Funksec Launches V1.5 RaaS to Expand Ransomware Arsenal
- Cybercriminal group Funksec recently endorsed a new Ransomware-as-a-Service advertisement on the dark web.
- Named Funksec V1.5, the RaaS can evade detection and encrypt faster than other tools.
- The new ransomware group that focuses on extortion was found extending its capabilities with RaaS tools.
A leading threat intelligence platform recently found a new Ransomware-as-a-Service (RaaS) advertisement on the dark web. The RaaS was floated on the dark web by the cybercriminal group called ‘Funksec.’
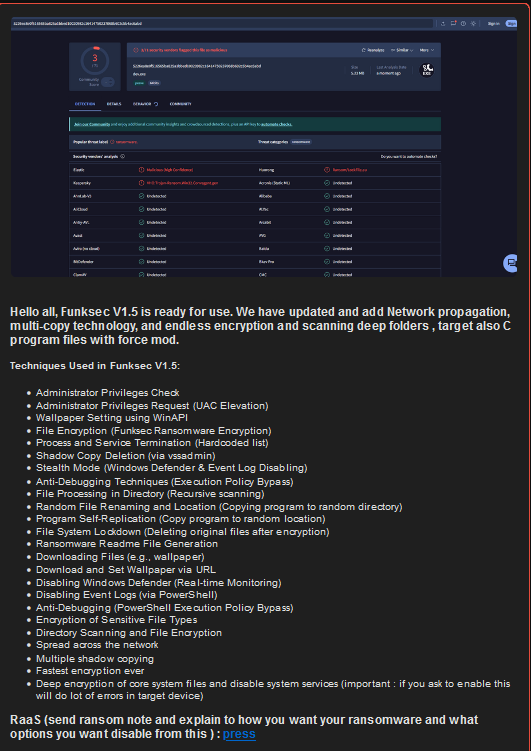
The Funksec group, which reportedly started operations in December 2024, stated that the updated version of RaaS, dubbed Funksec V1.5, offers additional benefits to cybercriminals like:
- Administrator Privileges Check
- Administrator Privileges Request (UAC Elevation)
- Wallpaper Setting using WinAPI
- File Encryption (Funksec Ransomware Encryption)
- Process and Service Termination (Hardcoded list)
- Shadow Copy Deletion (via vssadmin)
- Stealth Mode (Windows Defender & Event Log Disabling)
- Anti-debugging techniques (Execution Policy Bypass)
- File Processing in Directory (Recursive scanning)
- Random File Renaming and Location (Copying program to random directory)
- Program Self-Replication (Copy program to random location)
- File System Lockdown (Deleting original files after encryption)
- Ransomware Readme File Generation
- Downloading Files (e.g., wallpaper)
- Download and Set Wallpaper via URL
- Disabling Windows Defender (Real-time Monitoring)
- Disabling Event Logs (via PowerShell)
Anti-Debugging (PowerShell Execution Policy Bypass) - Encryption of Sensitive File Types
- Directory Scanning and File Encryption
- Spread across the network
- Multiple shadow copying
- Fastest encryption ever
- Deep encryption of core system files and disable system services (important: if you ask to enable this will do lot of errors in target device)
The extortion group further stated that the Funksec V1.5 RaaS offers network propagation which can potentially infect scores of computers at once. It could also go undetected by Windows Defender and Event Log, so the cybercriminals may launch cyberattacks and maintain persistence for longer.
The dark web advertisement stated that Funksec V1.5 can perform routine tasks like downloading files, encrypting files, and fetching the wallpaper via the URL.
The Funksec V1.5 boasts of not just encrypting core system files but also of the fastest encryption speed so far. It can access C program files and self-replicate files in no time, the advertisement read.
Not just this, the developer of the Funcksec V1.5 RaaS offered to customize the features according to the needs of the buyer or subscribers for malicious purposes.
In a world where the cost of recovering from a ransomware attack is predicted to cross over $250 billion by 2031, updates in malware and RaaS, as seen in Funksec V1.5, are a huge cause of concern for organizations and governments alike.
While the target suffers a massive recovery cost due to security breaches, a report by Halycon, a ransomware recovery platform, shed light on the meager amount paid by criminals to gain access to the stolen data.
In one incident, Funksec offered to sell exfiltrated data from a victim, reportedly a government research center, for only $1000.
In another instance, they demanded a ransom of $10,000 from a major power grid operator. If the victim did not comply, they threatened to sell the data to ‘other parties’ for half the price of $5000.
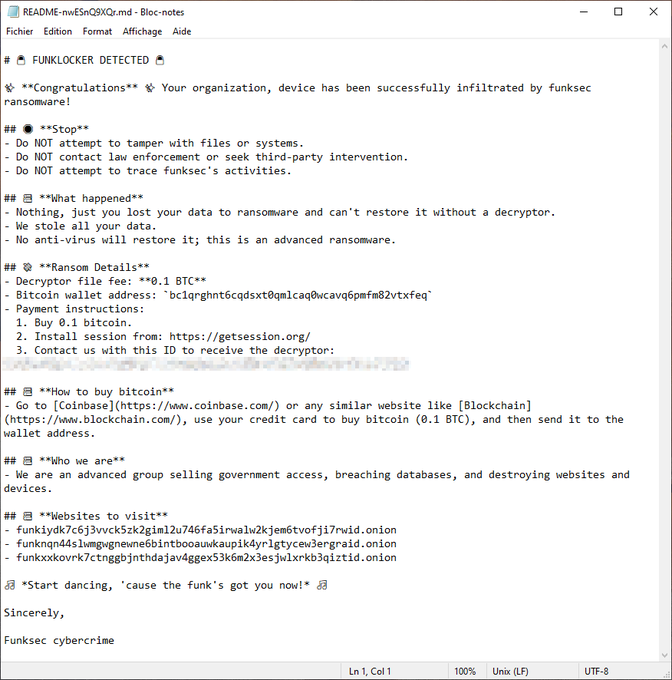
A malware researcher posted a screenshot of a ransom note left by Funksec on an infiltrated system. It read, “We stole all your data. No anti-virus will restore it; this is an advanced ransomware.”
This speaks volumes about the confidence of developers engaged in malicious activities. It cannot be said with surety whether these threat actors are backed by a state or not. However, there have been endorsements of tests, competitions, and rewards on the dark web for interested coders to develop malicious software for money.