CVE-2026-41940 Vulnerability in cPanel Exploited to Steal Credentials
- Critical cPanel vulnerability: CVE-2026-41940 maintains a 9.8 CVSS score and facilitates complete administrative privilege escalation.
- Global attack infrastructure: Threat intelligence analysis documented over 2,000 attacking source IP addresses across multiple geographies.
- Mr_Rot13 threat actor identification: The adversary deploys sophisticated multi-stage loaders, webshells, and cross-platform persistence mechanisms.
QiAnXin XLab has documented an active threat group, designated Mr_Rot13, exploiting CVE-2026-41940. The vulnerability impacting cPanel and WHM management infrastructure maintains a 9.8 CVSS score and enables unauthenticated remote authentication bypass, providing adversaries with complete administrative control.
Following public disclosure on April 28, 2026, XLab telemetry documented over 2,000 attacking source IP addresses distributed globally, with primary concentration in Germany, the United States, Brazil, and the Netherlands.
Payload Delivery Mechanism and System Compromise
On May 4, XLab identified a Go-based loader component named Payload. The loader incorporates Turkish debugging strings and exhibits characteristics consistent with AI-generated code segments.
During the execution phase, Payload retrieved a secondary component named Update from the command and control (C2) infrastructure “cp.dene.de.com.” The infector’s main tasks are:
- Modify the password of the compromised system,
- Implant SSH public keys, PHP webshells, and malicious JS code,
- Deploy filemanager remote control,
- Send sensitive device information and credentials back to the hacker.
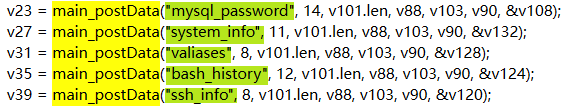
Ultimately, it steals bash history, SSH records, device information, database passwords, and Valiases configurations. The malware subsequently transmitted harvested credentials to “wrned.com” and an adversary-controlled Telegram communication channel.
Attacker Identification
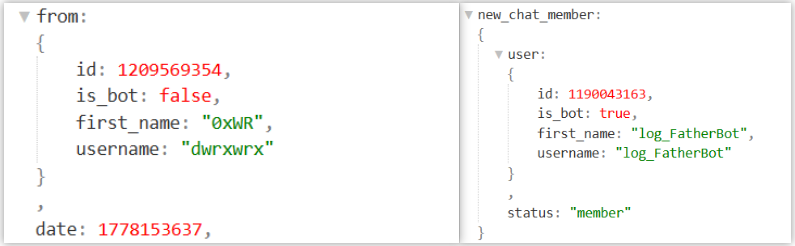
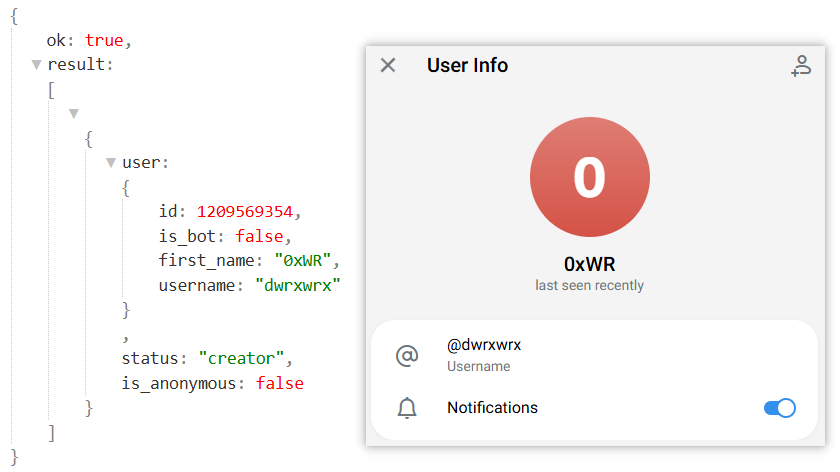
XLab designated the threat group Mr_Rot13 based on the Telegram handle 0xWR and the group's implementation of ROT13-obfuscated C2 communications. In addition to the primary infection vector, the adversaries deployed a cross-platform “filemanager” backdoor component.
Research analysis established an infrastructure correlation with a PHP backdoor with zero detections since 2022 that maintained communications with “wrned.com” – a domain that had been in use since 2020. This indicated a stable hacking group instead of opportunistic "hit-and-run" scriptsters.
The cPanel security update announced patches, and system administrators using cPanel and WHM must prioritize deploying emergency patches.
CVE-2026-41940 is currently under active mass exploitation, and forensic analysis indicates that it began as early as February 2026, significantly preceding public disclosure.