Cloud Credential Worm ‘PCPJack’ Targets TeamPCP Victims
- Cloud credential theft: SentinelLABS identified PCPJack, a framework that worms across cloud infrastructure and removes TeamPCP artifacts.
- No cryptominers deployed: The toolset targets Docker, Kubernetes, and other exposed services strictly for credential harvesting.
- Secondary toolset discovered: Researchers identified additional scripts and Sliver binaries targeting enterprise and AI service credentials.
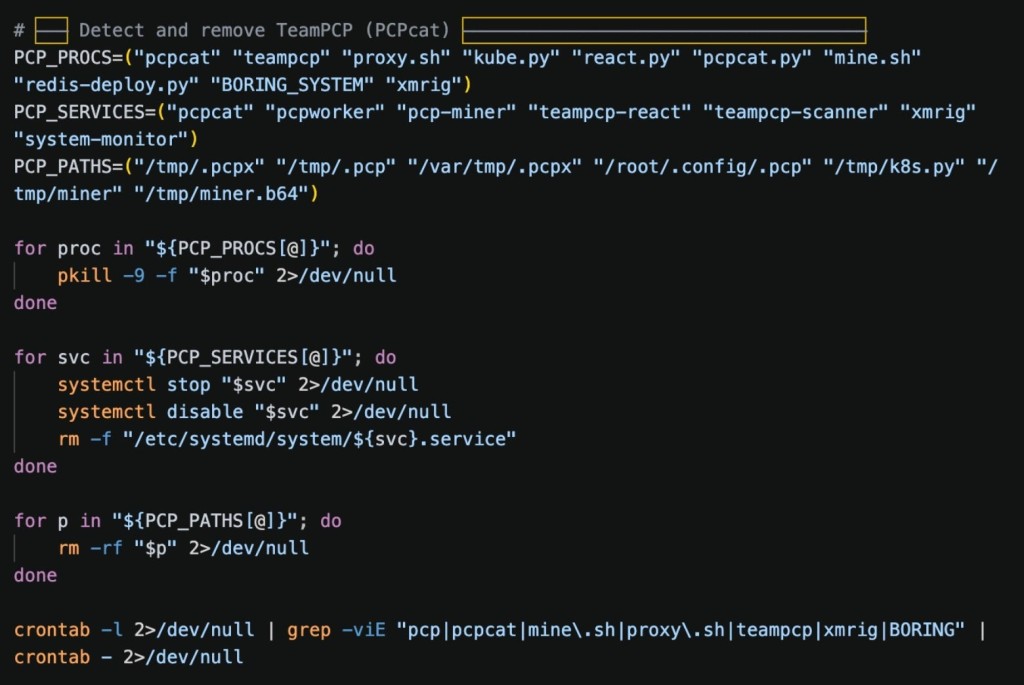
An aggressive cloud worm, initially programmed to specifically evict tools and artifacts associated with the TeamPCP threat group, traverses exposed cloud infrastructure to systematically harvest credentials from cloud, container, developer, productivity, financial, and messaging services.
Researchers named the toolset PCPJack. Notably, the framework does not deploy cryptominers, a significant departure from standard cloud attack methodologies.
Cloud Exploitation and Command Infrastructure
On April 28, 2026, SentinelLABS located a malicious script and subsequently identified the comprehensive credential theft framework. The initial infection vector relies on a script named bootstrap.sh. This script actively downloads functional payloads from an unauthorized Amazon S3 resource hosted at spm-cdn-assets-dist-2026.s3.us-east-2.amazonaws.com.
Once established, PCPJack actively targets and exploits exposed services across the network environment, including Docker, Kubernetes, Redis, MongoDB, RayML, and various vulnerable web applications.
On each compromised host, a script executes a shell pipeline that steals:
- .env files and config files
- Environment variables filtered for secrets, API keys, DB & SMTP creds
- SSH private keys and targets from known_hosts, ~/.ssh/config, and bash history
- AWS IMDS credentials
- Kubernetes service account tokens
- Docker secrets (/run/secrets/)
- Cryptocurrency wallets (wallet.dat files, Ethereum keystores, Solana keys)
To maintain operational persistence and direct the malware, the operators utilize Telegram for external command and control communication.
Secondary Toolset and Expanded Targeting
During the investigation, SentinelLABS also identified a second, distinct toolset hosted on the attacker’s primary payload server. This secondary deployment executes credential harvesting via the check.sh and extractor.py scripts, functioning alongside obfuscated Sliver binaries. It exfiltrates stolen data to a typosquatted domain, cdn.cloudfront-js.com.
Notable targeted services in the second toolset include Anthropic, Digital Ocean, Discord, Google API, Grafana Cloud, HashiCorp Vault, OnePassword, and OpenAI keys.
“Organizations can defend against these threats by adhering to cloud and web application security best practices”, the report advises.
A LiteLLM incident that impacted Mercor AI has been linked to TeamPCP. LiteLLM suspects that the compromise originated from the Trivy dependency used in its CI/CD security scanning workflow. Socket also noted that Trivy Docker images pushed to Docker Hub without corresponding GitHub releases contained infostealer IOCs associated with TeamPCP.
Last month, the GrafanaGhost exploit exfiltrated sensitive Grafana business data via indirect prompt injection.