IPVanish DSAR Process Explained: Access, Security Flow
- IPVanish DSAR Process: Secure portal, email verification required, requests processed quickly after confirmation, often within 24 hours
- Verification and Security: Identity checks prevent unauthorized access, deletion, or misuse of user accounts and personal data
- Privacy and Transparency: No-logs policy maintained, limited signup data collected, ongoing audits and transparency reporting ensured
IPVanish has shared new details about how it handles Data Subject Access Requests (DSARs), outlining its internal process for users who want to access or delete their personal data. The company emphasized a structured approach focused on security, transparency, and compliance with global privacy standards.
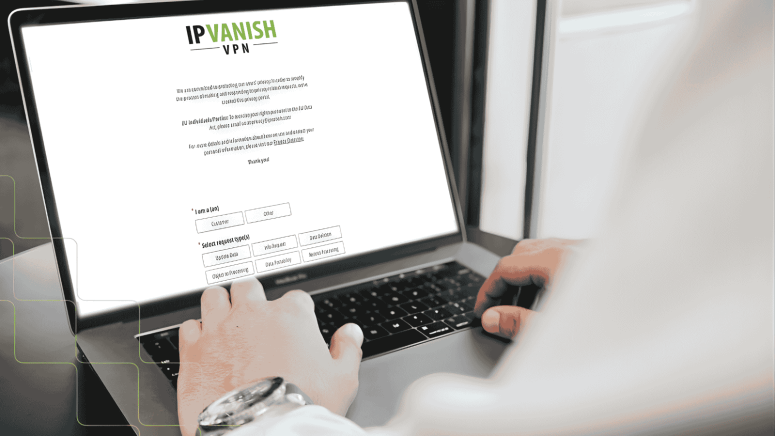
According to the announcement, users can submit requests through a dedicated Privacy Portal, where all requests are verified and processed, often within the same day once identity confirmation is completed.
Clear Process for User Data Requests
IPVanish states that its system is designed to give users full control over their data. Whether users want to review the information linked to their account or request deletion, the company provides a standardized workflow to handle such requests securely.
With increasing awareness of privacy laws such as the CCPA and GDPR, DSAR submissions have become more common. IPVanish says its process is built to meet these regulatory expectations while ensuring that requests are handled accurately and safely across all regions it operates in.
Verification Step Aimed at Preventing Misuse
A key part of IPVanish’s DSAR handling process is identity verification. After a request is submitted through the Privacy Portal, users must confirm their identity via email before any action is taken.
The company explains that this step is necessary to prevent unauthorized actions, such as:
- Accessing someone else’s personal data
- Deleting another user’s account
- Disrupting active subscriptions
If a user does not complete verification immediately, the request is placed on hold until confirmation is received.
Balancing Speed, Accuracy, and Security
Once verification is completed, IPVanish begins processing the request. While fast responses are often expected, the company notes that in privacy-related workflows, accuracy and security take priority.
Its approach focuses on three key principles:
- Ensuring the request comes from the correct user
- Providing complete and accurate data
- Completing requests as quickly as possible after verification
The company also highlighted that it does not compromise verification standards for faster turnaround times, unlike some providers that may streamline or skip certain checks.
No-Logs Policy and Data Collection Practices
IPVanish reiterated its no-logs policy, stating that it does not track, store, or monitor users’ browsing activity or VPN session data.
However, it clarified that certain limited information, such as the IP address used during account creation, may be collected. This data is used strictly for fraud prevention and payment validation and is not linked to VPN activity. The company adds that such data is anonymized if a user ends their service.
How Users Can Submit Requests
To submit a data request, users need to:
- Fill out the request form in the Privacy Portal
- Verify their request via email
- Wait for processing and confirmation, typically within 24 hours
IPVanish describes the system as both user-friendly and secure, ensuring that only legitimate requests are fulfilled.
Support for Global Privacy Rights
The company confirmed that it supports core privacy rights across all regions where it operates. Users can request deletion of their personal data at any time, regardless of location.
Additionally, users who wish to keep their accounts can request corrections to inaccurate information. In certain situations, IPVanish may retain limited data to comply with legal obligations, resolve disputes, or enforce agreements, in line with applicable laws.
Ongoing Focus on Transparency
IPVanish says it continues to refine its privacy practices and emphasizes transparency in how it manages user data. The company maintains that its processes are regularly reviewed through audits, transparency reporting, and disclosures available via its Trust Center.
The provider concluded by stating that privacy practices should be demonstrated through action, not just claims, and that its DSAR handling process is a key part of that commitment.