Amazon SES Phishing and BEC Attacks Leverage Leaked AWS IAM Keys
- Trusted platforms weaponized: Threat actors leverage Amazon SES to execute highly evasive phishing campaigns that bypass conventional filtering mechanisms.
- Exposed credentials exploited: Scammers hijack leaked AWS IAM keys from public repositories to access the cloud-based email delivery service.
- Advanced threat tactics: The compromised infrastructure facilitates sophisticated BEC attacks utilizing fabricated communication threads to execute financial fraud.
Cybersecurity analysts have identified a significant escalation in Amazon SES phishing operations. Threat actors increasingly weaponize the Amazon Simple Email Service (SES) to distribute malicious payloads and execute advanced social engineering schemes, exploiting the platform's inherent trustworthiness to circumvent enterprise email security perimeters.
Abuse of AWS IAM Keys, BEC Attacks, and Financial Fraud
Attackers initiate these campaigns by scanning public repositories, configuration backups, and Docker images for exposed AWS IAM (Identity and Access Management) keys, according to SecureList by Kaspersky. Once authenticated, cybercriminals utilize the legitimate Amazon SES infrastructure to deploy massive volumes of fraudulent emails, which pass standard SPF, DKIM, and DMARC validation checks.
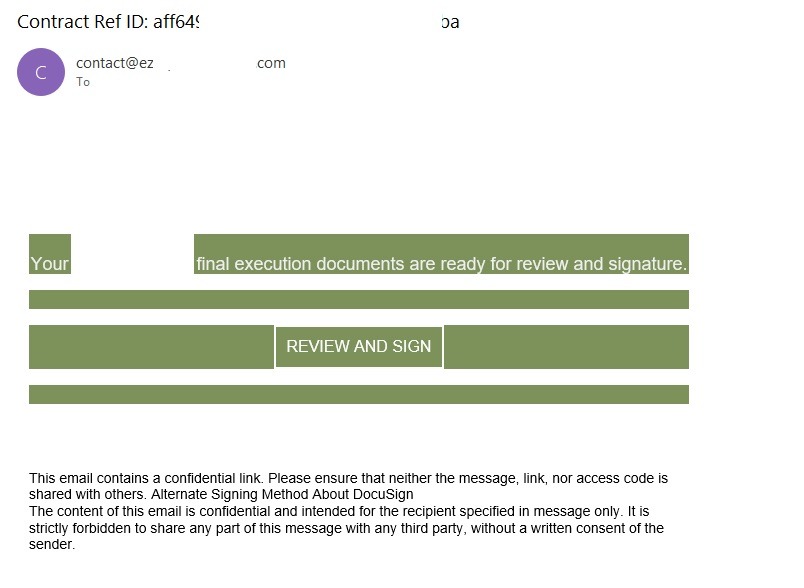
“In early 2026, one of the most common themes in phishing emails sent with Amazon SES was fake notifications from electronic signature services,” the report said.
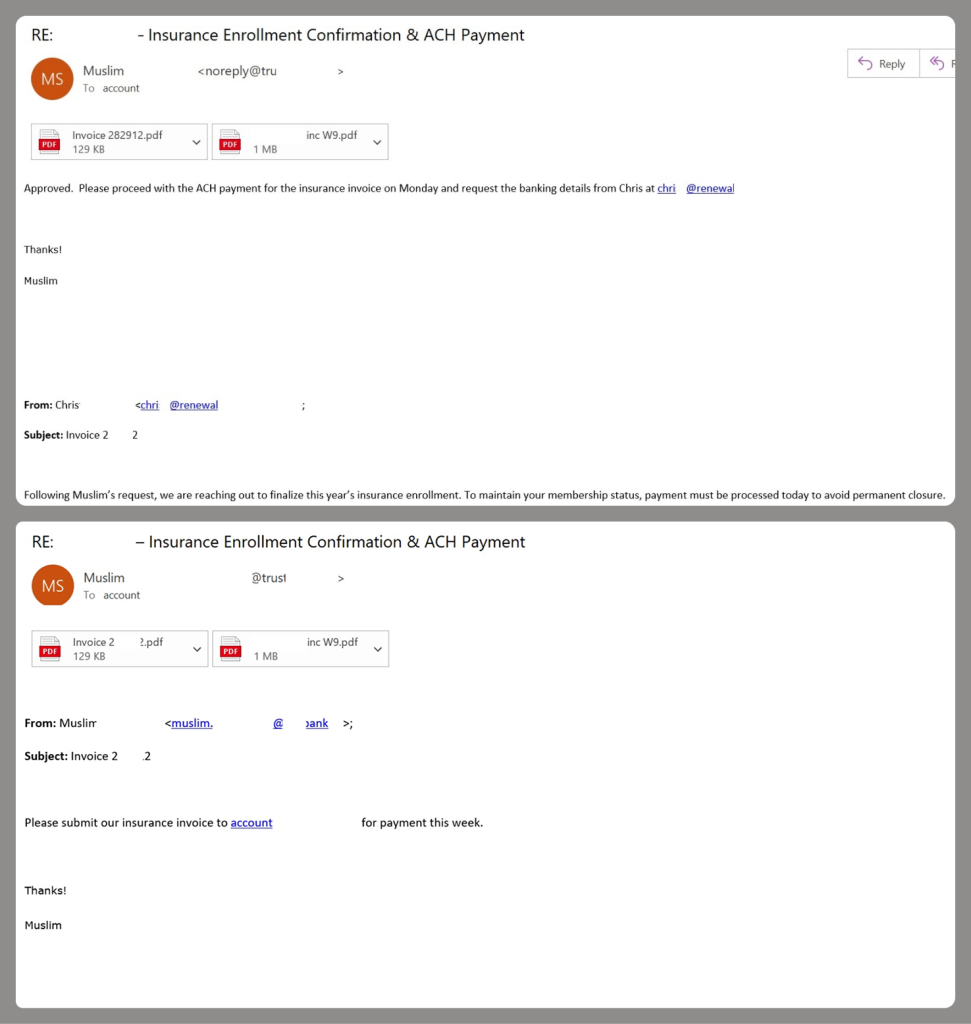
Beyond standard credential harvesting, adversaries utilize this compromised infrastructure to orchestrate highly sophisticated business email compromise (BEC) attacks.
In documented incidents, threat actors fabricated complex, multi-message email threads between corporate employees and external vendors regarding invoices. The emails’ PDF attachments only contained payment details and supporting documentation, successfully deceiving finance departments into executing unauthorized wire transfers.
Risk Mitigation
Amazon SES phishing attacks stem from compromised or leaked AWS credentials, so the first step is to prioritize the security of these accounts. To mitigate these risks, SecureList recommends following these guidelines:
- Implement the principle of least privilege when configuring IAM access keys.
- Transition from IAM access keys to roles when configuring AWS.
- Enable multi-factor authentication, an ever-relevant step.
- Configure IP-based access restrictions.
- Set up automated key rotation and run regular security audits.
- Use the AWS Key Management Service to encrypt data with unique cryptographic keys and manage them from a centralized location.
In December 2025, Amazon EC2 and ECS were targeted in a cryptomining campaign using compromised IAM credentials.