Two New Jersey Individuals Sentenced to Prison in North Korea IT Worker Scheme
- New Jersey sentencing: Two men received significant federal prison terms for orchestrating a North Korea WMD funding scheme.
- Stolen identities exploited: The operation utilized compromised profiles to secure identity theft IT jobs at major U.S. corporations.
- Severe cybersecurity risks: Overseas actors gained access to sensitive military data and proprietary source code.
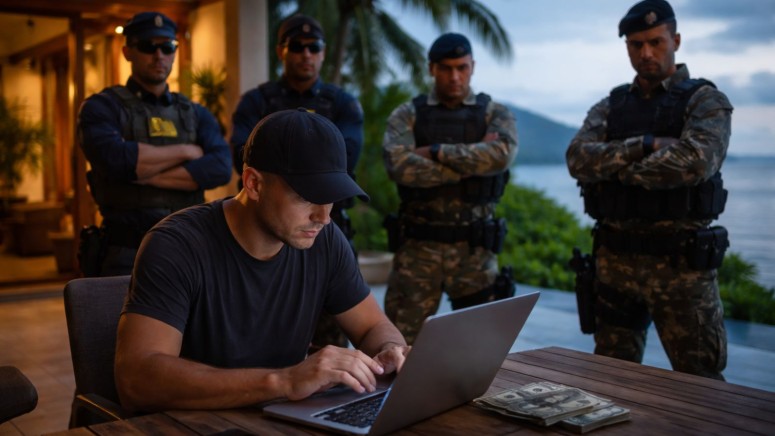
Two individuals involved in a sophisticated North Korea weapons of mass destruction (WMD) funding scheme were handed down prison sentences by a Boston federal court. This operation systematically exploited corporate hiring frameworks to channel illicit revenue to the Democratic People's Republic of Korea (DPRK).
They secured identity theft IT jobs at more than 100 U.S. enterprises, including Fortune 500 organizations and an artificial intelligence defense contractor.
Identity Theft Operation
Kejia "Tony" Wang, 42, and Zhenxing "Danny" Wang, 39, engineered a multi-year conspiracy that compromised the data of over 80 U.S. citizens. The New Jersey sentencing mandated nine years in federal prison for Kejia Wang and 92 months for Zhenxing Wang, the U.S. Department of Justice recently announced.
“For years, the defendants enriched themselves by assisting North Korean actors in a fraudulent scheme to gain employment with U.S. companies,” said Assistant Attorney General for National Security John A. Eisenberg.
The perpetrators established shell companies, including Hopana Tech LLC, Tony WKJ LLC, and Independent Lab LLC, to legitimize overseas operatives, which authorities now seized. Both facilitators hosted hardware devices, specifically keyboard-video-mouse (KVM) switches, enabling remote network access for North Korean workers while actively masking their true geographic locations.
The defendants were charged in June 2025, along with eight overseas operatives who remain at large. A reward is offered for the following eight defendants who are alleged to have participated in the scheme, and one suspected IT worker:
- Xu Yongzhe (徐勇哲)
- Huang Jingbin (黄靖斌)
- Tong Yuze (佟雨泽)
- Zhou Baoyu (周宝玉)
- Yuan Ziyou (Samuel Yuan)
- Zhou Zhenbang (周震邦)
- Liu Menting (劉孟婷)
- Liu Enchia (刘恩嘉)
- Song Min Kim (a.k.a. Chengmin Jin)
Elevating National Cybersecurity Risks
This coordinated breach generated over $5 million for the DPRK government while inflicting at least $3 million in remediation and legal damages upon victimized networks. In one confirmed instance, an overseas operative successfully accessed International Traffic in Arms Regulations (ITAR) data between on or about January 19, 2024, and on or about April 2, 2024.
Enterprise network administrators and compliance officers must implement rigorous identity verification and hardware auditing protocols to prevent state-sponsored threat actors from infiltrating secure infrastructure environments.
In December, Amazon announced blocking over 1,800 suspected North Korean IT operatives from securing remote roles. Reports in October warned that this scheme had expanded to the UK, Canada, and Germany.
In July 2025, a U.S. resident was sentenced for leading the IT worker fraud scheme, and one month later, the US Treasury sanctioned two people and two companies associated with the scheme.