Hackers Mass-Exploit Critical cPanel Vulnerability May Impact 550,000+ Potentially Vulnerable Servers
- Server exposure: More than 550,000 cPanel servers remain potentially vulnerable to active threat actor exploitation.
- Ransomware deployment: Cybercriminals leverage this WHM exploit to hijack host systems and deploy file-encrypting malware.
- CISA issues directive: Organizations must patch CVE-2026-41940 immediately to prevent further network infiltration.
A cPanel vulnerability tracked officially as CVE-2026-41940 is currently under active mass exploitation. This unauthenticated flaw in cPanel and WebHost Manager (WHM) allows malicious actors to bypass security controls and execute a complete website compromise.
Currently, more than 550,000 internet-facing servers running cPanel remain exposed to the vulnerability, as per Shadowserver telemetry data cited by TechCrunch, with the number of actively compromised instances recently dropping from 44,000 to approximately 2,000.
Scope of the WHM Exploit
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the CVE-2026-41940 flaw to its Known Exploited Vulnerabilities (KEV) catalog on April 30.
“WebPros cPanel & WHM (WebHost Manager) and WP2 (WordPress Squared) contain an authentication bypass vulnerability in the login flow that allows unauthenticated remote attackers to gain unauthorized access to the control panel,” the CISA advisory said.
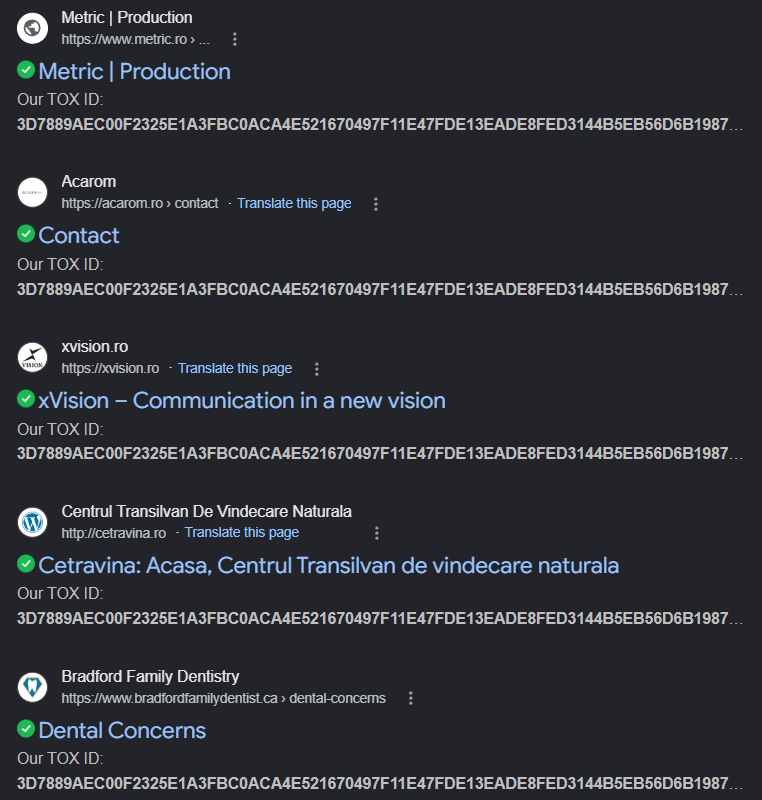
Threat actors are utilizing this WHM exploit to hijack vulnerable web hosting environments, with threat actors deploying Sorry ransomware designed specifically for Linux on several websites, some of which were indexed by Google.
Forensic analysis indicates that the exploitation of CVE-2026-41940 began as early as February 2026, significantly preceding public disclosure..
CISA Mandate and Remediation
System administrators utilizing cPanel and WHM architectures must prioritize emergency patch deployment, CISA mandated. Organizations must also rigorously audit their access logs for indicators of compromise to ensure threat actors have not already infiltrated their enterprise networks.
- Apply mitigations per vendor instructions,
- Follow applicable BOD 22-01 guidance for cloud services,
- Or discontinue use of the product if mitigations are unavailable.
The cPanel security update announced patches for:
- cPanel & WHM versions:
- 11.86.0.41 and higher
- 11.110.0.97 and higher
- 11.118.0.63 and higher
- 11.124.0.35 and higher
- 11.126.0.54 and higher
- 11.130.0.19 and higher
- 11.132.0.29 and higher
- 11.134.0.20 and higher
- 11.136.0.5 and higher
- WP Squared version:
- 136.1.7 and higher
In late April, ClickUp exposed 1,000 customer emails, including some belonging to government and corporate giants, and attackers breached a U.S agency via Cisco Firepower and Secure Firewall devices to distribute Firestarter malware.