PIA Q4 Report Shows it Received 30 Legal Requests in Q4 2025 but Produced No User Data – Know Everything
- Private Internet Access transparency Q4 report findings: Company received 30 legal requests but produced zero user data due no-logs policy enforcement authorities.
- Independent audit verification: Deloitte audit confirmed VPN servers, management systems, and dedicated IP technology follow privacy policies requirements.
- Bug bounty and security trends: Fourteen submissions received, one valid issue fixed, broader incidents highlight ongoing cybersecurity risks worldwide concerns.
Private Internet Access (PIA) has published its transparency report for the fourth quarter of 2025, covering the period between October and December. The report outlines the number and type of legal requests the company received and confirms that none resulted in user data disclosure.
Transparency reports are released regularly by the company to inform users about government, law enforcement, and civil requests for information, as well as how those requests are handled.
Legal Requests Increased Compared to Previous Quarter
During Q4 2025, PIA received a total of 30 legal requests from authorities in the United States and other countries. This marked an increase from 19 requests in the previous quarter.
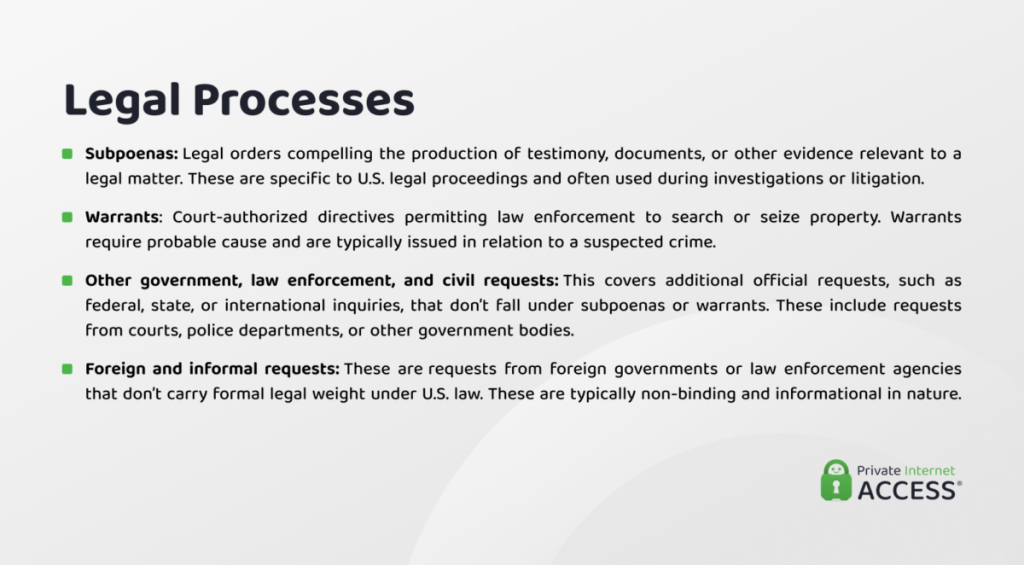
The breakdown of requests received during the quarter includes:
- Subpoenas: 7 received, 0 logs produced
- Warrants: 1 received, 0 logs produced
- Other government, law enforcement, and civil requests: 10 received, 0 logs produced
- Foreign and informal requests: 12 received, 0 logs produced
Subpoenas remained the most common type of legal request, although their number slightly decreased compared to the previous quarter. The overall rise in requests was mainly due to an increase in government and civil requests, as well as foreign and informal inquiries. The company also reported receiving one warrant during this period.
Despite the higher volume and broader range of legal requests, the outcome stayed the same. PIA stated that it did not provide any user data because it does not store activity logs. As a result, there was no information available to share with requesting authorities.
The company continues to use a simplified reporting format introduced earlier in 2025. This format groups certain legal requests together and separates foreign and informal requests due to their different legal status under U.S. law.
Independent Audit Confirms No-Logs Policy
PIA also announced that it completed its third independent audit during the quarter. The audit was conducted by Deloitte Audit Romania under the ISAE 3000 (Revised) assurance standard.
The audit reviewed several key areas, including:
- VPN server configurations
- Internal management systems
- Token-based dedicated IP infrastructure
According to the report, the audit confirmed that PIA’s server setup and systems align with its stated privacy policies. This independent review serves as external validation of the company’s no-logs policy, confirming that its infrastructure is designed in a way that prevents the storage of user activity data.
Bug Bounty Program Identified One Valid Security Issue
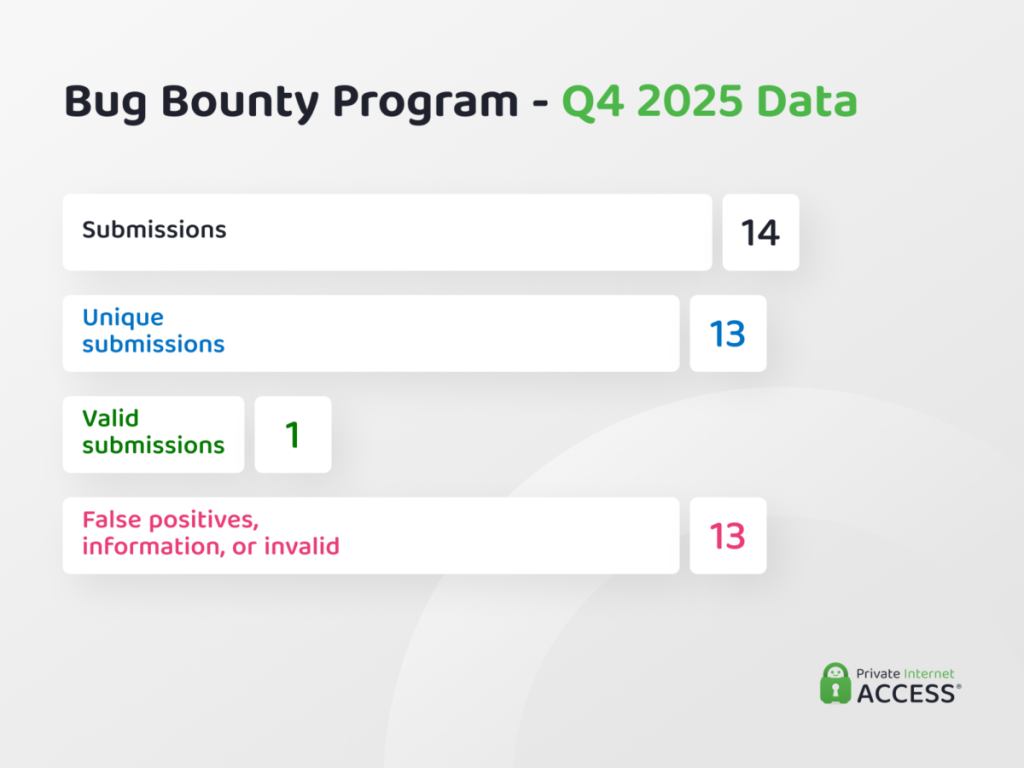
PIA’s bug bounty program, which allows external researchers to report security vulnerabilities, received 14 submissions during Q4 2025. Of these, 13 were unique reports.
Only one submission was identified as a genuine security issue, and the company addressed it. The remaining reports were classified as false positives and did not reveal any exploitable vulnerabilities.
Although the total number of submissions declined compared to the previous quarter, the program continued to provide focused testing. The company said the findings reflect targeted security reviews designed to identify meaningful issues.
Major Security Incidents Highlight Broader Privacy Risks
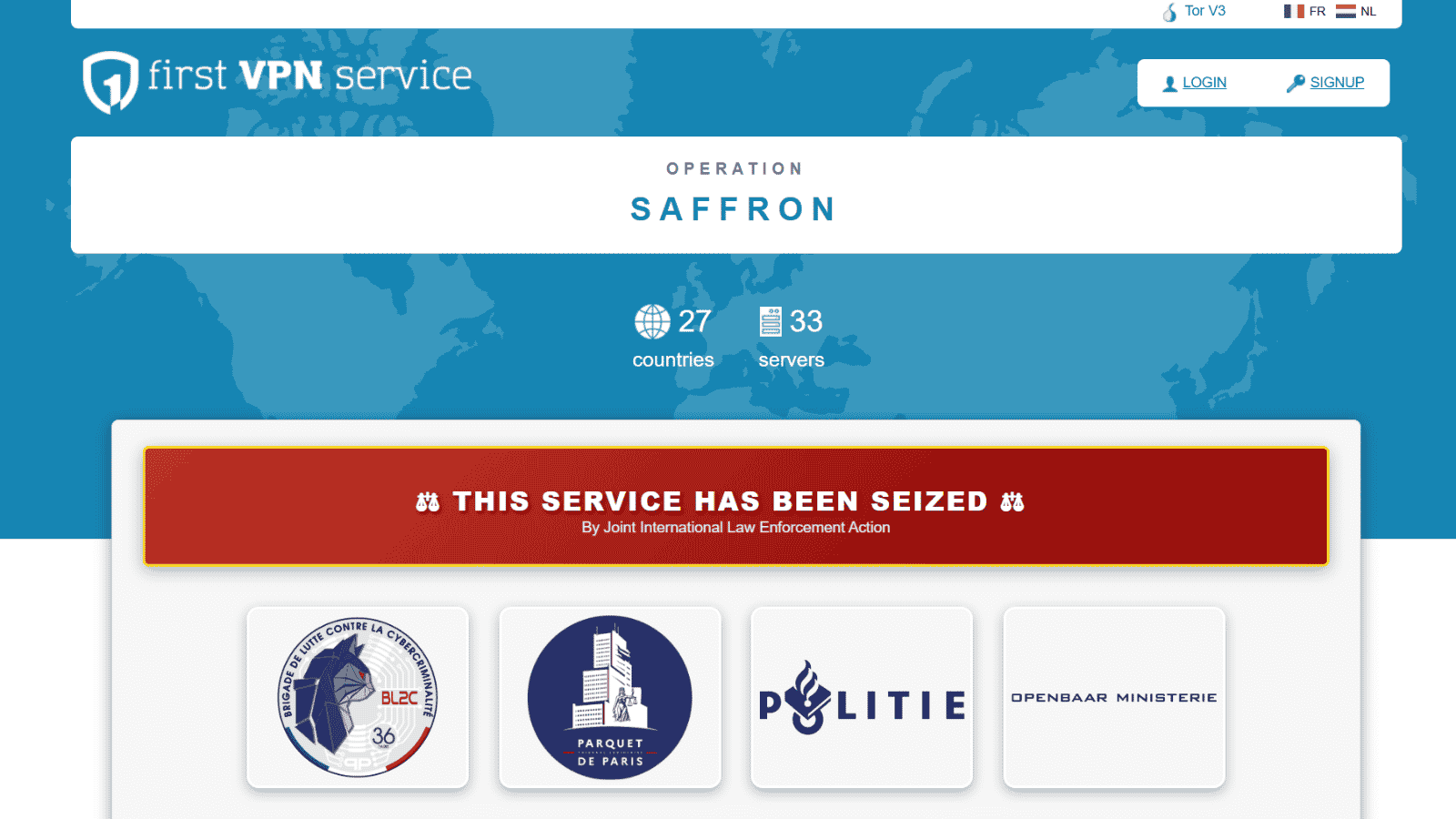
The report also pointed to several major cybersecurity incidents during late 2025 and early 2026 that demonstrate ongoing risks to user data across the internet.
One ongoing issue involved organizations affected by the breach of Oracle Corporation’s Oracle E-Business Suite platform. More than 100 organizations, including universities and large companies, continued to face ransom and data exposure threats months after the initial breach was disclosed. Attackers reportedly threatened to release stolen personal and financial information.
Another incident involved BreachForums, an underground hacking community. In early January, an archive containing around 324,000 user records was leaked. The exposed data included usernames, registration details, and public IP address information linked to many accounts.
Security researchers also reported over 91,000 automated attack attempts targeting misconfigured proxies connected to large language model infrastructure between October 2025 and January 2026. These attacks attempted to locate exposed AI systems and exploit weak configurations.
In addition, stolen login credentials and account takeovers became one of the leading causes of security breaches in the U.S., surpassing malware in many cases. Security analysts attributed this trend to password reuse, phishing campaigns, and attacks designed to overwhelm multi-factor authentication protections.
Overall, PIA’s transparency report for Q4 2025 shows an increase in legal requests but no change in its handling of user data. The company maintains that its systems do not log user activity, making it technically unable to provide such information even when requests are received.