Bell Ambulance Breach Exposes Almost 240,000 Patients’ Data, Medusa Ransomware Claims Incident
- Significant Impact: The cyberattack on Bell Ambulance, Wisconsin's largest ambulance provider, compromised the sensitive data of almost 240,000 individuals.
- Data Compromised: Stolen information includes Social Security numbers, driver’s license numbers, financial account details, medical information, and health insurance data.
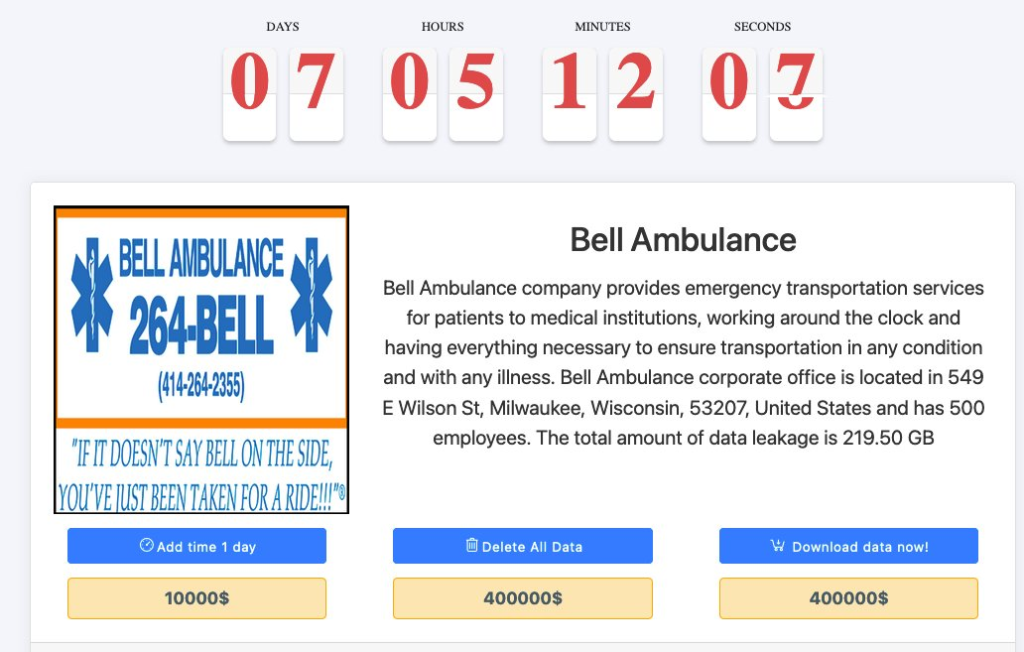
- Attribution: The Medusa ransomware gang claimed responsibility for the attack, demanding a $400,000 ransom for the 219 GB of exfiltrated data.
Bell Ambulance, the largest ambulance service provider in Wisconsin, has confirmed a significant cyberattack that resulted in a massive healthcare data breach. The incident, discovered in February 2025, compromised the personally identifiable information (PII) and protected health information (PHI) of 237,830 people.
This Bell Ambulance breach, which was claimed by the Medusa ransomware gang, is consistent with the group's established operational patterns.
Medusa Ransomware Gang's Involvement
The Bell Ambulance cyberattack was publicly claimed by Medusa, which listed the ambulance provider on its data leak site in March 2025 and demanded a $400,000 ransom to prevent the release of 219 GB of stolen data.
According to breach notification letters and the filing with the Maine Attorney General, the attackers successfully stole a wide array of sensitive data, including:
- Social Security numbers,
- financial account information,
- detailed medical and health insurance records.
Cybersecurity in Healthcare Implications
The Medusa group is a known ransomware-as-a-service (RaaS) operation that has been actively targeting critical infrastructure organizations, particularly within the healthcare industry. Federal law enforcement agencies have previously issued advisories regarding Medusa's tactics, which include data exfiltration followed by extortion and, in some cases, triple-extortion schemes.
Last year, RansomHub was linked to the Play, Medusa, and BianLian ransomware groups due to shared use of EDRKillShifter, and researchers revealed that modern Akira, Qilin, and Medusa cyberattacks leverage the Shanya Packer-as-a-Service (VX Crypt).
Just recently, a cyberattack on the U.S. medical giant Stryker that wiped employee devices was claimed by Handala, a threat actor historically linked to Iranian geopolitical interests.