Checkmarx Jenkins AST Plugin Compromised by TeamPCP Using Credentials Stolen in the Trivy Supply Chain Attack
- Rogue plugin: A malicious version of the Checkmarx Jenkins AST plugin was published on the Jenkins Marketplace.
- TeamPCP claims responsibility: The threat group utilized credentials from the Trivy breach to deploy credential-stealing malware.
- Remediation steps advised: Checkmarx urges users to deploy older plugin versions while they publish a secure update.
Checkmarx issued a critical security warning after discovering a rogue version of its Jenkins Application Security Testing (AST) plugin published on the Jenkins Marketplace. The compromise, formally claimed by the TeamPCP hacker group, marks the third incident in a series of targeted supply-chain attacks the firm has suffered since late March.
Jenkins operates as a widely used CI/CD automation solution, making compromised plugins a significant vector for enterprise networks. Checkmarx confirmed it is in the process of publishing a new version of the plugin to mitigate the threat.
Unauthorized Access and Malware Deployment
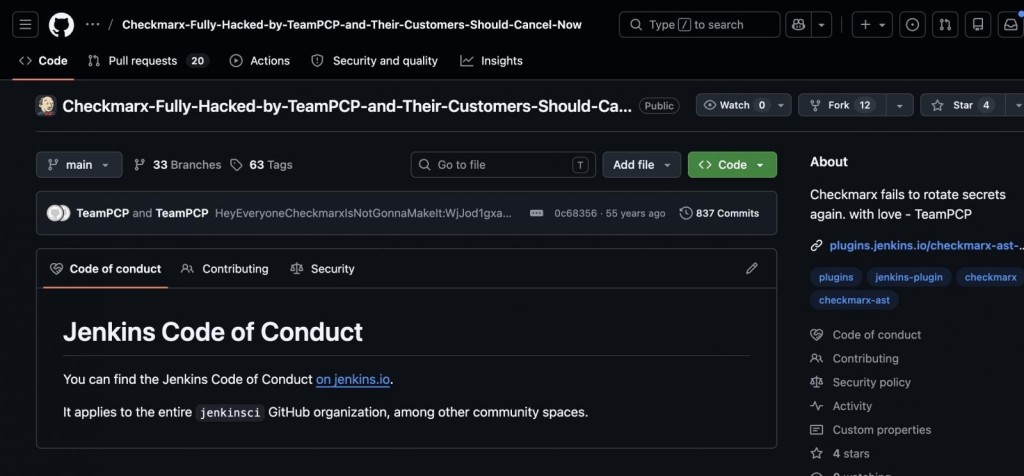
TeamPCP gained unauthorized access to Checkmarx GitHub repositories and backdoored the Jenkins AST plugin to deliver infostealers, according to offensive security engineer Adnan Khan. A Checkmarx spokesperson told BleepingComputer that the threat actor obtained the repository credentials during the Trivy supply-chain attack earlier in March.
On May 9, the threat actors uploaded the rogue version, designated as 2026.5.09, directly to repo.jenkins-ci.org. This malicious package was uploaded entirely outside the standard plugin release pipeline and included active malicious code.
Furthermore, analysts noted that the malicious plugin lacked a standard git tag and an associated GitHub release. "Checkmarx fails to rotate secrets again. With love - TeamPCP," said the hackers left in the about section.
Network Mitigation and Infrastructure Isolation
To mitigate immediate infrastructure risks, Checkmarx advised users to ensure they are utilizing the latest iteration of the plugin. “If you are using Checkmarx Jenkins AST Plugin, you need to ensure that you are using the version 2.0.13-829.vc72453fa_1c16 that was published on December 17, 2025, or previously,” the advisory said. The security update also contains a set of indicators of compromise (IoCs).
Addressing data security concerns, Checkmarx stated that its GitHub repositories are strictly isolated from customer production environments and confirmed that no customer data is stored within the compromised repositories.
Last month, Checkmarx confirmed that LAPSUS$ had leaked its GitHub data, which was stamped March 30.
A LiteLLM incident, which the company suspects that the compromise originated from the Trivy dependency, is suspected to be linked to TeamPCP. The cyberattack affected Mercor AI, with LAPSUS$ claiming the breach. The connection between Lapsus$ and TeamPCP is not yet clear.
Security researchers noted that Trivy Docker images pushed to Docker Hub without corresponding GitHub releases contained infostealer IOCs associated with TeamPCP.
Reports a few days ago warned that the credential-stealing worm PCPJack targets TeamPCP victims.