AI Agents Now Utilized in Cyberattack Infrastructure Management: North Korean APTs Capitalize on This Evolution
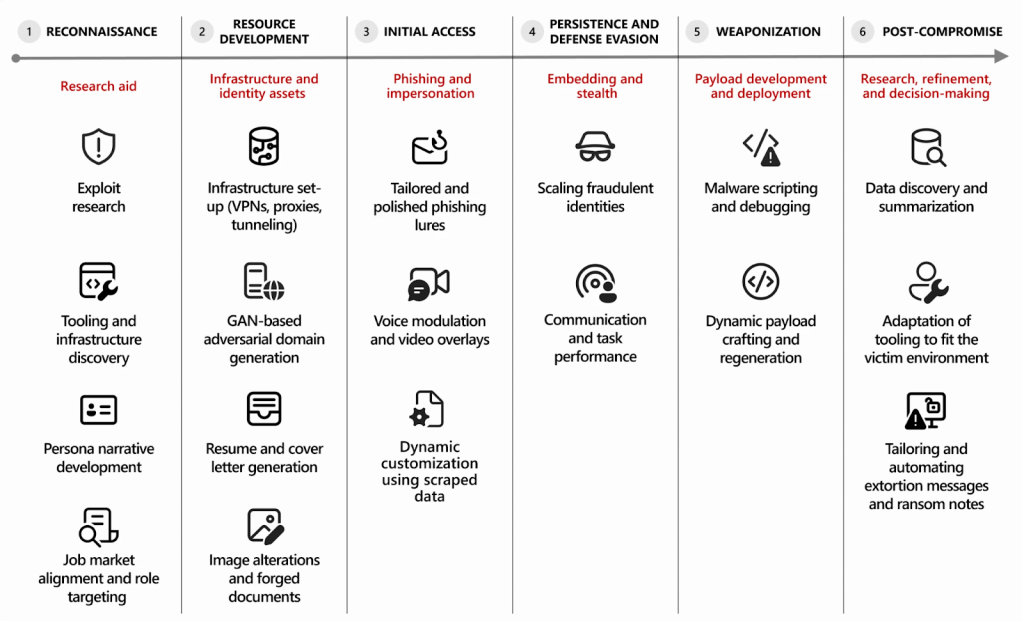
- Automation Work: Threat actors are now leveraging AI agents to automate and manage foundational cyberattack tasks, significantly increasing operational efficiency and speed.
- North Korean Actors: APTs have been observed using development platforms and AI to rapidly create and manage their attack infrastructure at scale.
- AI Integration into Malicious Tradecraft: This evolution in AI-enabled cybercrime lowers the technical barrier and enables more sophisticated, large-scale campaigns with less manual effort.
Advanced persistent threat (APT) groups are now using AI agents in cyberattacks to outsource and automate laborious, preparatory tasks, including conducting reconnaissance on compromised systems and, most notably, streamlining the management of attack infrastructure, Microsoft's threat intelligence division has reported.
By delegating this background work to AI, attackers can focus on higher-level strategic objectives, making their campaigns faster and more effective. A specific and concerning use case involves North Korea's cyber operations.
North Korea Cyber Operations Adopt AI
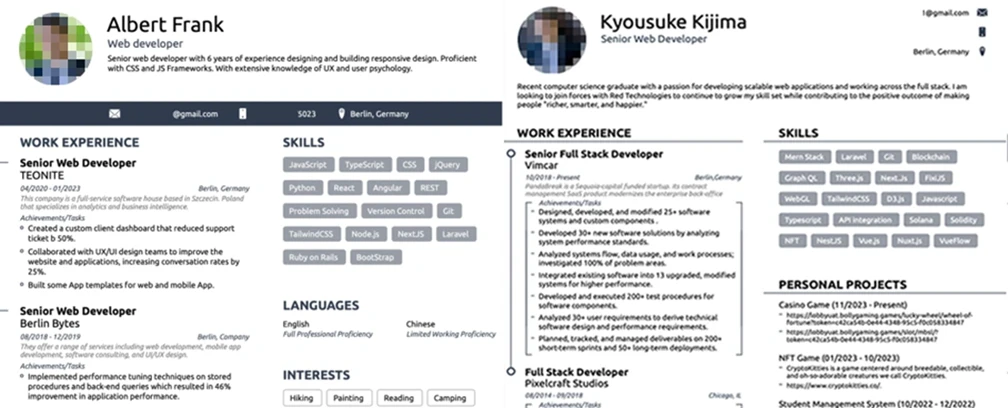
Microsoft has observed threat groups known as Jasper Sleet and Coral Sleet (formerly Storm-1877) misuse legitimate access through “identity fabrication, social engineering, and long‑term operational persistence.”
The use of AI agents enables more rapid campaign deployment, testing, and execution. In one example, hackers were seen employing role-based jailbreak techniques to bypass AI safety controls.
"We have always seen threat actors stand up the infrastructure, whether that means compromising existing legitimate infrastructure and using it for malicious purposes, or purchasing accounts and setting up their own infrastructure to launch threat campaigns," hs said Sherrod DeGrippo, Microsoft's GM of global threat intelligence.
- Coral Sleet uses development platforms to quickly create and manage convincing, high‑trust web infrastructure at scale, enabling fast staging, testing, and C2 operations. It also uses AI coding tools to generate, refine, and reimplement malware components and agentic AI tools to support a fully AI‑enabled workflow spanning end‑to‑end lure development. Notably, the actor has jailbroken LLM software to create new payloads.
- Jasper Sleet uses the Faceswap AI app and voice-changing software in fake IT worker job applications and leverages AI for reconnaissance when developing convincing digital personas.
Cybersecurity Implications of AI-Enabled Crime
The adoption of AI for infrastructure management presents serious cybersecurity implications. These powerful tools effectively lower the barrier to entry for less technically proficient criminals, while simultaneously amplifying the capabilities of APTs.
Security professionals must now contend with adversaries who can build and adapt their operational platforms with unprecedented speed. Microsoft offered support for Defender XDR customers to find potentially spoofed emails and suspicious sign-in attempts in their networks.
Last month, the North Korean threat actor Emerald Sleet was observed leveraging LLMs to research publicly reported vulnerabilities, including the CVE-2022-30190 Microsoft Support Diagnostic Tool (MSDT) vulnerability. A February Google report mentioned state-backed hackers use Gemini AI for cyberespionage.