Rockstar Games Data Breach Reportedly Leaked Analytics via Prior Anodot Security Incident
- Data breach confirmed: A massive data leak has exposed millions of internal records belonging to the premier video game publisher Rockstar Games.
- Third-party compromise: Attackers said they accessed Snowflake instances utilizing authentication tokens stolen during a prior Anodot security incident.
- Analytics data exposed: The leaked datasets reportedly contain player behavior metrics, game economy tracking, and anti-cheat model testing without impacting player accounts.
ShinyHunters recently released 78.6 million internal analytics records, reportedly from a confirmed Rockstar Games data breach. The leak allegedly includes in-game revenue tracking and player behavior patterns for titles like Grand Theft Auto Online and Red Dead Online, as well as fraud detection systems and anti-cheat model testing.
Exploiting Cloud Infrastructure
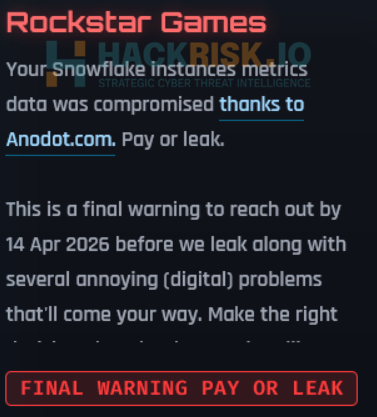
The ShinyHunters extortion group claimed on its leak site on Saturday that it compromised Snowflake instances via authentication tokens stolen during the recent Anodot breach (AI-powered business analytics platform). A gang representative told Reuters in an online chat on Monday that the breach involves 78.6 million exfiltrated records.
The hackers told Bleeping Computer the data leak contains mostly internal analytics related to Rockstar's online services and customer support analytics for the company's Zendesk support instance.
While the maker of the Grand Theft Auto and Max Payne video games confirmed the unauthorized access in a statement to Kotaku, they explicitly stated that the compromised files consisted of non-material company information. "This incident has no impact on our organization or our players," the statement reads.
The incident at data anomaly detection company Anodot involved the compromise of Snowflake, S3, and Amazon Kinesis instances.
Cybersecurity Implications
This Rockstar Games data breach does not impact the organization or its players, the statement said. To defend against similar supply chain attacks, enterprise network administrators must rigorously audit third-party access tokens and enforce the detection of anomalous behavior across all interconnected cloud platforms.
In a March announcement, ShinyHunters claimed a massive Salesforce breach that compromised data from Snowflake, Okta, Sony, AMD, LastPass, and Salesforce. In June 2024, a ShinyHunters member shared details on how the gang allegedly stole Snowflake customer data.
Scattered Lapsus$ Hunters were observed impersonating Zendesk in a phishing campaign targeting credential theft in November 2025.
In early 2025, a Path of Exile 2 breach led to hacked player accounts and theft of in-game items.