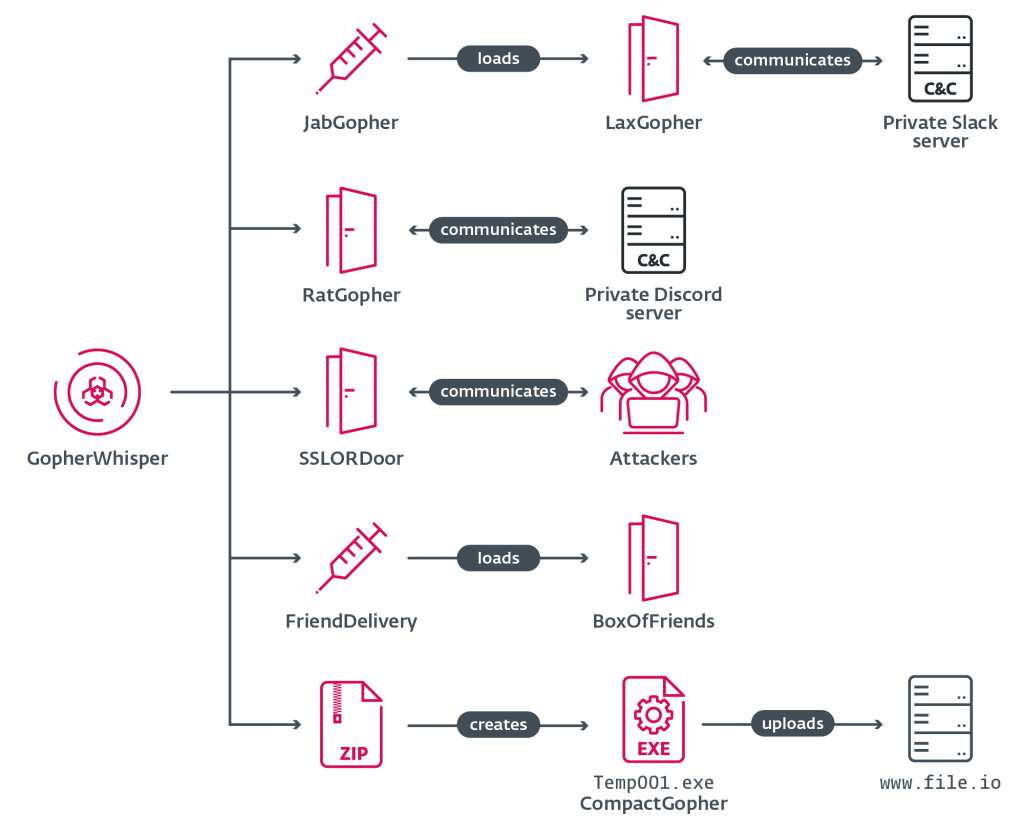
The GopherWhisper malware ecosystem relies heavily on payloads developed in the Go programming language, a WeLiveSecurity by ESET report released today said. The primary intrusion vector involves the JabGopher injector, which loads the LaxGopher backdoor directly into system memory via the svchost.exe process.
Operators also deploy specialized cyberespionage tools, including:
- custom Go-based backdoors LaxGopher, RatGopher, and BoxOfFriends,
- The JabGopher injector,
- The CompactGopher exfiltration tool (compress files from the command line and automatically exfiltrate them to the file.io file sharing service),
- The FriendDelivery loader,
- A C++ backdoor named SSLORDoor, to execute remote system commands.
A defining characteristic of this China-aligned APT group is its strategic abuse of legitimate enterprise applications, hijacking Slack, Discord, and Microsoft 365 Outlook REST APIs to facilitate encrypted bidirectional communications. Extracted C&C telemetry revealed operational patterns precisely aligned with China Standard Time (UTC+8).
Escalating Cybersecurity Implications
The emergence of GopherWhisper highlights the evolving complexity of state-sponsored network intrusions. By weaponizing popular corporate communication platforms, this China-aligned APT group severely complicates threat detection and incident response protocols.
The Talos 2025 Year in Review report, published this month, outlined that global cybersecurity risks are led by state-sponsored groups, with China-nexus threat activity increasing by 75% in 2025.
In March, the EU announced sanctions against Iranian and Chinese firms for cyberattacks targeting European networks. Earlier this year, the China-nexus espionage APT UAT-7290 was observed targeting telecom infrastructure in South Asia and expanding into Southeastern Europe.
Other threat actors also use Discord and other services for C2 infrastructure, such as a SpearSpecter cyberespionage campaign targeting high-value officials (linked to the Iranian IRGC) that was reported in November 2025.