Fake Android Apps Distributing Spyware, Linked to Italian Surveillance Vendor IPS
- Covert surveillance deployment: The Morpheus malware hides within fake Android spyware apps, tricking users into installing malicious updates.
- Vendor attribution identified: Evidence links this cyber espionage campaign to IPS Intelligence spyware, an Italian surveillance vendor.
- Severe access compromise: The malware exploits accessibility features and fakes biometric prompts to hijack WhatsApp accounts.
A sophisticated surveillance campaign distributes malware via fake updates of Android spyware apps, eventually hijacking the targets’ WhatsApp accounts. Digital rights organization Osservatorio Nessuno discovered the campaign and dubbed the malware “Morpheus,” linking it to IPS Intelligence spyware, an Italian surveillance vendor previously known for traditional network interception systems.
Morpheus Malware Linked to IPS
Morpheus relies on localized network manipulation and social engineering. In observed deployments, the victim received a deceptive SMS purporting to be from the Fastweb ISP, urging the installation of a network recovery application.
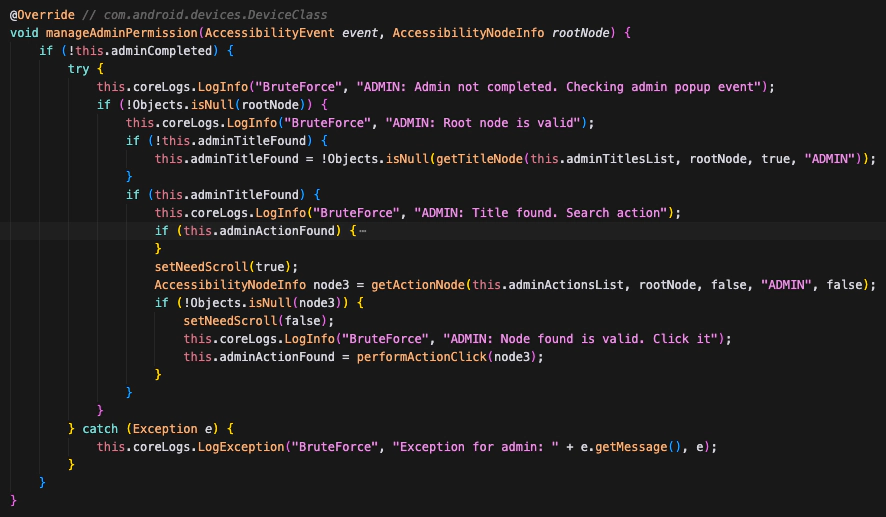
Once installed, the Morpheus malware exploits the Android operating system's built-in accessibility services, granting the app comprehensive visibility over screen telemetry and cross-application interactions. Its capabilities include:
- abusing accessibility features,
- automatically enabling the ADB daemon and issuing commands,
- disabling microphone and camera indicators,
- pairing additional WhatsApp devices,
- taking screenshots,
- recording audio and video.
Once active, Morpheus initiates a deceptive device reboot sequence and spoofs UI elements and interfaces. By tricking the user into providing biometric verification, the malware successfully links unauthorized companion devices to encrypted messaging platforms like WhatsApp.
“The spyware handles this scenario by triggering WhatsApp’s biometric request in the background and displaying a fake biometric UI on the overlay,” the report said. “When the person under surveillance taps the fingerprint sensor on the counterfeit dialog, they unknowingly grant the spyware full access to their WhatsApp account.”
Evolving Cybersecurity Threats
Technical forensic analysis attributes the Morpheus malware architecture to the IPS surveillance vendor. Reports suggest the campaign may be blacked by law enforcement and intelligence agencies.
Researchers identified distinct infrastructure overlaps, specifically command-and-control IP addresses registered to "IPS Intelligence Public Security," as well as source code artifacts referencing Italian cultural elements.
Recommendations for affected individuals include:
- Review recent activity
- Verify linked devices on messaging apps
- Audit Google account sessions
- Check battery usage – Spyware constantly running in the background can cause noticeable battery drain
The proliferation of these commercial espionage tools exacerbates cybersecurity threats to political activists and high-value targets globally.
Early this month, a WhatsApp spyware alert warned that a fake version of the Met-owned app linked to Italian surveillance provider SIO targets users in Italy, and hackers were hired to target the Android and iCloud devices of Egyptian and Lebanese journalists and activists.