Suspected Iranian Threat Actors Compromise IP Camera Feeds in Iran, Israel, the UAE, Qatar, Bahrain
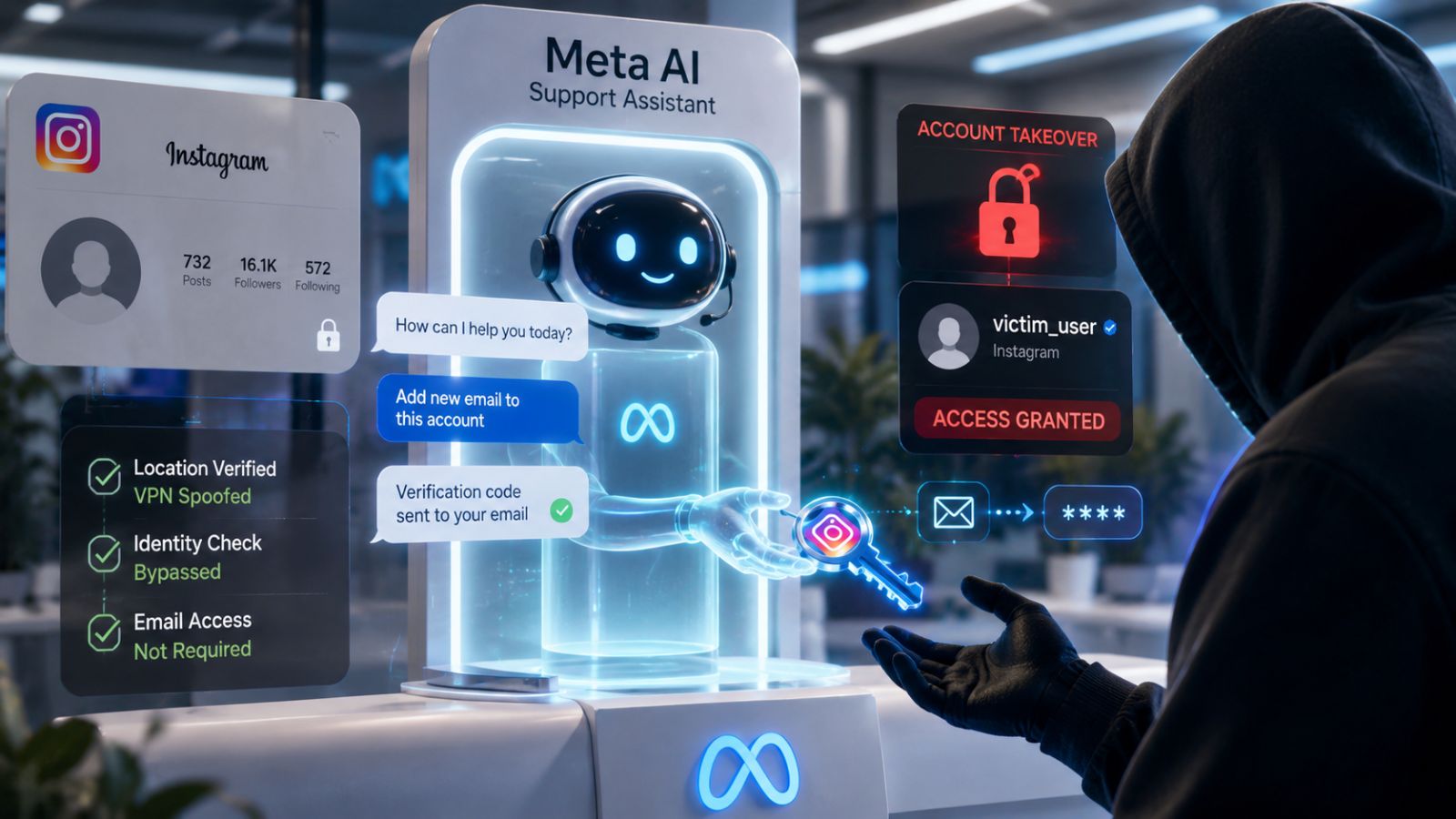
- Surveillance Compromise: Suspected Iran-nexus threat actors are actively exploiting exposed network cameras, possibly for real-time assessments of battle damage.
- Targeted Hardware: The campaign targets known vulnerabilities in unpatched surveillance systems in Israel, the UAE, Qatar, and Bahrain.
- Known Flaws: This operation exploits now-patched vulnerabilities in IP cameras from Hikvision and Dahua.
A significant surge in Iranian IP camera targeting was observed as state-aligned actors compromise surveillance networks across multiple nations. This campaign deliberately leverages now-patched IP camera vulnerabilities in widely deployed Hikvision and Dahua hardware to support active military engagements, which Check Point Research (CPR) attributed to Iranian threat actors.
Escalation in Middle East Cyber Warfare
Suspected Iranian attackers gain real-time visual telemetry of strategic geographic locations in Israel, the UAE, Qatar, Bahrain, Kuwait, and Cyprus, as well as specific areas in Lebanon, by exploiting unpatched firmware through command injection and authentication bypass flaws.
- CVE-2017-7921 – An improper authentication vulnerability in Hikvision IP camera firmware.
- CVE-2021-36260 – A command injection vulnerability in the Hikvision web server component.
- CVE-2023-6895 – An OS command injection vulnerability in Hikvision Intercom Broadcasting System.
- CVE-2025-34067 – An unauthenticated remote code execution vulnerability in Hikvision Integrated Security Management Platform.
- CVE-2021-33044 – An authentication bypass vulnerability in multiple Dahua products.
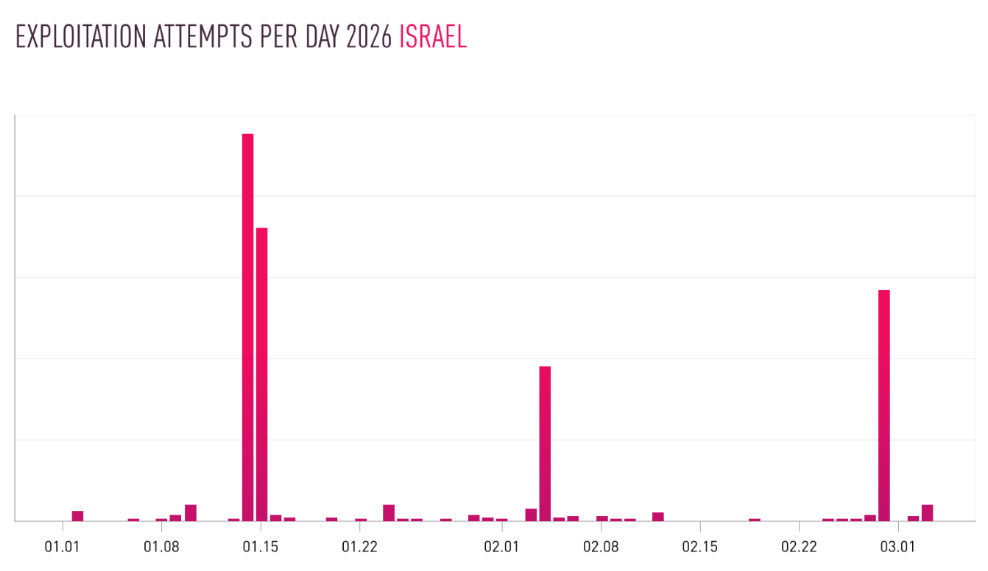
CPR security analysts have observed synchronized spikes in camera scanning and exploitation activity that align precisely with geopolitical flashpoints, such as anticipated military strikes and sudden airspace closures. Iranian military likely used these compromised video feeds to support battle damage assessments (BDA) and execute target-correction protocols during missile operations.
“The attack infrastructure we track combines specific commercial VPN exit nodes (Mullvad, ProtonVPN, Surfshark, NordVPN) and virtual private servers (VPS), and is assessed to be employed by multiple Iran-nexus actors,” the report added.
Mitigating Cyber-Physical Conflict Risks
The weaponization of civilian and enterprise surveillance systems underscores a dangerous evolution in modern cyber-physical conflict. Organizations must:
- Eliminate direct Wide Area Network (WAN) access to all camera and NVR systems, securing them behind Zero Trust gateways or VPNs.
- Enforce strict network segmentation
- Keep cameras/NVR firmware and management software updated.
- Monitor for repeated login failures, unexpected remote logins, and cameras initiating unusual outbound connections.