Kaspersky 2026 Ransomware Report Details Shifting Threats, as Attacks Decline and Tactics Change
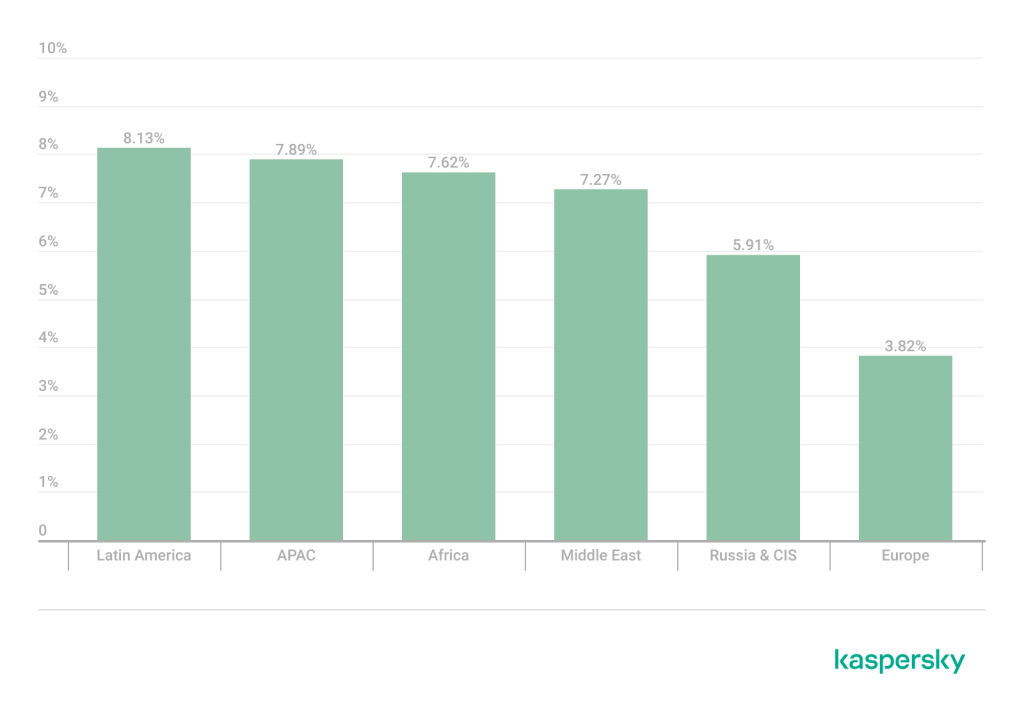
- Attack volumes decrease: The share of organizations affected by ransomware decreased globally in 2025.
- Evasion tactics escalate: Attackers increasingly deploy EDR killers and BYOVD techniques to bypass security.
- Post-quantum cryptography: New ransomware families utilize advanced algorithms to resist future decryption efforts.
Kaspersky’s "State of Ransomware in 2026" report details that while the share of organizations affected by ransomware decreased across all regions in 2025 compared to 2024, the malware remains a major enterprise threat.
Threat actors are rapidly refining their intrusion methodologies, increasingly deploying EDR killers and Bring Your Own Vulnerable Driver (BYOVD) techniques to disable endpoint defenses.
Advanced Cryptography and Encryptionless Extortion
The contemporary threat landscape is currently witnessing the deployment of post-quantum cryptography. The new PE32 ransomware family utilizes the cutting-edge ML-KEM (Module-Lattice-Based Key-Encapsulation Mechanism) standard to secure its AES keys, the report said.
NIST recently selected this cryptographic framework as the primary standard for post-quantum defense. Simultaneously, malicious groups are shifting toward encryptionless extortion.
As global ransom payment rates dropped to 28% in 2025, according to Chainalysis, threat actors like ShinyHunters are abandoning file encryption in favor of data theft and extortion via public leaks.
Furthermore, the industrialization of attacks relies heavily on initial access brokers (IABs), who continue to exploit RDP, VPN, and RDWeb as their leading network access vectors. This Access-as-a-Service model is fueled by “credential theft operations, and the widespread availability of compromised accounts harvested through infostealers and phishing campaigns.”
Dominant Threat Actors and Law Enforcement
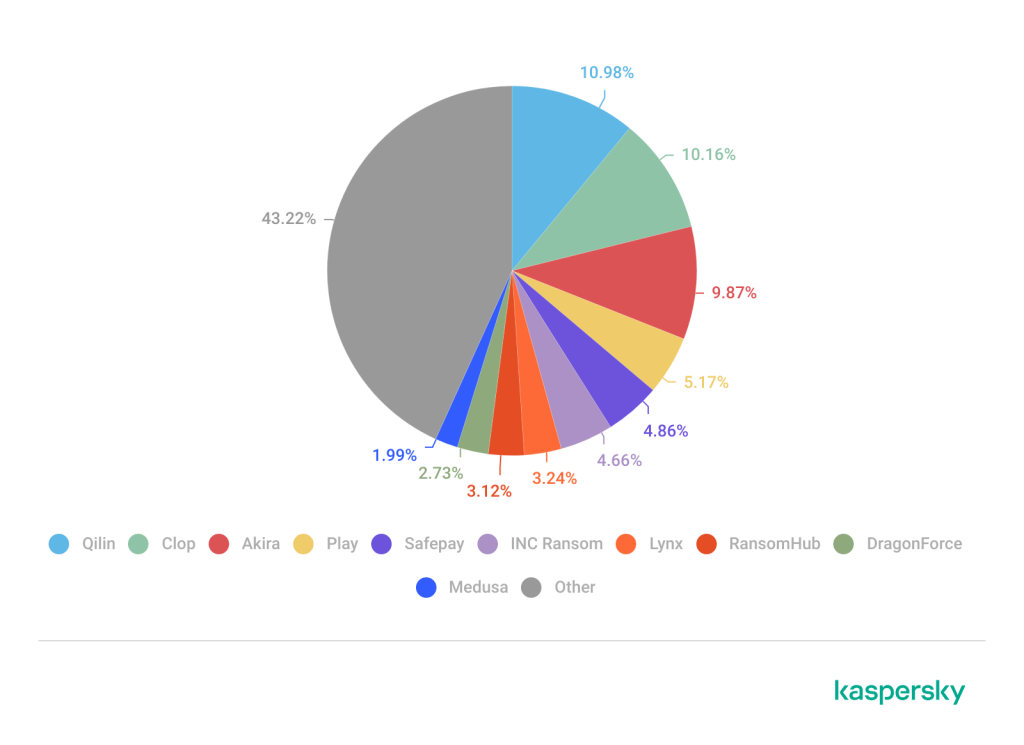
Qilin operated as the most active targeted ransomware group in 2025. Other major active operators included Cl0p Ransomware and Akira, while RansomHub experienced a rapid operational rise and subsequent disappearance.
DragonForce and emerging actors like The Gentlemen continue to professionalize data-centric extortion workflows. Some other groups to take note of in 2026:
- Devman
- MintEye
- DireWolf
- NightSpire
- Vect
- Tengu
- Kazu
In response to this activity, global law enforcement agencies escalated infrastructure disruptions, seizing prominent dark web platforms RAMP and LeakBase in 2026. These takedowns follow prior operational successes that seized Nulled, Cracked, XSS, and the official data leak sites of BlackSuit and 8Base.
A December 2025 report outlined that modern Akira, Qilin, and Medusa Ransomware cyberattacks use Shanya Packer-as-a-Service (VX Crypt). Last month, Qilin claimed a cyberattack on the German Democratic Socialist Party, Die Linke.