Russian Hackers Target 13,500 Signal Accounts in Hijacking Campaign
- Targeted Phishing Attack: Russian hackers targeted over 13,500 Signal users in an extensive espionage operation.
- Automated Compromise System: The ApocalypseZ infrastructure facilitated bulk account hijacking and data exfiltration.
- Security Mitigation Strategy: Security experts strongly advise enabling the Signal Registration Lock feature.
A targeted phishing attack directed at the personal Signal account of Donncha Ó Cearbhaill, head of Amnesty International’s Security Lab, was recently intercepted. Following the initial intrusion attempt, Ó Cearbhaill investigated the attack vector and determined that he was likely one of more than 13,500 targets in an ongoing cyberespionage operation.
Mass Exploitation and the ApocalypseZ System
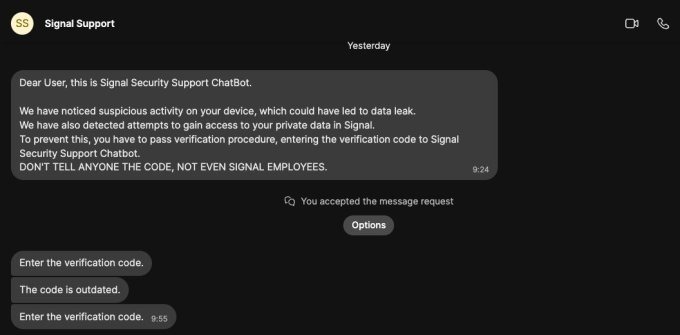
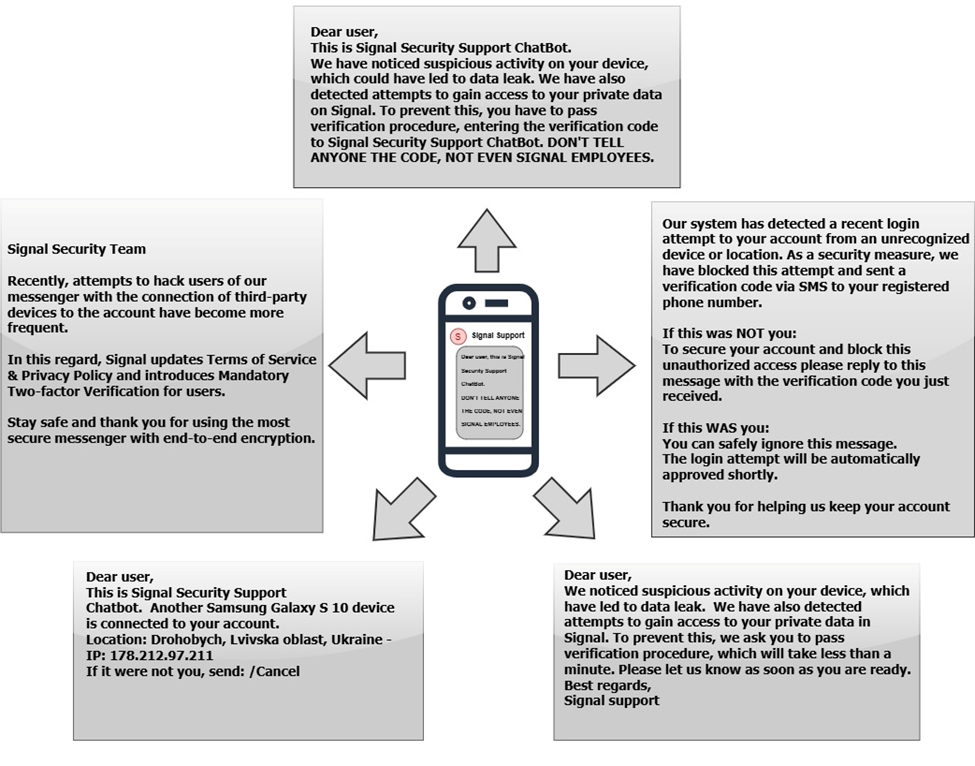
The malicious communication impersonated a "Signal Security Support ChatBot," attempting to manipulate the security researcher into divulging an authentication verification code. The operational objective was to hijack their Signal account by covertly linking it to a secondary device controlled entirely by the attackers.
During their technical analysis, he identified the underlying infrastructure driving the bulk attacks as an automated system named "ApocalypseZ," according to TechCrunch. The investigation revealed that both the codebase and the operator interface were written in Russian.
Additionally, the system was configured to automatically translate intercepted victim communications into Russian. The specific methodologies observed in this incident match a broader cyber threat campaign formally attributed to Russian government spies.
Global Intelligence Warnings and Mitigations
Multiple international intelligence organizations, including the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the UK’s cybersecurity agency, and Dutch intelligence, along with Signal, have issued official warnings about these specific hijacking techniques.
The threat has demonstrated substantial real-world impact; Der Spiegel reported that the campaign successfully compromised several individuals in Germany, including high-profile politicians.
To mitigate the risk of unauthorized device linking and account takeover, Ó Cearbhaill recommends that all users immediately enable the Signal Registration Lock feature to secure their communication infrastructure.
Last month, the EU sanctioned Russian propaganda networks Euromore and Pravfond with asset freezes.