When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.
What is VPN Obfuscation & How Does it Work?
It’s not just about using a VPN anymore. In places like China, even encrypted VPN traffic can be detected and blocked. Then what would you do? That’s where VPN obfuscation comes in, a stealthy technique that disguises your VPN traffic to look like regular browsing data.
But how does it work? When should you use it? And is it really foolproof? In this article, we’ll uncover the secrets of VPN obfuscation, show you when it matters most, and recommend the best VPNs that can fly under the radar.
Key Takeaway
- VPN obfuscation hides the fact that you're using a VPN by disguising VPN traffic as normal HTTPS traffic, helping bypass censorship, VPN blocks, and ISP throttling.
- It’s crucial in countries with VPN bans, schools or workplaces with firewalls, or when you want maximum privacy.
- Top VPNs like NordVPN, Surfshark, and ExpressVPN offer built-in obfuscation modes that activate automatically or with minimal setup. Our #1 recommendation will be NordVPN owing to its brilliant privacy features.
- To optimize performance, use split tunneling, change DNS settings, and enable kill switches and leak protection.
Obfuscation isn’t foolproof, but it’s a powerful tool when stealth and access matter most.
What Is VPN Obfuscation?
VPN obfuscation is a technique that prevents your ISP (Internet service provider) and spy organizations from finding out that you’re connected to a VPN. It consists of different features that make your VPN traffic look like regular Web traffic.
For example, in workplaces or universities where VPN traffic is often blocked to restrict access to certain sites or services, obfuscation can help you connect to a VPN without being flagged or disconnected. Moreover, if you live in a country where there are heavy restrictions on VPNs, then obfuscation comes pretty handy as it doesn't even make it look like you are using a VPN. It’s basically a VPN feature that disguises the fact that you’re using a VPN. Interesting, right?
But how does that happen? Well, obfuscation can be achieved by different technologies and tools that don’t necessarily work in a similar way. Some of the most common tools include OpenVPN, OpenVPN Scramble, Shadowsocks proxies, SSTP, and OpenVPN over SSL/TLS. Confused? Let's break it down a little for you!
How Does VPN Obfuscation Work?
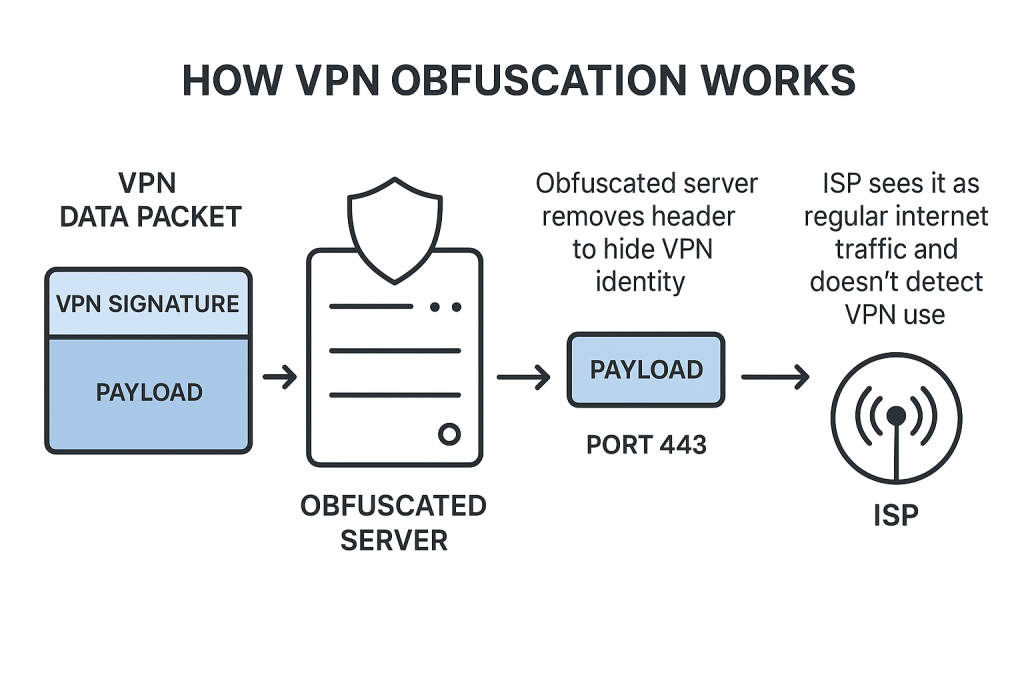
VPN obfuscation works by changing your VPN data packets to look like regular Internet traffic. This prevents ISPs from knowing that you’re a VPN user. On the flip side, if you’re using a regular VPN, your ISP can detect it, but they still cannot see your activities (here’s what your ISP sees when you use a VPN). This entire process can be broken down into two stages:
Stage-1
In the first stage, the obfuscated server will remove your VPN signature. To understand this better, let’s consider the example of an OpenVPN data packet.
Typically, a single data packet is divided into two parts: the header and the payload. The header contains metadata, which classifies the data as VPN traffic. The payload contains the actual contents of the data packet. Obfuscation removes information from the data packet’s header and prevents firewalls from recognizing it as VPN traffic.
Stage-2
In the next stage, obfuscation assigns the port number 443 to the data packet. This is the port number that regular HTTPS traffic uses. As a result, VPN traffic starts to resemble normal Web traffic. Hence, it becomes easier to pass through firewalls without getting detected.
Let's have a look at its visual representation:
When Is VPN Obfuscation Necessary?
VPN obfuscation is necessary to hide the fact that you’re using a VPN from government agencies, ISPs, and firewalls. There are many use cases for obfuscation, so let’s take a look at some common ones.
- When you're in a country that censors VPNs: There are many countries that ban the usage of VPN. In some countries, governments force ISPs to use DPI (deep packet inspection), which is a method to monitor and block VPN traffic. In some places, you can even get in serious trouble if the government catches you trying to use a VPN. Obfuscation can save you from these hassles.
- When your ISP Is throttling your VPN traffic: Most ISPs won’t do this. However, sometimes they can detect and throttle VPN traffic to discourage its use. In this case, VPN obfuscation techniques are the only way to trick your ISP into thinking you're just browsing HTTPS websites instead of using a VPN, thereby, removing chances of ISP throttling.
- When you're dealing with VPN blocks at school: Many people use VPNs at school to get around annoying firewalls. The problem is they might not work if admins are blocking VPN traffic. That is why it is advisable to use the most reliable VPNs for school that support obfuscation, so you can easily evade these blocks.
- If you want more privacy: If you’re looking for maximum privacy, obfuscation will always come in handy. For example, it can be helpful for journalists who use a VPN to conduct private interviews.
- When you want to unblock streaming & torrenting websites: Some streaming services block VPN connections and give a proxy error message. This is due to detection techniques like port blocking, deep packet inspection, and IP blacklisting. Thankfully, using the best streaming and torrenting VPNs that support obfuscation can easily let you bypass them.
When Not to Use VPN Obfuscation
It is best to avoid using VPN obfuscation when you want maximum speed. This feature will slow down your Internet speed due to the usage of extra layers of encryption and algorithms. So, data packets have to travel through longer routes.
- If you have a slow Internet connection: Obfuscated servers may render your Internet connection useless if the base speeds are already slow. This can cause an interruption in your online activities.
- To stream shows and movies: Streaming 4K/HD videos requires fast Internet speeds. But if obfuscation significantly limits your Internet speed, you will end up facing buffering delays and low-resolution results.
What VPN Obfuscation Techniques Do Providers Use?
VPNs use a range of techniques for obfuscation, like OpenVPN Scramble, Shadowsocks, obfsproxy, and more. Let’s take a look at some of the most prominent ones.
1. OpenVPN Scramble
OpenVPN Scramble is a patch applied to the OpenVPN protocol that adds a lightweight obfuscation layer using an XOR operation. It slightly modifies packet data to make it harder for firewalls to recognize VPN traffic based on deep packet inspection (DPI).
However, XOR is not a substitution cipher (like Caesar or Vigenère). Instead, it operates at the binary level, flipping bits based on a given key. While this does change the appearance of the data, it's a very basic and weak form of obfuscation that can be easily reversed with simple analysis tools.
Additionally, XOR-based obfuscation is commonly used by malware authors to evade detection, which means it may be flagged by security systems or ISPs.
PROS
- Open-source codebase.
- Simple to understand.
CONS
- Weak encryption.
- Not the best at bypassing firewalls.
- Frequently used by hackers.
2. Obfsproxy
Obfsproxy is a Tor subproject that adds a strong layer of obfuscation to VPN traffic using pluggable transports. The most modern and effective of these is obfs4, which is designed to make VPN and Tor traffic indistinguishable from random data.
Unlike older methods like obfs2 or obfs3, obfs4 uses a handshake protocol that avoids recognizable patterns, making it highly resistant to DPI and blocking. It’s particularly effective in countries with heavy censorship like Iran and China.
While manual setup can be tricky, some VPNs offer pre-configured obfs4 servers.
PROS
- Uses less bandwidth.
- Trustworthy (Tor project).
CONS
- Difficult to set up.
- Low level of obfuscation.
3. OpenVPN Over SSL
Unlike the previous VPN obfuscation techniques, this one involves adding an SSL (Secure Socket Layer) layer of encryption to the OpenVPN data. True, OpenVPN already uses a type of SSL encryption, but it has been tweaked, so it's different. And that is exactly why DPI (deep packet inspection) can easily reveal OpenVPN traffic.
When you wrap OpenVPN data in a layer of SSL encryption, DPI can no longer recognize it as VPN data. While this is a pretty efficient VPN obfuscation method, the setup process can be pretty difficult if you're not tech-savvy.
PROS
- Open-source.
- Commonly used in VPNs.
- Fast speed.
CONS
- SSL is outdated.
- Difficult to set up manually.
4. OpenVPN Over SSH
This is pretty similar to OpenVPN over SSL. The only difference is that it uses SSH (Secure Shell) to hide VPN traffic.
There's really not much to say here. SSH is pretty secure since it has strong encryption. The only drawback is that it's more of a corporate protocol since businesses use it to securely access shell accounts. You might still be able to use it as an average online user, but you'll need to talk with your VPN provider about that.
PROS
- Quite secure.
- Good speeds.
CONS
- Not available commonly.
- Commercial usage.
- Difficult to set up.
5. Shadowsocks
Shadowsocks is an open-source project based on the SOCKS5 proxy. A Chinese programmer using the pseudonym "clowwindy" created it back in 2012 to help people in the country bypass censorship, and also hide the fact that they're doing it.
On its own, Shadowsocks just masks online traffic, making it look like HTTPS so that you can bypass firewalls. It doesn't have much encryption to secure your data, though. However, a VPN provider can use their service together with Shadowsocks to hide OpenVPN traffic.
PROS
- Open source.
- Uses less RAM.
- Fast speed.
CONS
- Not officially audited.
- No port forwarding.
6. SoftEther
This is a multi-protocol software that was developed by Daiyuu Nobori. One notable aspect of SoftEther is that it’s fully open-source and helps create low-latency connections after its implementation. Furthermore, it runs on platforms like Windows, Linux, Solaris, macOS, and FreeBSD.
SoftEther has a proprietary protocol to create a secure tunnel. This helps bypass firewalls and create obfuscation because HTTPs handles regular internet traffic as well. Other than that, SoftEther also supports OpenVPN, L2TPv3, L2TP/IPSec, and EtherIP.
Unfortunately, SoftEther is not as secure because vulnerabilities have been found in its implementation in 2019. You can read more about Hide.me’s vulnerabilities with SoftEther.
PROS
- Quite secure.
- Bypasses firewalls.
- Very fast speeds.
CONS
- Not available commonly.
- Manual configuration.
- Security vulnerabilities.
7. SSTP
Secure Socket Tunnel Protocol is a popular and secure VPN protocol that was developed by Microsoft. Hence, it supports major platforms like Windows, Android, and Linux, along with many routers. This was designed as a replacement for the PPTP protocol in 2007.
Back then, SSTP was vulnerable to POODLE attacks (also known as a man-in-the-middle). However, it’s considered to be secure nowadays because TLS 1.3 and 1.2 are used to implement it instead of SSL3.
A number of trusted VPNs like Hide.me and IPVanish offer SSTP. However, censorship-friendly VPNs prefer using more sophisticated technologies.
Despite its secure nature, it may still have hidden vulnerabilities. According to the documents revealed by Edward Snowden in 2013, Microsoft and NSA have collaborated in mass spying activities in the past. This makes SSTP less reliable regardless of how good the technology is.
PROS
- Good at bypassing firewalls.
- Great speeds.
- Uses strong encryption.
CONS
- Cloud source.
- Possibly linked with the NSA.
8. V2Ray/VMess
V2Ray is a powerful open-source platform designed for censorship circumvention, especially popular in heavily censored countries like China and Iran. It supports multiple protocols, the most well-known being VMess, which encrypts and disguises traffic to avoid detection.
Although VMess is being phased out in favor of more secure and flexible protocols like VLESS and Reality, many tech-savvy users still rely on it due to its effectiveness and customization options. V2Ray offers multi-layered obfuscation, routing rules, and advanced traffic masking.
While it’s not widely used by mainstream VPNs, mostly due to complex setup and lack of demand among casual users, it remains one of the most sophisticated tools in censorship resistance.
PROS
- Great customization.
CONS
- Not available widely.
- Complicated implementation.
- Lack of security audits.
What's the Best Obfuscation VPN?
NordVPN is the best obfuscation VPN based on our rich experience of testing multiple providers. However, you do have more options. Let’s take a look at the prominent examples.
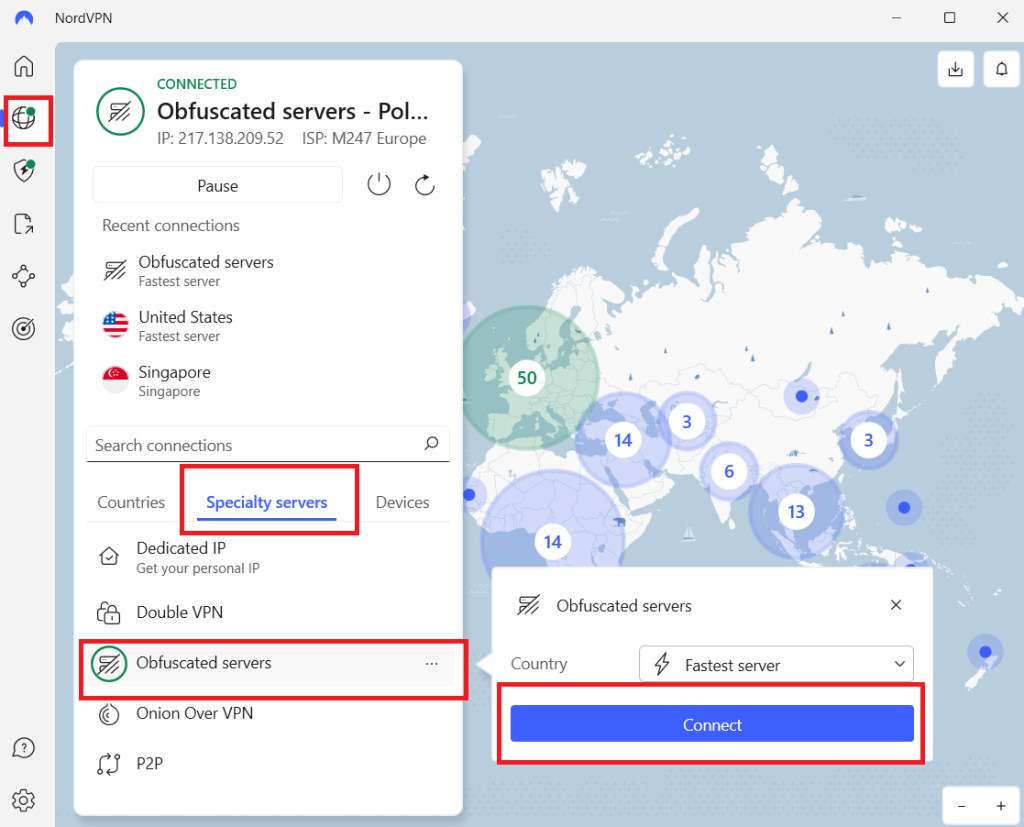
1. NordVPN
NordVPN is one of the most trusted VPNs on the market, known for its strong commitment to user privacy and excellent performance. It offers a strict no-logs policy, fast speeds, and Double VPN servers for added encryption. And not to mention, NordVPN obfuscation is available on all devices.
Enable obfuscation on Windows:
Go to NordVPN app > use OpenVPN (UDP/TCP) > Home > Specialty Servers > Obfuscated Servers > connect > Tap three dots to pick a country >Tap Disconnect to stop.
Additional privacy features:
- Nordlynx protocol based on WireGuard: It provides faster speed and better security.
- Kill switch: Automatically blocks Internet access if the VPN connection drops to prevent data leaks.
- Post-quantum encryption: Prepares your data to stay safe even against future quantum computing attacks.
- Split tunneling: Choose which apps use the VPN and which connect directly, giving you more control.
- Threat Protection: Blocks ads, malicious sites, and web trackers even when you're not connected to the VPN.
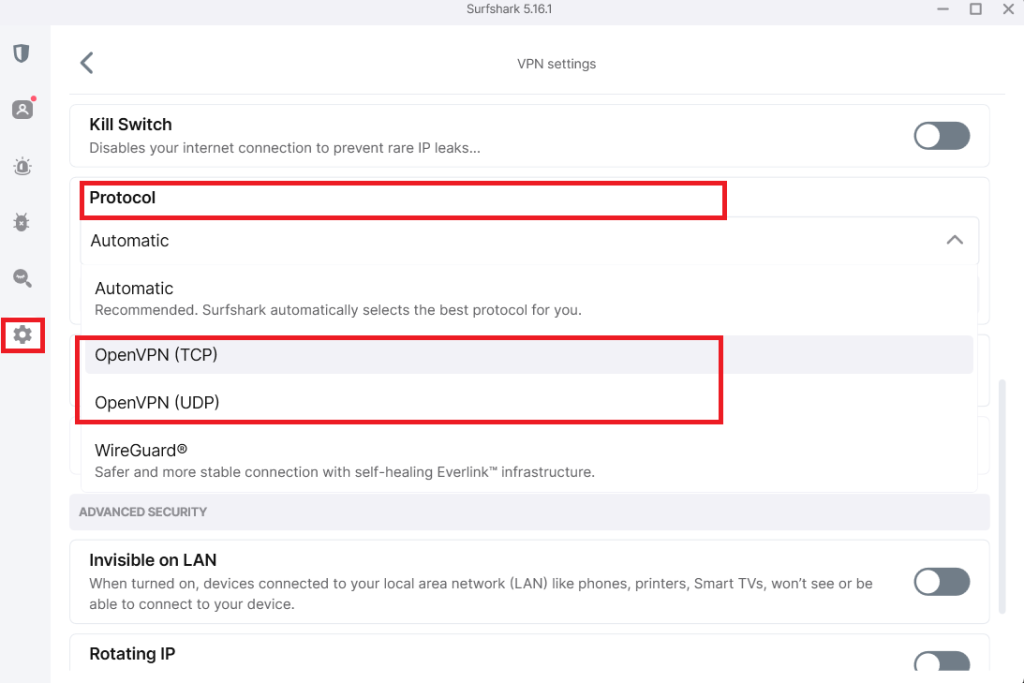
2. Surfshark
Based in the privacy-friendly Netherlands, Surfshark offers strong security and unbeatable value. It includes a kill switch, CleanWeb ad blocker, and DNS leak protection, making it ideal for everyday privacy and secure streaming.
How to enable obfuscation:
Use Camouflage Mode, which is automatically activated when you connect using the OpenVPN protocol. No manual setup is needed. And the best part is, Surfshark obfuscation is available on all devices.
Additional privacy features:
- Multihop (double VPN): Routes traffic through two VPN servers in different countries, adding an extra layer of encryption.
- NoBorders mode: Detects network restrictions and gives you access to servers optimized for use in restrictive regions.
- Kill switch: Disconnects your Internet if the VPN drops, preventing accidental data leaks.
- CleanWeb: Blocks ads, trackers, malware, and phishing attempts at the DNS level for safer browsing.
- Override GPS location: On Android, Surfshark can spoof your GPS location to match your VPN server, adding an extra layer of privacy.
3. ExpressVPN
ExpressVPN is a premium VPN known for speed, ease of use, and bulletproof privacy standards. All of its servers are automatically obfuscated, which makes it perfect for bypassing firewalls in restricted regions—no setup required.
How to enable obfuscation:
You don’t have to. Obfuscation (available on all devices) is built-in and activates automatically when needed.
Additional privacy features:
- TrustedServer (RAM-only): Runs all servers in RAM so that no data is ever stored permanently.
- Perfect Forward Secrecy: Assigns a new encryption key every session, so even if one key is compromised, past and future sessions remain safe.
- Self-hosted DNS: Prevents DNS leaks by keeping all DNS queries within the encrypted VPN tunnel.
- Kill switch (Network Lock): Stops all internet traffic if the VPN connection drops unexpectedly.
Can Governments Stop VPN Obfuscation?
Yes, governments can indirectly stop VPN obfuscation by going out of their way and blocking VPN websites, server IP addresses, blocking ports, and intercepting HTTPs traffic. Let’s take a look at these techniques:
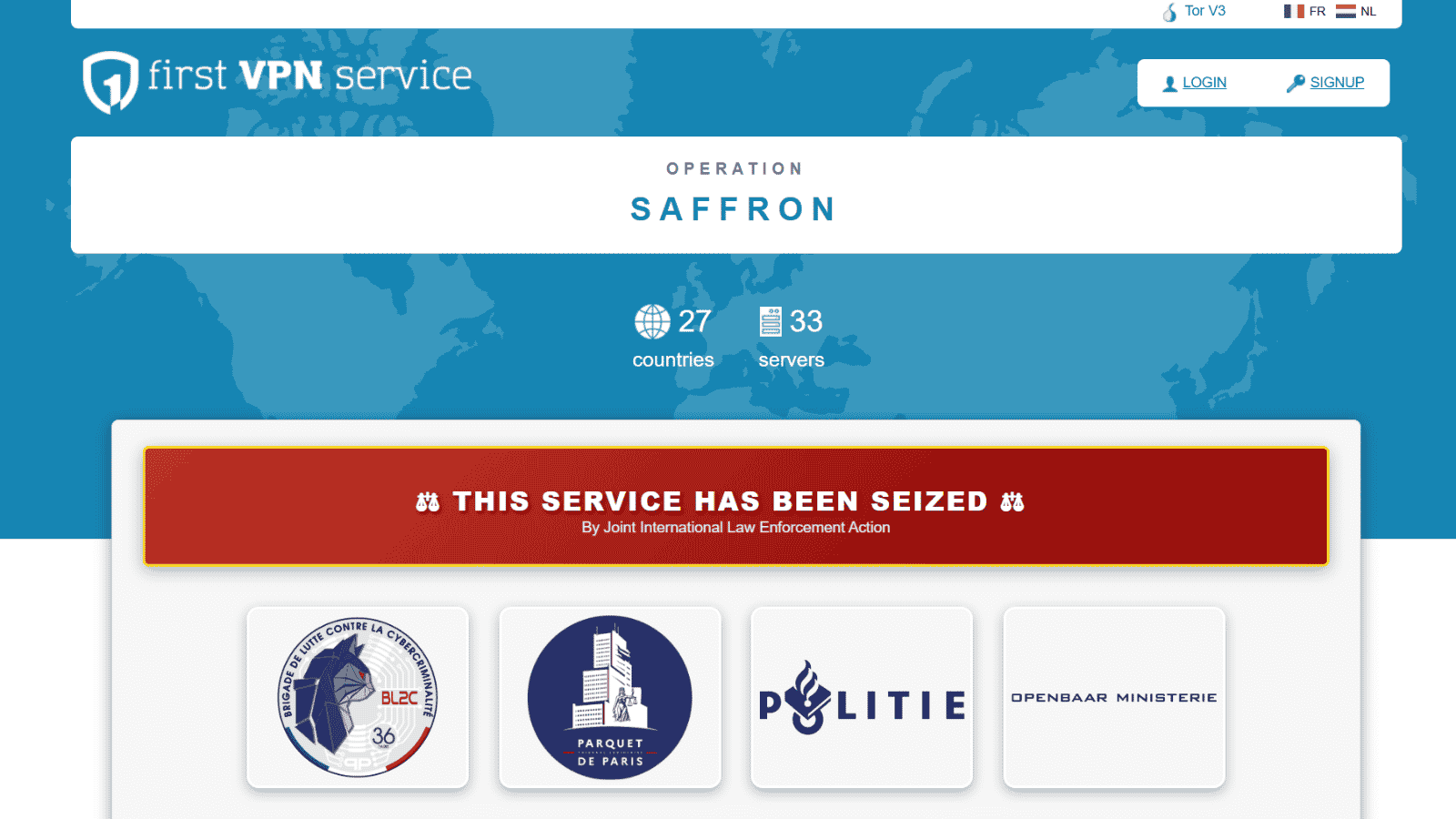
1. Block VPN Provider Websites
If they want to stop people in the country from using obfuscated VPN services, they can just block the websites of the providers that offer this feature. That stops people from subscribing to the service or downloading apps.
Sure, if you downloaded the VPN client before the government blocked the website, you would be fine - but not forever. In the end, you wouldn't have access to updates this way, and you wouldn't be able to change your subscription or renew it on the provider's website.
True, you can use a lesser-known VPN service or an online proxy to unblock the provider's website. But the government will know you're doing it if they use DPI. Also, they can block those services too.
2. Block VPN Server IP Addresses
If blocking a provider’s website isn't efficient for some reason, governments can just force ISPs to block the IP addresses of well-known VPN servers.
Not only that, but they can also order them to monitor your connections, flag suspicious IP addresses (those with no hostnames associated with the server), check if they belong to VPN servers, and block them. Remember - VPN obfuscation will hide the VPN traffic, not the VPN server's address.
3. Block the Ports VPN Protocols Use
ISPs can also just block the ports VPN protocols need to function. Without them, you can't run a VPN connection. For example, they could block UDP port 500 to stop IKEv2 or L2TP traffic. ISPs could also block UDP port 1194 to block OpenVPN traffic.
However, that's the port OpenVPN uses by default. If you or the provider configure it to use port 443, there's not much a government can do. If they block it, they would block HTTPS traffic country-wide. Until now, we have yet to hear of a country doing that.
4. Intercept HTTPS Traffic
Most obfuscation methods make VPN traffic look like regular HTTPS traffic. Well, if a country's ISPs or surveillance agencies were to intercept that traffic, and decrypt it, the government would easily find out who is using VPNs.
Sounds like it might never happen? After all, you can't really break HTTPS, right?
Well, not exactly. Kazakhstan actually started intercepting HTTPS traffic back in 2019. Basically, the authorities made ISPs force their users to install government-issued certificates on their devices. Those certificates allow government surveillance agencies to decrypt users' HTTPS traffic.
How to Get the Best Out of VPN Obfuscation
To get the best out of VPN obfuscation, you can use split tunneling, change DNS settings, and combine it with other preventive measures. That is because obfuscation can cause a massive speed drop-off. Let’s take a look at ways to optimize it.
1. Use Split Tunneling If Possible
Split tunneling means you can decide which traffic goes through the VPN tunnel, and which doesn't. For instance, you can use split-tunneling to separate VPN traffic (like Web browsers) from non-VPN traffic (like gaming clients). If you do that, you might increase your speed since you're making your traffic more lightweight.
2. Change Your ISP-Assigned DNS Settings
The default DNS settings you get from your ISP may not be ideal - especially when you're using a VPN. So, you should change them with your VPN provider's own DNS configuration. Alternatively, try using Google Public DNS or OpenDNS configurations.
3. Use Preventive Measures
This doesn't have much to do with speed, but it's a useful thing to keep in mind when using VPN obfuscation. The idea is that hiding your VPN traffic won't do much for your privacy if the VPN connection suddenly goes down or suffers leaks. So, to make sure you're safe, you should enable the kill switch feature. It'll shut off your Web access if your VPN connection goes down. Also, turn on IP and DNS leak protection.
What to Do When VPN Obfuscation Isn't Working
If obfuscation is not working for you, you should reach out to the VPN’s support team and ask for help. However, customer support can sometimes be slow. To help you fix obfuscation, we have compiled a list of common troubleshooting methods below.
Why is Using OpenVPN with Obfuscation Your Safest Bet?
Using OpenVPN with obfuscation is the safest because not all protocols offer advanced encryption like OpenVPN. So, there’s a chance with other protocols (albeit a small one) that your ISP could tell you're using a VPN.
In fact, if they check your outbound connections and see that you're connecting to an IP address with no hostname over UDP/TCP port 443, they'll likely realize you're using a VPN server. If you get caught doing that in a country where it's illegal or at work/school where it's against the rules, you can end up in a lot of trouble.
So, it's just safer to use OpenVPN with VPN obfuscation in that case.
Final Thoughts
VPN obfuscation is useful because it hides the fact that you’re using a VPN, which allows you to bypass firewalls and prevent spying. Not even your ISP can tell that you’re connected to a VPN. However, it also has some drawbacks like potentially complicated setup and low speeds.
Most of the capable VPNs provide built-in obfuscated servers that are also optimized for high speed. This removes the hassle of having to set up obfuscation manually.
We recommend NordVPN due to its built-in high-speed obfuscated servers. This VPN has 8,900+ servers in 129 countries. And the best part, it supports obfuscation on all devices.
Finally, we hope that you found this article very valuable and it answered all your questions about VPN obfuscation. Feel free to comment below or to reach out to us if you have any queries. Thanks for reading!