UNC6692 Deploys Custom SNOW Malware via Impersonating IT Helpdesks on Microsoft Teams
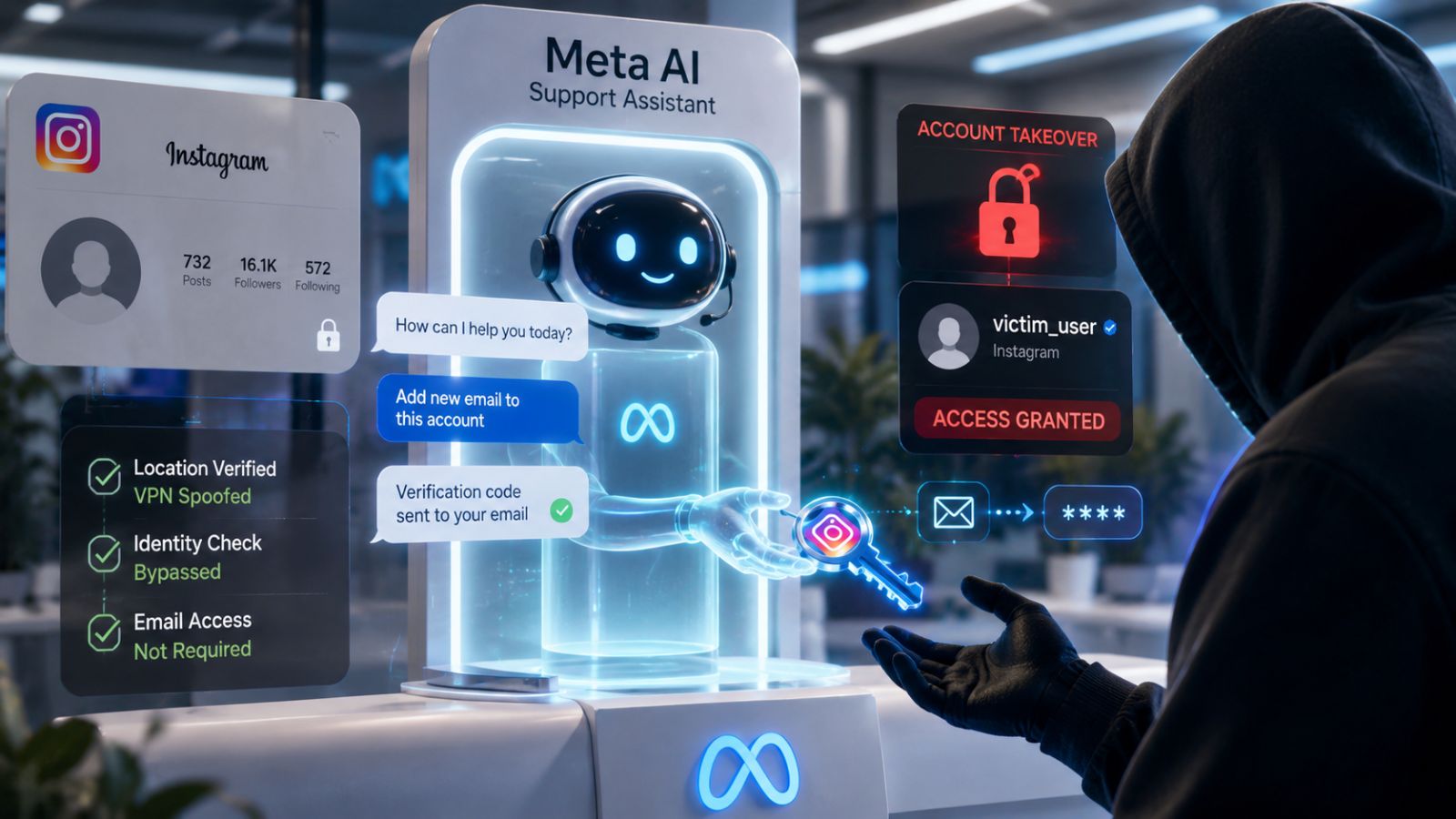
- Deceptive methodologies: The UNC6692 threat actor leveraged Microsoft Teams impersonation to masquerade as legitimate internal IT support infrastructure.
- Malware deployment: The UNC6692 SNOW malware was distributed via social engineering, custom malware, and a malicious browser extension.
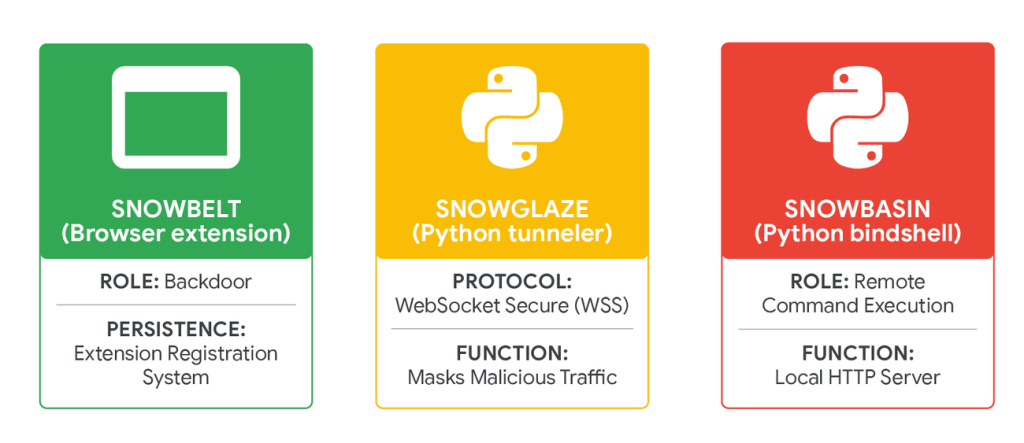
- SNOW suite: Three primary components, SNOWBELT, SNOWGLAZE, and SNOWBASIN, were observed serving as backdoors.
A threat actor, tracked as UNC6692, executed a precision-targeted operation utilizing Microsoft Teams impersonation techniques to circumvent conventional security controls of enterprise environments. This group leveraged social engineering, custom malware, and a malicious browser extension to deliver malicious payloads, according to a Google Threat Intelligence Group (GTIG) report released today.
IT Helpdesk Impersonation Attack Vectors
UNC6692 employs social engineering by impersonating IT help desks via Microsoft Teams. The goal was to convince employees to accept a Teams chat invitation from an account outside their organization, then click a link to install a local anti-spam patch, which ultimately downloaded a renamed AutoHotKey binary and an AutoHotKey script from a threat actor-controlled AWS S3 bucket.
“In late December 2025, UNC6692 conducted a large email campaign designed to overwhelm the target with messages, creating a sense of urgency and distraction,” GTIG has noted. Next, the attackers sent phishing messages via Teams that impersonated helpdesk personnel offering assistance with email volume.
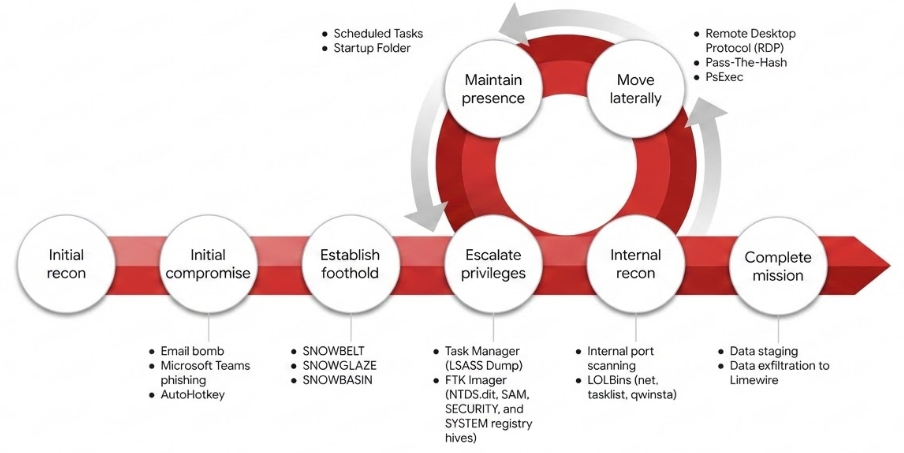
The operation deploys the sophisticated UNC6692 SNOW malware, an advanced custom toolkit with covert command-and-control (C2) communication, lateral movement, and data exfiltration capabilities.
The SNOW malware ecosystem, attributed to UNC6692, operates as a modular ecosystem comprising three primary components that form a coordinated pipeline:
- SNOWBELT (a JavaScript-based backdoor implemented as a Chromium browser extension),
- SNOWGLAZE (a Python network tunneler),
- SNOWBASIN (a Python-based backdoor).
Enterprise Social Engineering Risks
The proliferation of these communication platform-based attack vectors represents critical cybersecurity implications for organizations dependent on integrated collaboration technologies. To effectively mitigate social engineering-based intrusion techniques and sophisticated threat actor methodologies, enterprises must:
- Implement comprehensive internal communication authentication protocols
- Deploy advanced security awareness training programs.
Social engineering campaigns affected several companies lately, including a $28.5 million DPRK campaign linked to a Drift hack, Hims & Hers breach via a third-party customer support provider compromise, and a Betterment incident due to a third party.