US Authorities’ Actions Result in Arrest, Indictments in IT Worker Scheme Funding North Korea
- One individual was arrested and eight indicted for allegedly participating in illegal activities that funded North Korea.
- DOJ announced critical charges, asset seizures, and the dismantling of fraudulent infrastructure.
- North Korean IT workers accessed sensitive employer data, stole cryptocurrency, and more.
Nine individuals were indicted in Boston, Massachusetts, with one of them arrested, for cyber schemes tied to the Democratic People's Republic of Korea (DPRK), aiming to thwart illicit activities funding the regime's programs, including its weapons initiatives.
One New Jersey man and eight overseas actors from China and Taiwan were connected to an alleged scheme to generate revenue for the DPRK's weapons of mass destruction (WMD) programs, the U.S. Department of Justice (DOJ) announced.
Authorities revealed that North Korean individuals fraudulently obtained employment as remote IT workers for over 100 U.S. companies, using stolen or falsified identities. Investigations uncovered the use of shell companies, fraudulent websites, and financial networks to launder funds back to the DPRK regime.
Simultaneously, U.S. officials seized 29 financial accounts, dismantled 21 fraudulent websites, and executed searches at suspected "laptop farm" locations across 16 states. Over 70 laptops, remote access devices, and critical evidence were recovered.
The following defendants have been indicted for their roles in the scheme, which generated at least $5 million in revenue for North Korea:
- U.S. national Zhenxing “Danny” Wang of New Jersey – arrested
- Chinese national Jing Bin Huang (靖斌 黄);
- Chinese national Baoyu Zhou (周宝玉);
- Chinese national Tong Yuze (佟雨泽);
- Chinese national Yongzhe Xu (徐勇哲 andيونجزهي أكسو), currently residing in the United Arab Emirates;
- Chinese national Ziyou Yuan (زيو), currently residing in the United Arab Emirates;
- Chinese national Zhenbang Zhou (周震邦);
- Taiwanese national Mengting Liu (劉 孟婷); and
- Taiwanese national Enchia Liu (刘恩)
Zhenxing "Danny" Wang was arrested for involvement in facilitating these schemes. Wang and co-conspirators allegedly funneled millions through fake companies, disguising remote workers as legitimate employees.
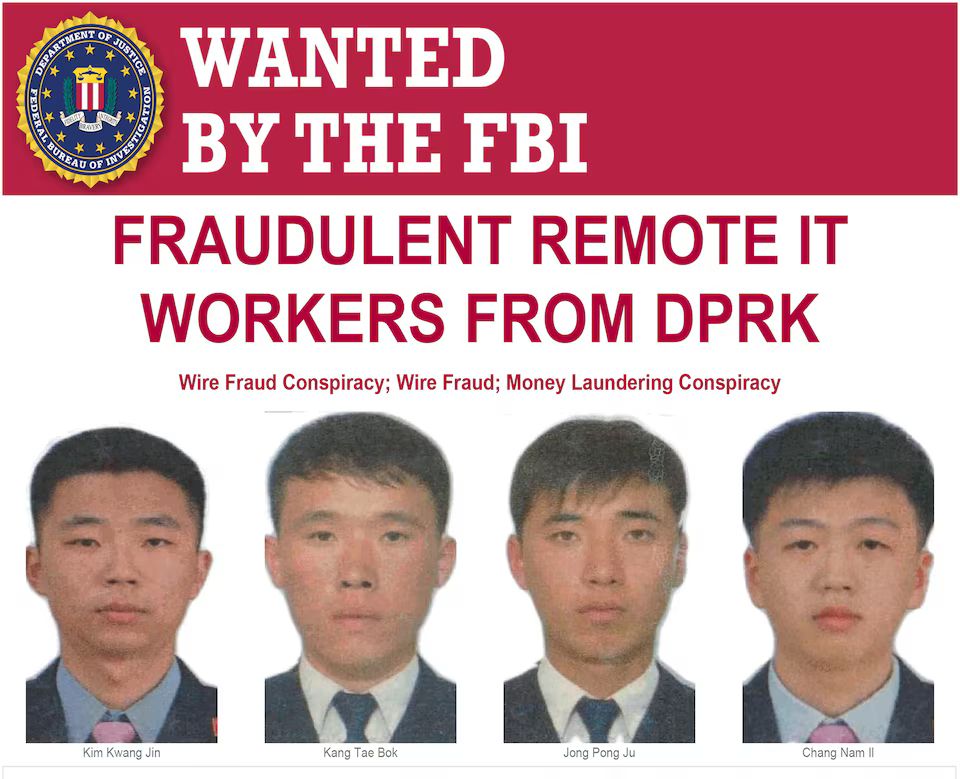
North Korean nationals Kim Kwang Jin, Kang Tae Bok, Jong Pong Ju, and Chang Nam Il have been charged in a five-count wire fraud and money laundering indictment.
These individuals, supported by collaborators in the U.S, China, the UAE, and Taiwan, orchestrated sophisticated schemes that included hosting "laptop farms" to bypass geolocation restrictions.
North Korean IT workers not only collected millions in salary payments but also accessed sensitive employer data, including export-controlled military technology and cryptocurrency theft amounting to $900,000 from a blockchain company.
The FBI, Defense Criminal Investigative Service (DCIS), and Homeland Security Investigations (HSI) played key roles in unraveling these networks.