Tropic Trooper Deploys AdaptixC2 and Custom Beacon Listener
- Attack vector: Tropic Trooper utilized a trojanized SumatraPDF loader to deploy an AdaptixC2 Beacon agent against Asian targets.
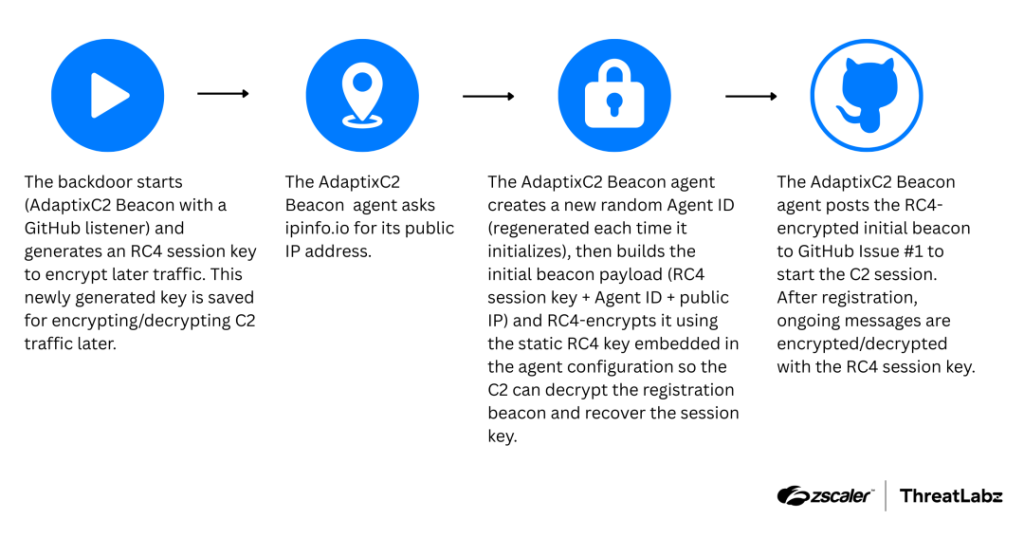
- Covert C2 infrastructure: The operators engineered a custom beacon listener that leverages GitHub repositories for encrypted bidirectional communications.
- Persistent remote access: Following initial exploitation, the cyber espionage group pivots to Visual Studio (VS) Code tunnels to maintain administrative control.
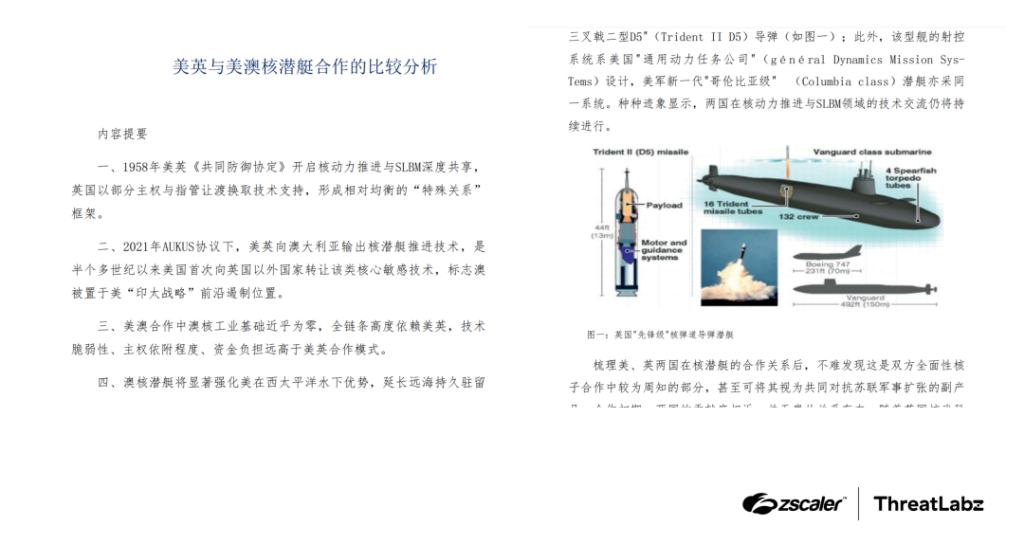
A sophisticated cyber espionage campaign orchestrated by the threat actor dubbed Tropic Trooper (also known as Earth Centaur and Pirate Panda) utilizes military-themed lures to deploy advanced malware, demonstrating a significant evolution in their operational capabilities and infrastructure. The attackers engineered a custom beacon listener that abuses GitHub for command-and-control (C2) and VS Code for remote access.
Discovered in March 2026 by ZScaler security researchers, this operation targets Chinese-speaking individuals across Taiwan, South Korea, and Japan.
Tropic Trooper AdaptixC2 Implementation
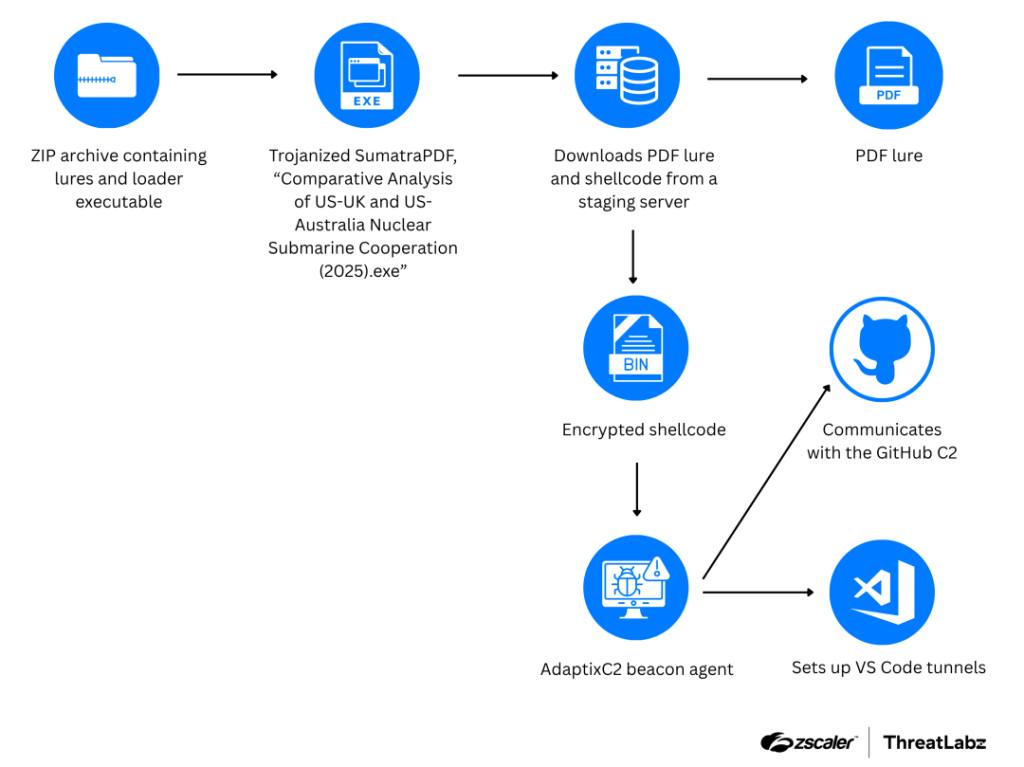
The attack sequence begins with a malicious ZIP archive containing trojanized military documents and legitimate-looking decoys. Specifically, the threat actors modified the open-source SumatraPDF reader using a shellcode loader that closely resembles the TOSHIS loader, the ZScaler ThreatLabz report said.
Once a victim executes the disguised executable, the loader hijacks the control flow by overwriting the _security_init_cookie function and then downloads and executes a second-stage payload directly in memory.
The primary payload in this campaign is the open-source AdaptixC2 Beacon agent, which retrieves its external IP address and establishes a session by posting encrypted data to GitHub Issues. The malware utilizes a 16-byte RC4 session key to encrypt all C2 traffic.
The threat actors execute a series of reconnaissance commands. When they identify a target of interest, the attackers deploy Visual Studio (VS) Code to establish remote access to the compromised network.
Cyberespionge Risks
This complex Tropic Trooper AdaptixC2 attack chain highlights the severe operational risks facing targeted organizations and the continuous advancement of cyberespionage techniques.
“The staging server involved in this attack also hosted CobaltStrike Beacon and an EntryShell backdoor,” the report added, which were previously associated with Tropic Trooper.
In March, a GitHub phishing campaign targeted developers with fake VS Code alerts urging them to patch fabricated CVEs.
In November 2025, Tomiris APT targeted diplomats using AdaptixC2. One month later, an Evasive Panda APT cyberespionage campaign targeting Asia poisoned DNS requests to deliver MgBot.