Can a VPN Keep You Safe in War Zones? VPN Providers and Experts Answer Tough Questions
Over the past few weeks, we’ve been getting a lot of similar questions from people trying to figure out how VPNs actually work in high-risk situations. These aren’t casual questions. They’re coming from people who are trying to stay informed and protect themselves under real pressure. The problem is that clear, honest answers are hard to find, and much of the information online is either oversimplified or misleading.
To address this, we decided to go directly to the source. We reached out to leading VPN providers with a consistent set of questions, asking them to explain in plain terms what their services can and cannot realistically protect users from in such scenarios. The goal is not promotion, but clarity. We want to surface expert perspectives, highlight limitations, and give readers a more grounded understanding of the risks involved.
This is an ongoing thread, not a one-time piece. As more providers respond, we’ll keep adding their answers here so everything stays in one place. The idea is simple. Give you direct access to expert responses, side by side, so you can make more informed decisions based on real input rather than assumptions.
Windscribe: If Windscribe is connected properly, your internet provider should not see the websites or apps you are using through the VPN tunnel. They will generally still be able to see that you are connected to a VPN. In a country where VPN use itself is treated as suspicious, that may be a risk.
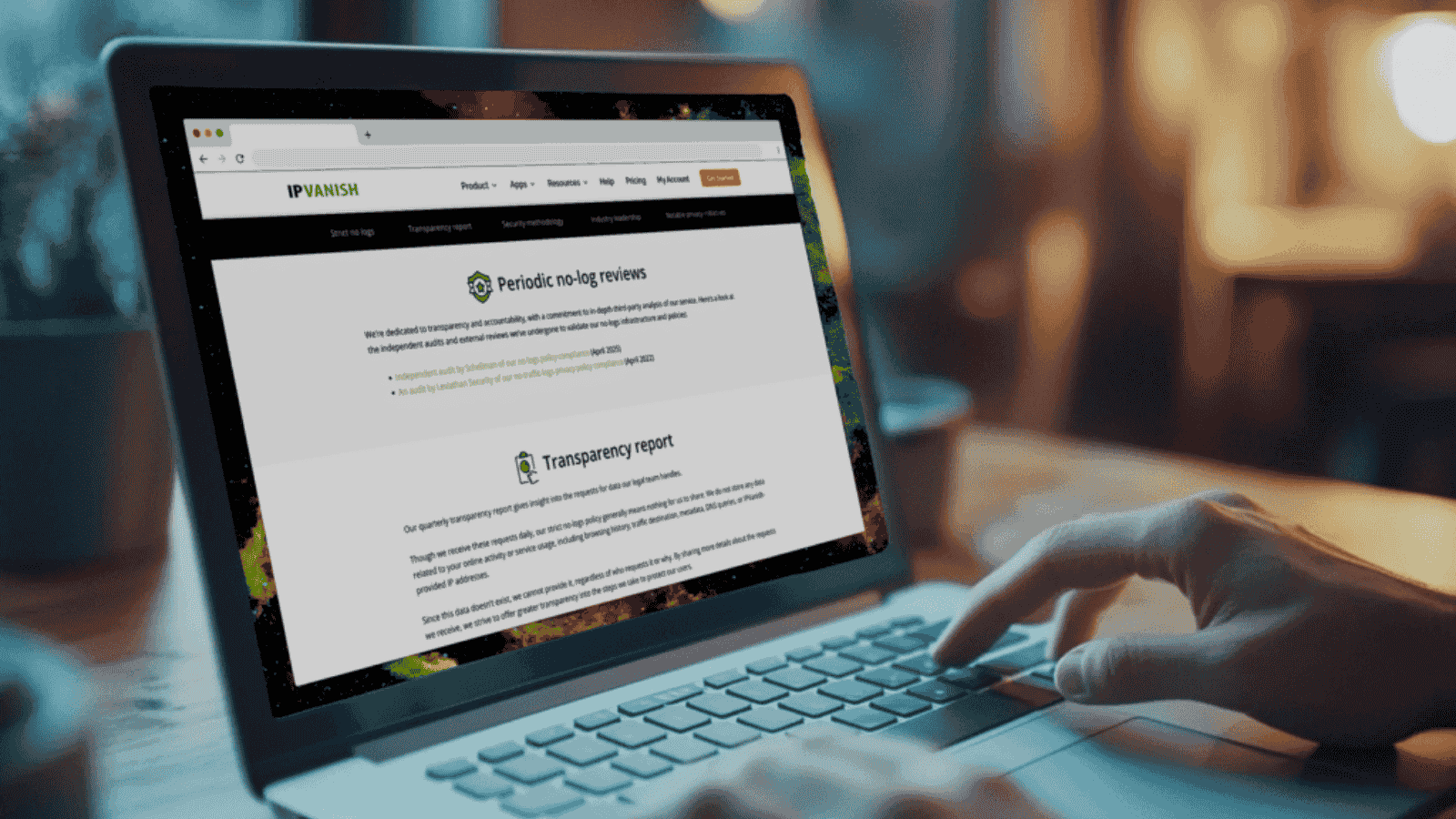
Windscribe does not keep connection logs, IP timestamps, session logs, or browsing activity logs, so we cannot reconstruct what a user did later from data we do not have.
That said, merely changing your IP address does very little for privacy if the rest of your operational security is poor. A VPN does not erase activity from the websites you log into, your device, browser history, app notifications, malware, payment records, cookies, browser fingerprints, or anything exposed before the VPN connection was established. In a life-or-death situation, the required operational security is much higher than simply turning on a VPN.
Windscribe: There is still a chance a user could be exposed, depending on what goes wrong.
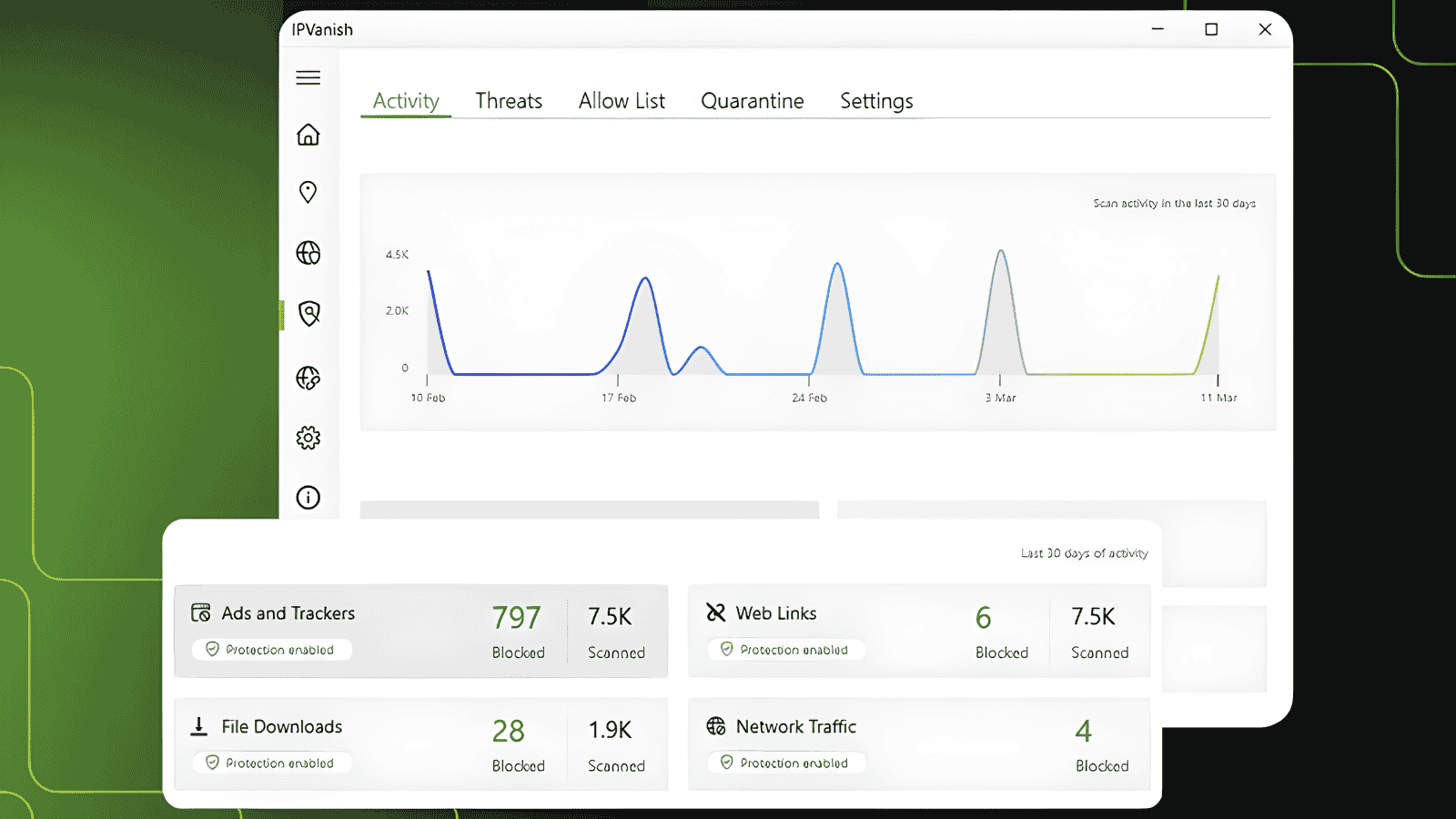
On desktop, Windscribe’s Firewall blocks connectivity outside the VPN tunnel if the VPN drops. On Android and iOS, users should use the operating system’s Always On VPN setting.
Windscribe also has Decoy Traffic mode (where available), which generates random activity over the VPN tunnel to make traffic correlation attacks harder. That can help in adversarial network environments, but it does not make someone invisible.
No VPN can fully hide the fact that a VPN may be in use from a sufficiently motivated internet provider or state-level adversary. A VPN can make traffic harder to inspect and correlate, but it cannot protect against device seizure, malware, phishing, account logins, screenshots, unsafe browser settings, or legal consequences from a government that treats circumvention itself as suspicious.
Windscribe: Windscribe is one of the more proactive VPN services when it comes to anti-censorship, but a VPN still needs some route from the user’s device to the outside internet. If international connectivity is fully cut off, no VPN has a secret path around that.
VPNs are most useful when there is still partial connectivity, throttling, DNS blocking, website blocking, or protocol-level interference that can be worked around. If the network is reduced to a domestic intranet or a strict whitelist, the VPN may not connect at all.
Windscribe: It depends on the network, carrier, region, and current blocking methods. This changes constantly.
Windscribe includes censorship-circumvention connection protocols such as Stealth, WStunnel, and AmneziaWG through Circumvent Censorship mode. These are designed for hostile network environments and, in many heavily censored regions, we are often able to get past blocks.
But there are limits. We can add layers of obfuscation that help VPN traffic blend in or slip through, but we cannot guarantee that attempted VPN use will never be noticed. If an adversary is sufficiently motivated, they can move toward allowlist-based blocking, where only explicitly permitted traffic is allowed through. In that scenario, there may be very little any VPN service can do.
Windscribe: While connected, surveillance actors can't tell what websites you visited, however, there are many, many moving parts in one's operational security. We cannot prevent state actors and even ISPs from knowing that you connected to a VPN, which by itself might be a risk to one's life.
Our advice is to treat a VPN as one layer of protection, not a complete safety guarantee. Use the latest app version, enable Circumvent Censorship, use Firewall where available, consider Decoy Traffic where available, avoid logging into personally identifying accounts when possible, keep the device clean, and consider the local risk environment before relying on any single tool.