Vercel Investigation Discovers More Compromised Accounts in Context.ai Breach and a Separate, Prior Breach
- Expanded investigation: Vercel uncovered additional compromised accounts linked to the recent Context.ai security incident.
- Secondary findings: During the investigation, a separate incident came to light, which seems to be unrelated to the AI tool breach.
- Authentication vulnerabilities: The ongoing security probe highlights severe OAuth risks surrounding third-party application authorizations.
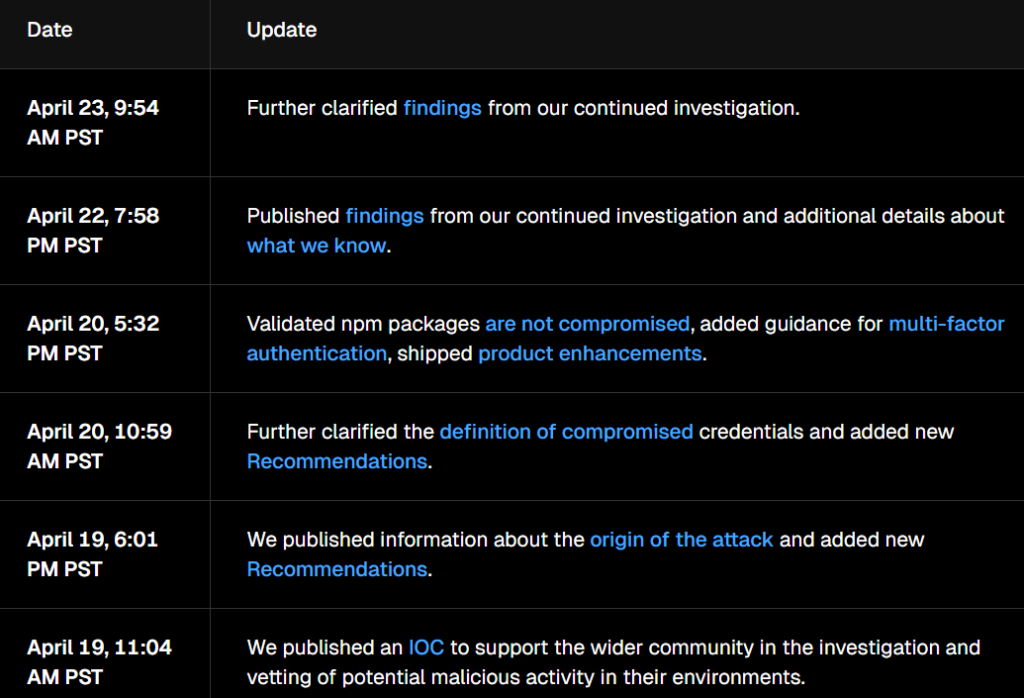
Vercel identified additional compromised accounts connected to the Context.ai-related breach during its ongoing security investigation. The infrastructure provider confirmed that the scope of the recent third-party network incident has widened, affecting more users than initially reported. Meanwhile, the company also found signs of an intrusion unrelated to the AI tool breach.
Expanding Scope of the Context.ai Breach
As Vercel broadened its investigation into the Context.ai breach, security teams identified a “small number” of additional compromised accounts, as well as a limited number of breached customer accounts that appear to be unrelated to the April 2026 incident.
“Based on our investigation to date, these compromises do not appear to have originated on Vercel systems,” the recent Vercel update said.
The company also suggested the AI tool’s “Google Workspace OAuth app was the subject of a broader compromise, potentially affecting its hundreds of users across many organizations.”
Hudson Rock cybercrime intelligence revealed that a Context.ai employee with sensitive access privileges was compromised in a February 2026 Lumma stealer infection, suggesting this could be a likely point of origin. The report added that Context.ai has only one infostealer infection on record, which is “this exact employee from a month prior to the incident.”
Cybersecurity Implications and Risks
Vercel is actively notifying newly identified victims and securing the affected accounts to prevent further unauthorized activity. Attackers allegedly exfiltrated sensitive organizational data from the compromised infrastructure, with a threat actor claiming to be part of ShinyHunters announcing a $2 million data sale.
Platform users should immediately revoke unrecognized third-party application access and rotate all administrative security tokens. Implementing stringent access controls and continuous monitoring remains the most effective defense against subsequent supply chain attacks.
Over the past months, several security incidents have been attributed to third parties and supply chain compromises. Last week, retail giant Inditex reported a third-party data breach, Rockstar Games reportedly leaked analytics data via a prior Anodot security incident, and a Hallmark breach exposed 1.7 million customers due to a Salesforce compromise.