New NGate Malware Variant Discovered in Trojanized NFC App Stealing Payment Card PINs
- Novel attack vector: A new NGate malware variant is distributed through a maliciously modified version of the legitimate HandyPay Android application.
- Financial data theft: The trojanized NFC app captures payment card PINs and relays NFC data to threat actors for unauthorized ATM cash withdrawals.
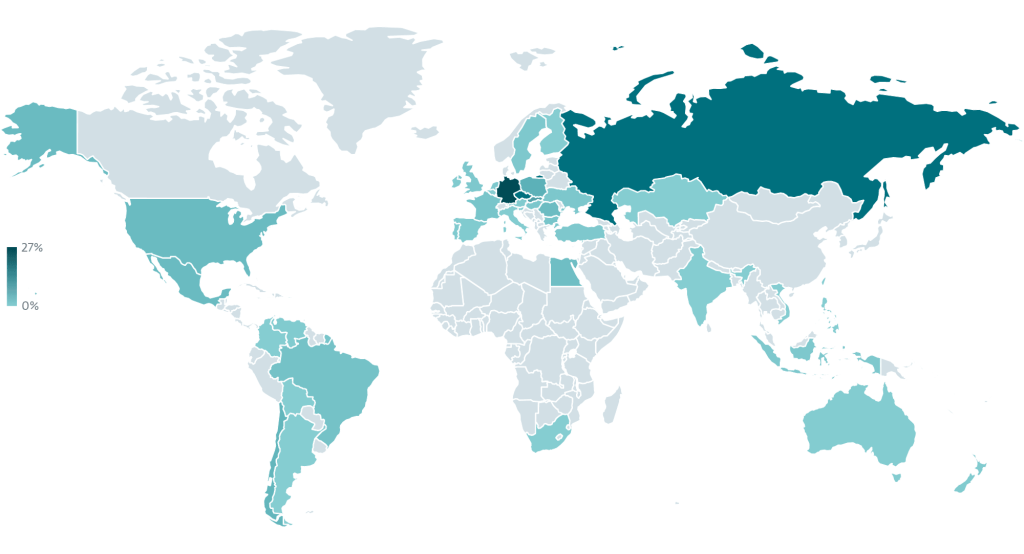
- Targeted geographic campaign: Active since November 2025, this operation targets Brazilian users via fake lottery websites and counterfeit Google Play download pages.
A sophisticated new NGate malware variant is actively targeting Android users. Instead of relying on traditional open-source tools, this malicious campaign leverages a trojanized NFC app to execute unauthorized financial transactions and steal payment card PINs.
Cybersecurity researchers at ESET have identified that threat actors facilitate this operation by abusing HandyPay, a legitimate Android application originally designed to relay NFC data, and injecting it with malicious code.
HandyPay Abuse and Malware Distribution
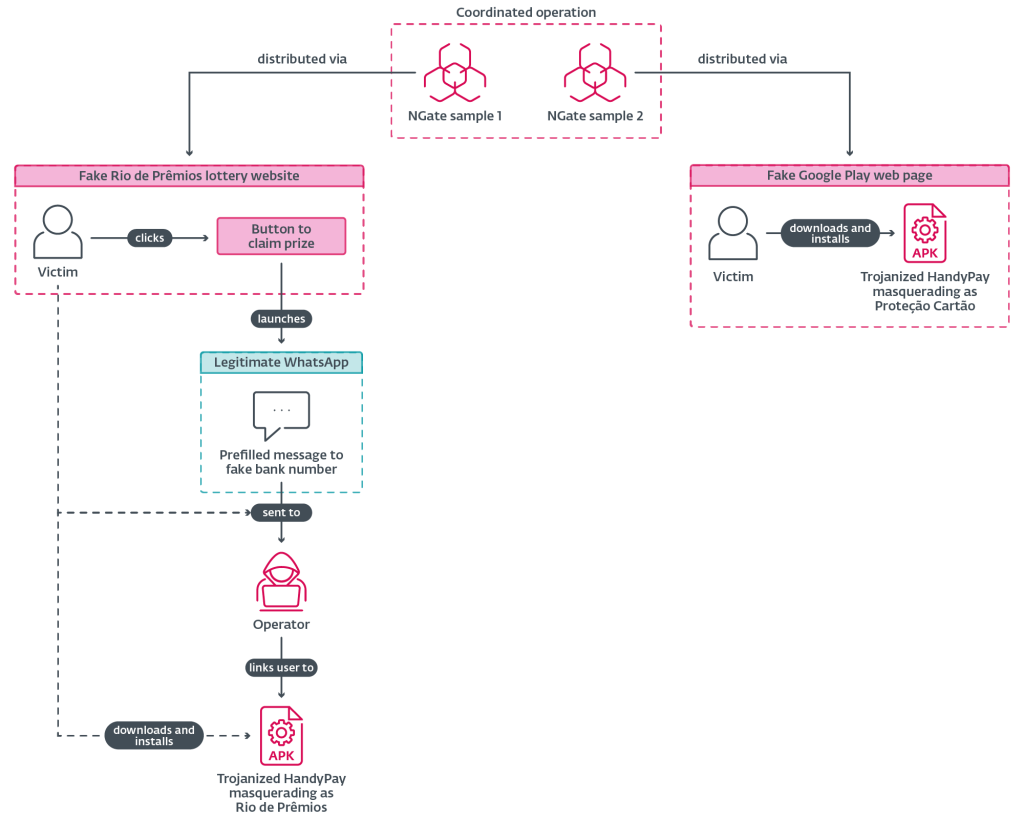
The NGate campaign currently targets users in Brazil and distributes the malware through two primary channels. Victims are lured via a fraudulent website impersonating the Rio de Prêmios lottery or through a fake Google Play landing page offering a counterfeit card protection application named Proteção Cartão.
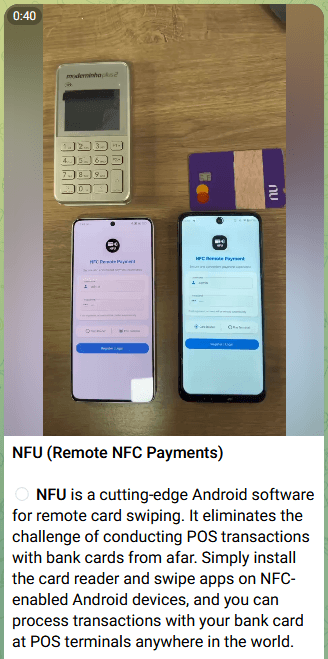
The first NGate attacks used the open-source NFCGate tool to transfer NFC data. Since then, several similar malware-as-a-service (MaaS) offerings have emerged, including NFU Pay and TX‑NFC.
Once manually installed, the software prompts victims to input their payment card PINs and tap their physical cards against their NFC-enabled smartphones.
The NGate malware variant subsequently relays the captured NFC traffic directly to an attacker-controlled device. This functionality allows cybercriminals to emulate the victim's card, perform contactless ATM cash-outs, and execute fraudulent retail payments.
Furthermore, the application explicitly exfiltrates the stolen PINs over HTTP to an external command-and-control (C2) server. The ESET report indicates that the perpetrators likely used generative AI to assist in writing this code, as evidenced by emojis left in the logs.
Cybersecurity Threats
This evolution in digital banking attacks highlights escalating cybersecurity threats within the mobile ecosystem, demonstrating how threat actors continuously refine their tactics to bypass standard endpoint defenses, exploit device hardware, and effectively monetize compromised hardware.
In late March, a novel DeepLoad malware campaign leveraged the ClickFix technique and possible AI-backed evasion.
A February 2025 Fortinet FortiGuard Labs report revealed that a banking trojan campaign targeted Brazilian Windows users, while a new Brazilian malware, dubbed Caminho Loader, was observed leveraging steganography in a global campaign deploying Remcos RAT, XWorm, and Katz Stealer.