Global Cybersecurity Risks Led by State-Sponsored Groups: China-Nexus Threat Activity Increases by 75%, Hacktivist Activity by 60%
- Shared attack vectors: Adversaries consistently leverage unpatched software vulnerabilities and compromised identity credentials to penetrate enterprise networks.
- Geopolitical threat motivations: China's cyber espionage and Russia's cyber activity heavily align with national strategic objectives and international conflicts.
- Advanced persistence tactics: Threat actors deploy custom backdoors and tunneling tools to maintain undetected, long-term access within compromised infrastructure.
Advanced persistent threat (APT) groups originating from China, Russia, North Korea, and Iran share common tactical patterns. Despite having diverse strategic objectives, these state-sponsored adversaries rely heavily on similar access paths to infiltrate organizations, security analysts said in the Talos 2025 Year in Review.
China Cyber Espionage and Russian Cyber Activity
China-nexus operators demonstrate rapid software exploitation capabilities, with an observed increase of nearly 75%. They leverage both newly disclosed and legacy network vulnerabilities (e.g., ToolShell) and establish persistence via web shells, custom backdoors, tunneling tools, and credential harvesting. Chinese cyber espionage frequently overlaps with financially motivated cybercrime, creating dual revenue streams.
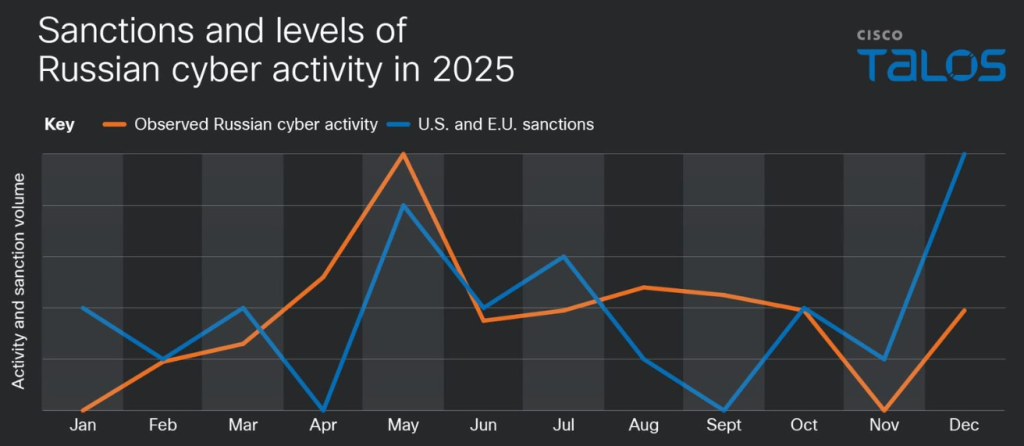
Concurrently, Russian cyber activity remains tightly bound to international sanctions and the ongoing conflict in Ukraine. Russian threat actors consistently exploit unpatched edge devices to deploy commodity malware variants, such as Remcos RAT, Dark Crystal RAT (DCRAT), and Smoke Loader.
These tools ensure continuous intelligence collection and unauthorized network access.
Evaluating Tactics from North Korea and Iran
North Korean offensive operations prioritize complex social engineering and fraudulent insider access. Operatives utilize fake corporate recruiter personas and artificial intelligence to infiltrate major enterprises. These tactics facilitate historic cryptocurrency heists that finance state military operations.
Meanwhile, Iranian threat groups execute hybrid campaigns, with a 60% increase in hacktivist operations. They coordinate highly visible distributed denial-of-service (DDoS) attacks linked to regional tensions, while specialized units deploy backdoors to maintain covert access to targeted telecommunications networks.
The following guidance is recommended for security teams:
- Don’t ignore older systems.
- Prioritize identity security.
- Increase visibility into network and edge infrastructure.
- Expect activity to follow global events.
- Inspect for long-term presence.
Early this month, the suspected head of a cyberfraud syndicate was extradited from Cambodia to China. In March, the EU sanctioned Iranian and Chinese firms for cyberattacks against European networks.