This Month’s Patch Tuesday Brings Fixes for 11 Actively Exploited Vulnerabilities
- Microsoft is pushing a small “Patch Tuesday” which is very important to apply nonetheless.
- The software giant has identified and fixed eleven actively exploited bugs, four of which are critical.
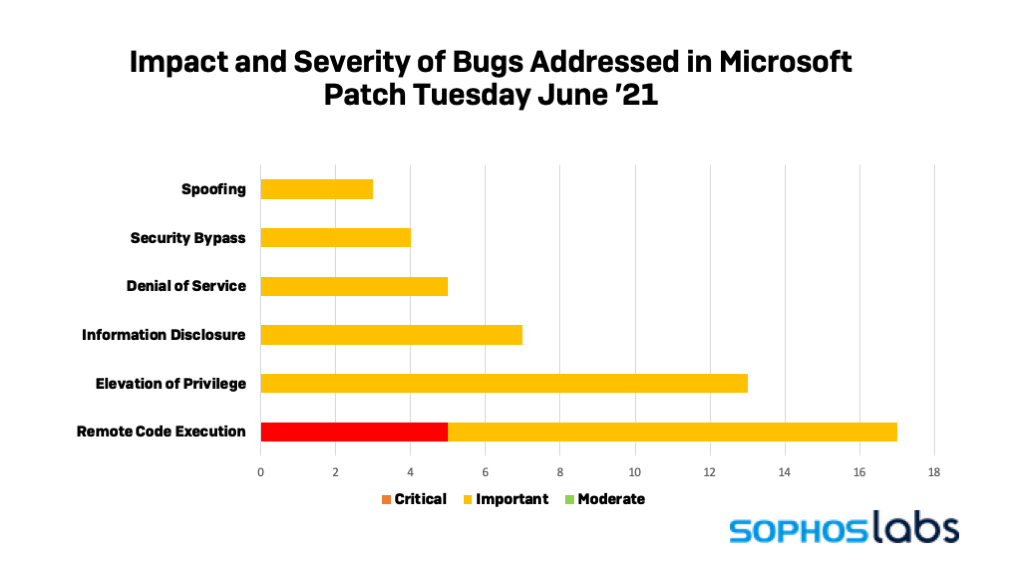
Microsoft has released the June 2021 “Patch Tuesday” for its various products. The notable aspect this month is that the pack contains fixes for eleven vulnerabilities currently under active exploitation. As such, applying the patch is a tad bit more critical than usual, although there’s really no Tuesday Patch that system administrators can afford to skip or even postpone. In total, Microsoft has fixed 49 flaws, with five of them being critical and the rest classified as important.
Here are the most important critical fixes of this month:
- CVE-2021-33742 – Actively exploited flaw in the Windows MSHTML, abusing the Internet Explorer HTML engine to execute commands on the target system.
- CVE-2021-33741 – Actively exploited elevation of privilege vulnerability affecting the Edge browser.
- CVE-2021-31985 – Actively exploited remote-code execution flaw in Microsoft Defender.
- CVE-2021-31959 – Actively exploited memory corruption vulnerability in the Chakra Jscript engine.
And below are the currently-exploited flaws that are rated as “important”:
- CVE-2021-31199 and CVE-2021-31201 – Vulnerabilities in Microsoft’s Enhanced Cryptographic Provider
- CVE-2021-33739 – Elevation of privilege bug in the Windows NTFS
- CVE-2021-31956 – Elevation of privilege flaw in the Windows DWM Core Library
- CVE-2021-31955 – Information disclosure bug in the Windows Kernel.
Although the classification of the flaws is definitely a critical factor to consider, it is often indicative of the damage potential that a particular exploit could have. This month, we see five important bugs being actively exploited. This indicates that even small holes are important to address as they can open up the potential for other, more serious exploits. Some of these zero-days are used in chained exploits, so no matter if a bug is rated as critical or just important, if adversaries are using it, there’s a good reason to fix it.
Before you apply this month’s update, make sure to backup your data and secure your most important files from unfortunate events like a corrupted filesystem. Remember, this is rare, but it can happen, so don’t skip the backing-up part.
Adobe has synchronized the fixing of critical flaws on its products too, so if you’re using the Reader, Photoshop, Connect, and the Creative Cloud in general, you should apply the available updates there too.