Cybersecurity News Roundup: From Roblox Cheats To Enterprise Breaches, Small Actions Led To Big Compromises
Cybercrime is evolving into structured operations, with organized workflows and repeatable attack models. Access remains a key lever, with third-party abuse witnessed throughout the month.
Law enforcement is tightening its grip, with guilty pleas, arrests, and coordinated crackdowns as cybercrime operations mature into multi-million dollar ecosystems.
Palantir Manifesto Pushes Tech Toward Defense-Driven AI
Palantir has released a 22-point document outlining its corporate ideology, drawing directly from CEO Alex Karp’s book The Technological Republic. The framework positions the technology sector as a key pillar in supporting state power, particularly in strengthening Western geopolitical influence. It calls for a shift away from consumer-focused innovation, arguing that software development should instead prioritize national security, economic resilience, and public safety. The document also promotes faster development of military AI systems, warning that geopolitical rivals are already advancing similar capabilities.
Europol Uses OSINT Tools to Trace Deported Ukrainian Children
Europol coordinated a multinational operation using open-source intelligence techniques to identify children forcibly transferred from occupied Ukrainian regions. Investigators from 18 countries worked together in The Hague, combining digital tools and data analysis to track movements across borders. The team compiled intelligence on 45 children, mapping transportation routes, identifying associated individuals, and tracing possible locations. Analysts also examined online platforms, records, and visual data to uncover links to camps, facilities, and networks involved in the transfers.
Scattered Spider Hacker Pleads Guilty In $8M Crypto Theft Scheme
A 24-year-old British national, Tyler Robert Buchanan, pleaded guilty in a U.S. federal court for his role in a cybercrime campaign that stole at least $8 million in cryptocurrency. Prosecutors linked him to the Scattered Spider collective, a loosely organized group known for sophisticated social engineering attacks. Buchanan admitted to conspiracy to commit wire fraud and aggravated identity theft after authorities accused the group of running large-scale phishing operations targeting employees across multiple companies. The attackers used SMS phishing campaigns to trick victims into entering credentials on spoofed websites, which were then used to access corporate systems and digital assets. Victims included major firms such as MGM Resorts, Coinbase, Twilio, Mailchimp, and LastPass.
Lazarus Hackers Use Multi-Stage Attack to Steal $290 Million From KelpDAO
KelpDAO was hit by a coordinated multi-stage attack on April 19 that led to the theft of roughly $290 million in cryptocurrency. Attackers first compromised cross-chain verification nodes tied to decentralized verifier networks, allowing them to inject fraudulent transaction data into the system. At the same time, they launched a distributed denial-of-service attack on healthy nodes, forcing the protocol to rely on the already compromised infrastructure. This combination enabled the network to validate malicious cross-chain messages as legitimate transactions. Around 116,500 rsETH tokens were drained and later routed through Tornado Cash to obscure fund movement.
Ransomware Negotiator Pleads Guilty To Aiding BlackCat Attack
A U.S.-based ransomware negotiator has pleaded guilty to secretly assisting the BlackCat ransomware gang in carrying out attacks and increasing ransom payouts. Angelo Martino, 41, admitted to sharing confidential client information, including insurance limits and negotiation strategies, with attackers while working on behalf of victims in 2023. The insider access allowed BlackCat operators to demand higher ransoms, with Martino receiving financial compensation in return. He also collaborated with two other incident responders to deploy ransomware across multiple U.S. targets, including one case that resulted in a $1.2 million Bitcoin payment.
Poste Italiane And Postepay Fined Over Unauthorized Data Processing
Italy’s data protection authority fined Poste Italiane and its subsidiary, Postepay, €12.5 million for unlawfully processing the personal data of millions of users via their mobile applications. The investigation found that fraud detection and anti-malware features collected excessive device and behavioral data beyond what was necessary for security purposes. Regulators also cited failures to properly inform users and the absence of required data protection impact assessments under GDPR rules. Authorities concluded that the data handling practices did not meet proportionality and transparency standards.
EU Sanctions Euromore And Pravfond Over Disinformation
The European Union has imposed sanctions on Euromore and Pravfond for their roles in distributing pro-Kremlin narratives and conducting coordinated disinformation campaigns. Authorities linked both organizations to Russian state interests and accused them of targeting audiences across EU member states and Ukraine. Euromore operated as a media platform amplifying Kremlin-aligned messaging, while Pravfond allegedly funded and supported influence networks promoting false narratives. Under the sanctions, all EU-based assets tied to these entities have been frozen, and financial support from EU individuals and businesses is now prohibited.
France Investigates ANTS Breach As Citizen Data Circulates Online
French authorities have launched an investigation after a cyber incident at ANTS led to the exposure of sensitive citizen data from its online services platform. The breach, identified on April 15, involved unauthorized access to personal records tied to identity and administrative services. Shortly after, a threat actor claimed to be offering a large dataset for sale on underground forums, alleging it contains millions of user records. While officials have not confirmed the scale of the leak, they acknowledged that data from both private individuals and professional accounts may have been accessed.
A Bug That Let Deleted Signal Messages Linger Inside iPhone Notifications
Apple fixed a flaw where deleted chat messages from apps like Signal could remain stored in the iPhone’s notification system. The issue meant message previews were not fully cleared and continued to exist in internal logs even after chats disappeared. These leftover notifications could be recovered using forensic tools, exposing fragments of conversations users believed were erased. The problem was tied to how iOS handled notification data rather than any weakness in encrypted messaging itself. Apple has now patched the bug to ensure notifications marked for deletion are completely removed.
Roblox Cheat Download Opened the Door to a $2M Vercel Breach
A Vercel-linked breach was traced back to an employee at AI startup Context.ai who unknowingly installed infostealer malware while downloading a Roblox cheat tool. The malware harvested saved browser credentials, including access tokens and login data tied to enterprise systems. Weeks later, attackers used those stolen credentials to compromise Context.ai and extract OAuth tokens tied to its customers. One of those tokens provided access to a Vercel employee’s Google Workspace account, allowing attackers to move deeper into internal systems. From there, they accessed customer environment variables that were not initially flagged as sensitive. The stolen data was later advertised for sale online with a reported price of $2 million.
US Sanctions Cambodian Senator for Trafficking Network
The U.S. Treasury has sanctioned Cambodian senator Kok An and 28 linked individuals and entities tied to a sprawling fraud network operating out of casino-backed compounds. Authorities say these sites ran large-scale crypto romance scams that extracted funds from victims worldwide through manipulated investment schemes. What sets this action apart is the formal linking of these fraud hubs to organized human trafficking, where workers were lured with fake job offers and forced to run scams under coercion. Victims inside the compounds reportedly had passports seized and faced threats or violence if they resisted.
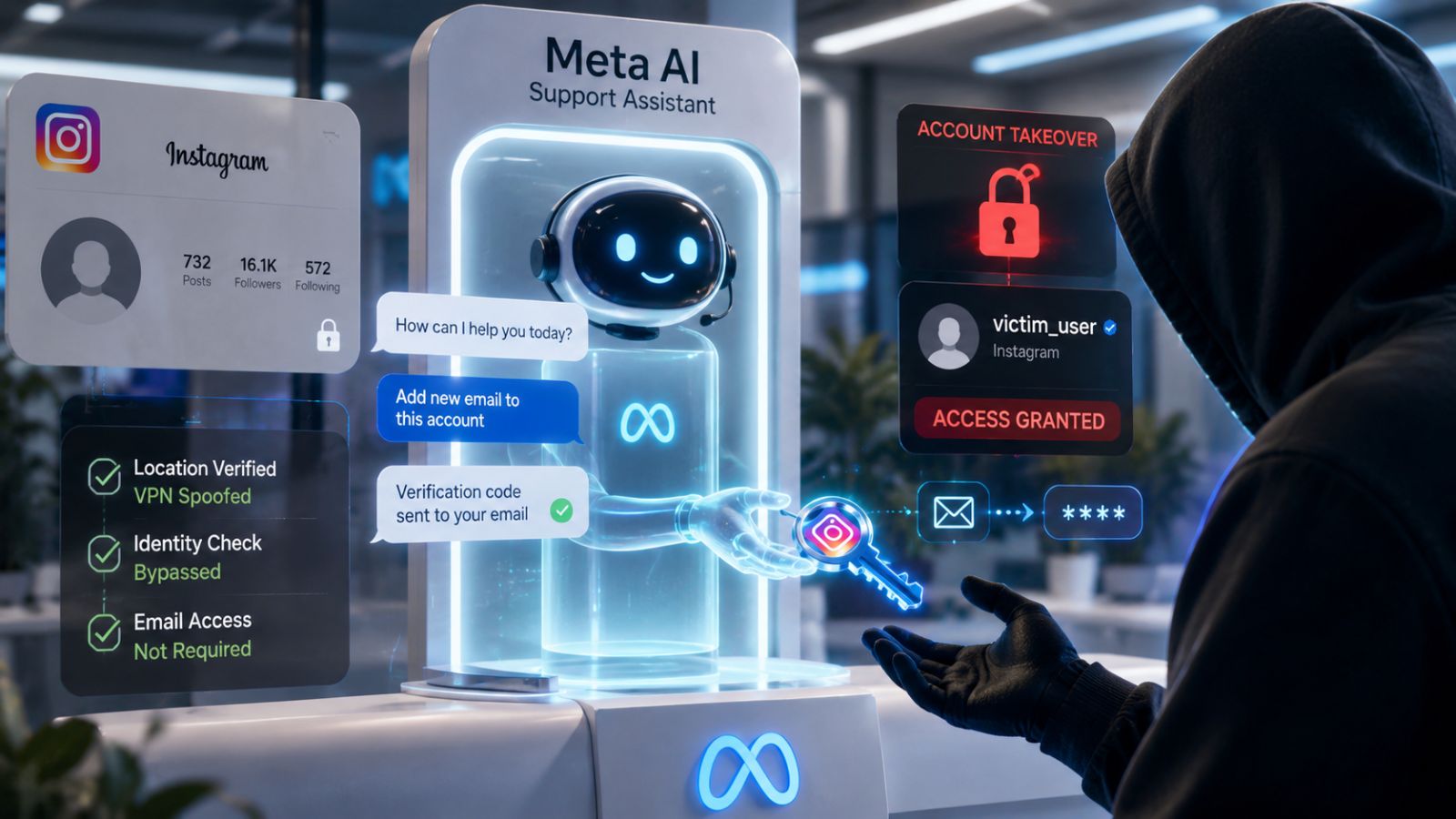
UNC6692 Poses as Company IT Support on Microsoft Teams
A campaign tracked as UNC6692 shows attackers continuing to rely on impersonation tactics, this time posing as internal IT helpdesk staff on Microsoft Teams to breach corporate environments. Employees were first flooded with spam emails before receiving follow-up messages from accounts mimicking support teams, urging them to install a supposed fix. The approach reflects a broader pattern where attackers exploit trusted workplace roles and communication platforms to lower suspicion and gain initial access. In this case, victims installed malicious files that deployed the SNOW malware suite, enabling persistent access and data movement within networks.
NIST Launches OT Visibility Project to Improve Critical Infrastructure Threat Detection
NIST is launching a project to improve visibility across operational technology environments used in critical infrastructure systems. Many organizations do not have a complete inventory of devices or clear insight into how systems communicate within OT networks. This lack of visibility has made it harder to detect unauthorized access and suspicious activity. Threat actors have used these gaps to move between IT and OT systems and maintain access over time. The project will focus on helping organizations identify assets, monitor network activity, and understand system interactions more clearly. The effort is intended to support earlier detection of intrusions and reduce the risk of prolonged unauthorized access.
Europol Reveals Victims as Global Child Abuse Network Investigations Deepen
Europol has identified 12 children during a coordinated victim identification taskforce targeting child sexual abuse cases. Specialists from 31 countries, alongside Europol and INTERPOL, analyzed 317 datasets containing abuse material to uncover identifying clues. The effort generated over 200 leads, which have been passed to national authorities to support ongoing investigations and locate victims. By linking digital evidence to real-world locations and individuals, investigators are able to move cases forward and intervene in situations where abuse may still be ongoing. The process also strengthens cases against offenders by building intelligence packages that can lead to arrests.
Canada Sees First Arrests In SMS Blaster Phishing Operation
Canadian police have made their first arrests in a case involving the use of mobile “SMS blasters,” devices that impersonate legitimate cell towers to deliver large-scale phishing messages. The investigation, launched in Toronto in late 2025, uncovered equipment capable of forcing nearby phones to connect to rogue networks, allowing attackers to send fraudulent texts posing as banks or government services. Authorities linked the devices to over 13 million network disruptions, which at times interfered with normal connectivity and could affect access to emergency services. Multiple units and supporting hardware were seized.
Norway To Enforce Social Media Age Limit and Mandatory Verification
Norway’s government plans to introduce legislation setting a minimum age of 16 for social media access, with enforcement tied to the year a child turns 16. The proposed law shifts responsibility to technology companies, requiring them to implement age verification systems at login rather than relying on user honesty. Officials say the move is aimed at limiting children’s exposure to algorithm-driven platforms while ensuring equal access across age cohorts. The legislation will align with broader European efforts, including the EU’s Digital Services Act, which pushes platforms to enforce age restrictions more strictly. If passed, the law will be implemented in phases.
Deleted But Not Gone: Where Data Privacy Stands
Child protection campaigns are at an all-time high, with governments, law enforcement, and cross-border coordination working hand in hand. Norway’s move toward mandatory age verification signals stronger control over child safety. Europol, alongside international partners, is driving enormous progress in child protection.
Palantir’s push signals a defense-driven AI ecosystem, where technology development is aligned with national security and geopolitical priorities. While Italy fined Poste Italiane for over-collecting user data, and Apple’s flaw showed that even deleted data may not be fully gone, where do data processing and digital safety really stand?