When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.
Can a VPN Be Hacked?
Think your VPN makes you untouchable online? Well, think again. While VPNs are great for boosting privacy and security, not all of them are created equal, especially the free ones. Some can actually get hacked themselves, putting your data at serious risk.
This article will discuss how malicious actors can hack a VPN, the risks you should be aware of, and the steps to take if your VPN gets hacked. After that, we shall look at the best VPNs to protect yourself from hackers.
Key Takeaways
- VPN Hacking Explained: A VPN can be hacked through weak protocols, stolen encryption keys, server breaches, software bugs, or user error, compromising your privacy and data.
- Common Attack Methods: These include cryptographic attacks, DNS/WebRTC/IP leaks, hijacked VPN servers, and phishing. Even your own device or poor password hygiene can be the entry point.
- How to Stay Safe: Use VPNs with AES-256 encryption, secure protocols like WireGuard or OpenVPN, a strict no-logs policy, kill switches, and regular security audits. Avoid free VPNs and always update your software.
How Can a VPN Get Hacked?
A VPN can get hacked by exploiting vulnerabilities in the protocol, stealing encryption keys, and compromising the backend servers. Hackers can also decrypt your encrypted data using brute force methods or capture leaked information outside the VPN tunnel.
Let’s discuss some common ways in which hackers can get to your VPN.
1. Exploits and Vulnerabilities in the VPN’s Protocol
A VPN protocol is a set of rules that specify how your data routes between your device and the VPN’s server. In other words, a VPN protocol determines how the VPN tunnel is formed. Also, consumer VPNs let you choose between protocols like WireGuard, OpenVPN, L2TP/IPsec, and more. However, all protocols are not the same, and each has its pros and cons.
Some VPN protocols are reported to have confirmed vulnerabilities and an obscure code base. Hackers can exploit a protocol’s vulnerability and gain access to your information. PPTP is one such outdated protocol that is relatively easy to hack. In fact, it has reportedly been cracked by the US NSA (National Security Agency).
Similarly, L2TP/IPSec is suspected of having hidden exploits present in its closed-source code due to potential collaboration between its parent company, Microsoft, and the NSA. So, it may potentially be vulnerable to man-in-the-middle attacks. In this attack, the attacker places himself between two parties and intercepts/alters their communication.
Generally, protocols with an open code base, meaning its code is public, are more secure than those with a closed code base. OpenVPN is a prime example of a highly secure protocol, as it has been extensively tested by the community.
2. Cryptographic Attacks
VPNs that use older and breakable encryption ciphers are susceptible to cryptographic attacks, in which hackers can easily decrypt your data after intercepting it.
But what are cryptographic attacks? To help you understand, let’s discuss how VPNs mask your data. VPNs hide your Web traffic by encrypting it, which is a process that converts the data into unreadable code. This is done using algorithms called encryption ciphers, such as Blowfish, ChaCha20, AES, and more.
Overall, a cryptographic attack aims to break the encryption and decrypt your data to read the contents inside it. When that happens, your security cover will be blown, and the hacker will be able to see all your Internet activity.
That being said, not all VPN encryption ciphers are the same. In this scenario, the key length is a major differentiating factor. Basically, the key length of a cipher refers to the number of bits present in its encryption key, and bigger keys mean better security. For example, AES-256-bit encryption has a key length of 256 bits and is considered unbreakable.
As technology becomes more advanced, it takes a shorter amount of time to break encryption ciphers and hash functions. For instance, the Blowfish cipher is vulnerable to birthday attacks, while the SHA-1 hash function can be broken cryptographically.
3. VPN Leaks (WebRTC, DNS, IP)
A hacker does not always have to break the encryption or hijack the VPN’s servers on the backend to gain access to your information. Rather, a hacker can also intercept leaked data outside the encrypted tunnel.
There are various types of VPN leaks that can expose your data. For example, in IPv6 leaks, the VPN fails to encrypt IPv6 requests. Similarly, during a WebRTC leak, the VPN fails to reroute the WebRTC connections properly.
Also, if there are issues with your VPN kill switch, your browser activity can briefly be exposed. So, the only prevention against such data leaks is to use the best VPN with a high level of security.
4. Compromising VPN Servers
In some cases, hackers can also compromise VPN servers through the backend. This can happen due to multiple vulnerabilities. For instance, the server’s login credentials might be weak. Similarly, it may also have configuration issues.
Once hackers gain access to the backend servers, they can access all the information you have willingly or unwillingly given to the VPN provider. This includes your credit card info, purchase history, billing address, name, and previous browsing activity. If the server remains compromised, your future internet activities will also stay exposed.
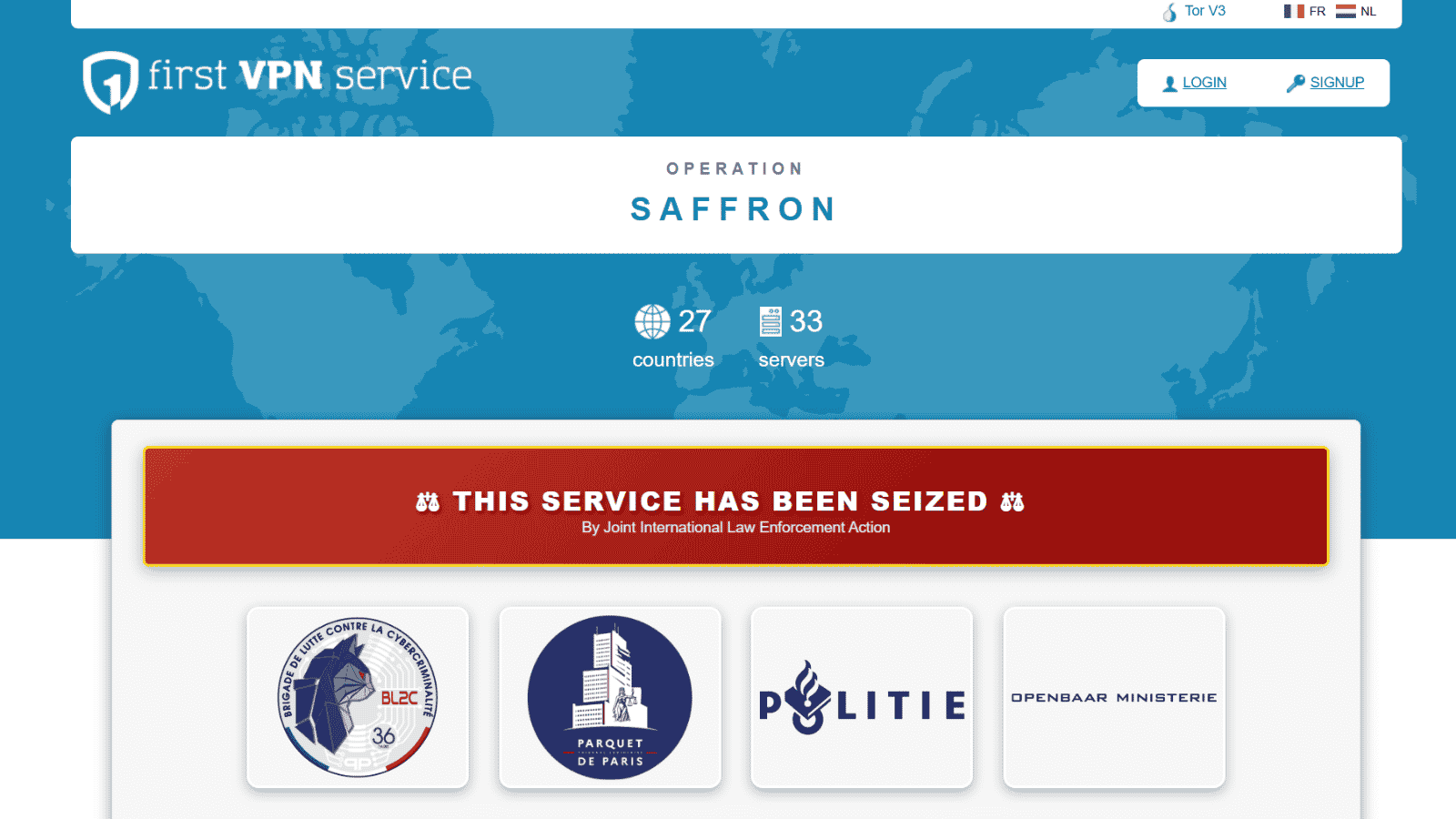
The worst part is that such attacks are quite common. In 2021, ChatVPN, SuperVPN, and GeckoVPN got their servers hacked. This resulted in the information of over 21 million users becoming public.
Similarly, in 2018, NordVPN also got its servers compromised. However, NordVPN assured that the users were safe because the server did not contain sensitive information or activity logs. They further clarified that this happened because one of Nord’s data center providers left the remote management system unprotected.
Now you must be wondering why we still recommend it. It is because NordVPN did not hide away from this fact; rather, they acknowledged and faced it. They were completely transparent with their shortcoming, and this is what is essential to look out for in a VPN.
5. Stolen Encryption Keys
Sometimes, hackers may manage to steal your encryption keys. These keys are used by encryption ciphers or cryptographic algorithms to encrypt/decrypt data securely. Using stolen keys, hackers can easily decrypt your data after intercepting your traffic.
Nowadays, capable VPNs use a feature called PFS (perfect forward secrecy). It ensures that the VPN client and server use unique symmetric keys. These keys are independently generated on either side and are never exchanged.
Furthermore, once a connection has closed, the previous keys become obsolete, and a unique key gets generated for every new session. So, even if hackers manage to get access to both keys in a single session, which is very unlikely, your future VPN sessions stay unaffected.
6. Hacking the VPN Software
When people talk about hacking a VPN, one possible route is exploiting vulnerabilities in the VPN software itself. Just like any other app, VPNs can have bugs, and if those bugs aren’t patched quickly, hackers can potentially use them to gain access to your device or redirect your traffic.
This is especially a concern with unknown or shady VPN providers, particularly free ones that don’t invest in regular updates. In fact, some free VPN apps have even been found bundled with malware. That’s why choosing a VPN with a good security track record and consistent software updates is more than just smart, it’s essential.
7. Hacking Through the User
Here’s the cold, hard truth: the weakest point in any VPN setup is usually... you. If your device is already infected with malware, or if you fall for a phishing email and give up your credentials, the VPN can’t protect you.
Hackers love exploiting human behavior, clicking suspicious links, downloading sketchy apps, or using the same weak password everywhere. VPNs are powerful tools, but they’re not magic shields. If your endpoint is compromised, your privacy is already gone, VPN or not.
What Will Happen If Your VPN Gets Hacked?
If your VPN gets hacked, hackers can access your personal information and steal it. This can be used for identity theft or other types of fraud. They may also be able to track your browsing activity and infect you with malware.
Here’s a list of the most common risks of a VPN hack.
- Your Activities Can Be Spied On: If a VPN gets compromised on the backend, hackers can gain access to the server. When that happens, they will be able to monitor your IP address, track browsing activity, and see previous data if it has been logged.
- Hackers Can Steal Your Personal Data: This remains one of the biggest and most damaging risks. Some hackers are capable of causing long-lasting harm to an individual by stealing their identity. They can use your info coupled with social engineering tactics to harm your reputation and commit bank fraud and other crimes online.
- You Can Be Targeted with Phishing and Malware: A hacked VPN doesn’t automatically make your device vulnerable. However, if you use a compromised VPN on an unsecured public WiFi, you may be susceptible to man-in-the-middle attacks. The hackers can redirect you to malicious websites or fake websites and false login forms. This can make you vulnerable to phishing attacks.
- You Can Experience DDoS Attacks: In such attacks, hackers send an overwhelming number of data packets, far more than a server connection is capable of handling, resulting in massive slowdowns. Your IP is among the most vital pieces of information in this scenario. If a hacker knows your real IP, they can track your location and even hit you with DDoS attacks to make your Internet connection unresponsive.
How to Know If Your VPN Is Hacked?
Just because you’re using a VPN doesn’t mean you’re 100% immune to cyber threats. If your VPN is compromised, there may be subtle (and sometimes alarming) signs. The key is to spot them early before they lead to serious privacy risks. Here's a breakdown of what to look out for:
What to Do If Your VPN Is Hacked?
If your VPN is hacked, you should immediately start securing your device to protect yourself. First, disconnect from the VPN server immediately. Once that’s done, you can uninstall the client/app from your device and assess your device’s security.
Let’s take a look at the necessary steps and discuss why they are important.
1. Disconnect the VPN
This should be your very first response if you suspect that your VPN is hacked. You would not want the hackers to intercept more of your traffic or find more information about you. Once you have disconnected from a hacked VPN (learn how to disconnect your VPN safely), you’re no longer on a compromised server and the hacker cannot intercept your future activity.
2. Uninstall the VPN Client
In some cases, especially when the hack is invasive, you will want to uninstall the VPN client. Since you may not be able to figure out the true extent of the hack, it is safe to uninstall the VPN client/app from your device if you suspect it’s hacked.
3. Never Use the Same VPN Credentials Again
If you notice new and unknown device logins on your VPN account, it can mean that your login details have been compromised. Hackers often leak databases after gaining access to them, which results in a wide number of user login/passwords becoming public. Make sure that you’re not using the same password on all your important accounts. Also, never use the same credentials again on any service.
4. Change All Passwords Saved on Your Device
You may think that a simple VPN hack won’t expose passwords saved on your device. That may be true, but you never really know the true extent of the hack. For all you know, your device may have already been infected with a malicious tool. It would be safer to immediately change all your passwords and turn on 2FA authentication for added security.
5. Assess the Extent of the Compromise
Assessing the extent of the compromise can help you determine the further steps that you should take. For instance, your device may have been infected with malware via an unsecure public WiFi because your VPN was not working as it should have. In that case, you may want to do a full device scan, or reinstall the operating system to completely secure yourself.
6. Switch to a Better VPN Provider
Eventually, you’ll want to switch to a VPN provider known for strong security and reliability. We highly recommend NordVPN as it’s consistently rated among the best for privacy, speed, and security, backed by independent audits.
For a comprehensive overview of top VPN options, check out our detailed Best VPN Guide to help you choose the right service for your needs.
7. Avoid Free VPNs
Free VPNs often cut corners on security and may even log or sell your data. A small monthly investment in a premium service can go a long way in protecting your privacy.
8. Regularly Test for Leaks
Once you're back online with a new VPN, check for vulnerabilities using tools like ipleak.net. Regular testing helps ensure your IP address, DNS requests, and WebRTC data are truly secure.
Best VPNs for Protection From Hackers
To protect yourself from hackers, you need to use a VPN that offers secure protocols and unbreakable encryption. You should also make sure that it has a no-logging policy. It may be surprising to know that hackers also use high-security VPNs to hide their identities.
Let’s take a look at the best VPNs for ethical hackers and regular users alike.
1. NordVPN
NordVPN is a strong and trusted VPN that keeps you safe online. It protects you from hackers, phishing, malware, and IP leaks. Whether you're using public Wi-Fi or browsing at home, NordVPN hides your data and keeps your internet private. It's easy to use, fast, and works on all your device, giving you peace of mind every day.
Save upto 70% on NordVPN’s 2-year plan – now priced at $3.39/month ($81.36 in total). 30-day money-back guarantees available!
Key Features that Prevent You From Hacking
- Threat Protection and Post-Quantum Encryption: Blocks malicious websites, trackers, and malware, even when the VPN is off.
- Kill Switch: Automatically cuts Internet if the VPN drops, preventing accidental exposure.
- Dark Web Monitor: Alerts you if your credentials are found in data leaks.
- Meshnet: Create secure private tunnels between your devices without exposing them to the public Internet.
- NordPass Integration: Manage and store strong, unique passwords to avoid credential reuse.
- Obfuscated Servers: Helps avoid detection and blocks network-level attacks in restrictive regions.
- Double VPN: Routes traffic through two servers for added encryption.
2. Surfshark
Surfshark is a low-cost VPN with strong protection against hackers. It lets you connect as many devices as you want, all at the same time. It’s great for families, friends, or anyone who wants to stay safe online without spending a lot. Easy to use, fast, and secure, Surfshark makes smart online safety simple.
Key Features that Prevent You From Hacking
- CleanWeb: Blocks phishing, malware, and intrusive ads at the DNS level.
- Kill Switch: Cuts connection instantly if VPN fails, protecting from IP/DNS leaks.
- Obfuscation (Camouflage Mode): Masks VPN traffic to prevent ISP or hacker tracking.
- NoBorders Mode: Lets you connect safely even in high-surveillance regions.
- Surfshark Alert (Add-on): Monitors the web for data breaches and leaks.
- Surfshark One (optional bundle): Includes antivirus and a secure search engine.
3. ExpressVPN
ExpressVPN works fast and smoothly, but it also keeps you safe in powerful ways. Behind the scenes, it uses strong tools to block hackers and online threats. You stay protected while you browse, stream, or shop. It's more than just a VPN – it's a shield for your internet. Simple, secure, and smart. Trust it to guard your privacy.
Key Features that Prevent You From Hacking
- TrustedServer Tech (RAM-only servers): No data is ever written to disk, your data disappears with every reboot.
- Self-Hosted Encrypted DNS: Keeps your DNS queries encrypted and private.
- Kill Switch (Network Lock): Prevents any traffic from leaking during disconnection.
- Perfect Forward Secrecy: Generates new encryption keys for every session.
- Split Tunneling: Choose which apps go through VPN to reduce attack surfaces.
- Built-in Obfuscation: Helps bypass firewalls and masks VPN use automatically, no setup needed.
- Threat Manager: Threat Manager on iOS and iPadOS blocks apps and websites from communicating with known trackers and malicious servers to enhance user privacy.
Remember that even though you can use VPNs to secure your connection, they will not protect you against backdoor attacks, vulnerabilities in software, malware, and unsafe browsing practices. It is important to educate yourself about safe Internet browsing.
Final Thoughts
Ever wondered what would really happen if your VPN got hacked? It's not just about losing anonymity; your personal data, browsing history, and even passwords could be exposed. VPNs are powerful, but they’re not foolproof. Hackers can exploit weak protocols, steal encryption keys, or even trick you into giving away access yourself.
What separates a vulnerable VPN from a trustworthy one? It comes down to encryption strength, updated protocols, and the provider’s overall security track record. Does your VPN offer features like AES-256 encryption, a kill switch, and Perfect Forward Secrecy? If not, it might be time to reconsider your choice before it’s too late.
Looking for a VPN that actually walks the talk? NordVPN is our top recommendation. Not only does it offer powerful tools like Threat Protection and Double VPN, but it also responded transparently to past incidents, proving it puts users first.
For complete understanding, have a look at these additional guides:
- Learn how safe VPNs really are in our detailed guide on How Safe Is VPN?
- Understand common VPN myths and get them debunked in VPN Myths Debunked
- Discover what your ISP can actually see when you use a VPN in What Does Your ISP See When You Use a VPN?
- Find out what VPN leaks are and how to detect and stop them in VPN Leaks: What They Are, How to Detect and Stop Them
- Explore if free VPN services are truly safe in Are Free VPN Safe?
- Learn about Double VPN and its added security benefits.
- Compare Tor and VPN to decide which privacy tool suits your needs.
- Check out the best no-log VPNs recommended by TechNadu experts.
We hope that you enjoyed reading this article about 'Can a VPN be Hacked?'. If you have any comments, remarks, or experiences to share, feel free to comment below!