Malicious NuGet Packages Target Chinese .NET Ecosystem Developers
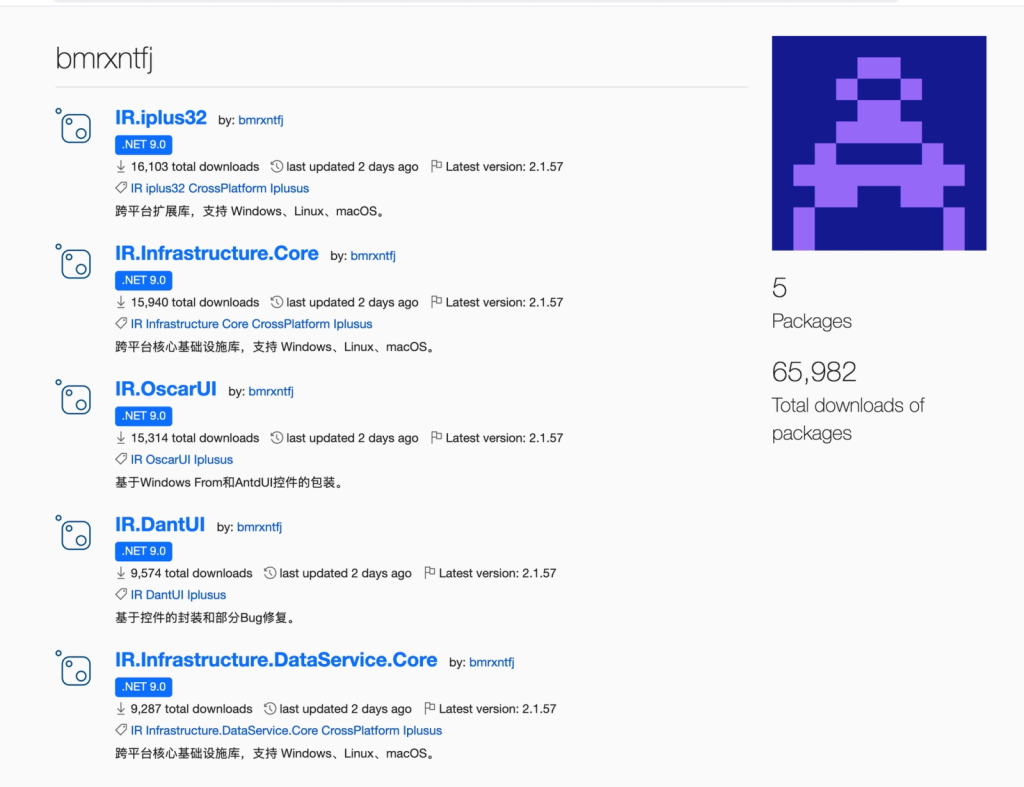
- Malicious NuGet packages: Five compromised packages impersonating Chinese .NET libraries under the publisher account bmrxntfj.
- Extensive data theft: The .NET Reactor-protected infostealer targets browsers, cryptocurrency wallets, SSH private keys, and system files.
- Widespread download impact: The packages accumulated approximately 65,000 downloads and remained available on the NuGet registry.
Five malicious NuGet packages were published under the account bmrxntfj. Cybersecurity researchers at Socket have discovered the IR.DantUI, IR.Infrastructure.Core, IR.Infrastructure.DataService.Core, IR.iplus32, and IR.OscarUI packages, which are actively impersonating legitimate Chinese .NET libraries, including AntdUI.
This supply chain campaign specifically targets developers operating within Chinese enterprise .NET ecosystems, exposing tens of thousands of developer workstations and CI/CD build servers to the risk of credential and crypto wallet theft.
Infostealer Payload and Evasion Tactics
The malicious packages are designed to deploy a sophisticated .NET Reactor-protected infostealer. The latest documented iteration, version 2.1.55 across all five packages, was published simultaneously on April 14, 2026. Across their entire version history, these packages have accumulated approximately 65,000 downloads.
The threat actor utilized extensive version manipulation to avoid detection; of the 224 total versions published, 219 were configured with a "listed: false" status. The infostealer targets 12 web browsers, 8 desktop cryptocurrency wallets, and 5 browser wallet extensions, the Socket report said. It harvests:
- sensitive credentials,
- enterprise assets,
- SSH private keys,
- Outlook profiles,
- Steam session configurations,
- local files stored within the user's Documents, Desktop, and Downloads directories.
All exfiltrated data is transmitted to the campaign's primary command-and-control (C2) domain, dns-providersa2.com, which was registered on March 12, 2026.
Risk Mitigation
At the time of writing, all five malicious packages remained accessible on the NuGet repository. Socket has officially submitted takedown requests to the registry's security team to neutralize the ongoing threat.
Developers are advised to install legitimate upstream libraries directly from their canonical NuGet identities and publishers and rotate all credentials accessible from compromised machines – browser-saved passwords, API keys, SSH private keys, cryptocurrency wallet seeds, and cloud provider credentials.
Security teams should add the following to the detection stack:
- Block or alert on any DNS resolution of dns-providersa2[.]com.
- Alert on any outbound connection to 62[.]84[.]102[.]85.
- Alert on file creation at C:\\ProgramData\\Microsoft OneDrive\\keys.dat. Legitimate OneDrive never writes this file.
- Alert on CoCreateInstance calls requesting the Microsoft Edge IElevator interface (IID {c9c2b807-7731-4f34-81b7-44ff7779522b})by any process outside the Edge browser family.
- Alert on CI or build machines loading any DLL matching the five SHA-256 hashes in the IOC section.
- Flag outbound HTTP requests carrying headers matching X-[a-z]{3} with a short random value from build or developer machines, which is the stealer's per-request C2 header obfuscation pattern.
Meanwhile, an April report said China-nexus threat activity increased by 75% last year, and in March, the EU sanctioned Iranian and Chinese firms for cyberattacks against European networks.