Kimsuky PebbleDash and AppleSeed Malware Campaigns
- Targeted sectors: Operations focused on South Korean entities, alongside defense targets in Brazil and Germany.
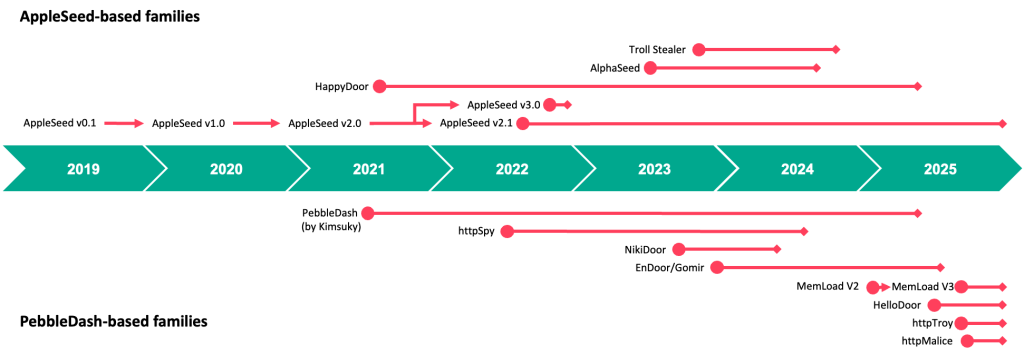
- Malware variants: Threat actors deployed HelloDoor, httpMalice, MemLoad, httpTroy, AppleSeed, and HappyDoor malware.
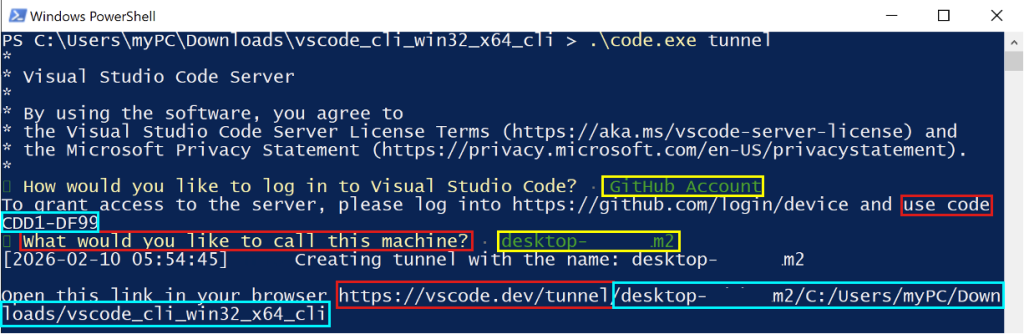
- Legitimate tools: Attackers abused VSCode tunneling, GitHub authentication, and DWAgent for post-exploitation.
A new suite of PebbleDash-based tools was linked to the AppleSeed malware cluster in observed campaigns attributed to the advanced persistent threat (APT) group Kimsuky, also recognized under the threat aliases APT43, Ruby Sleet, Black Banshee, Sparkling Pisces, Velvet Chollima, and Springtail.
The campaign disseminated backdoors such as HelloDoor, httpMalice, MemLoad, httpTroy, AppleSeed, and HappyDoor, leveraging legitimate tools such as VSCode and DWAgent.
Kimsuky Payload Delivery and Post-Exploitation
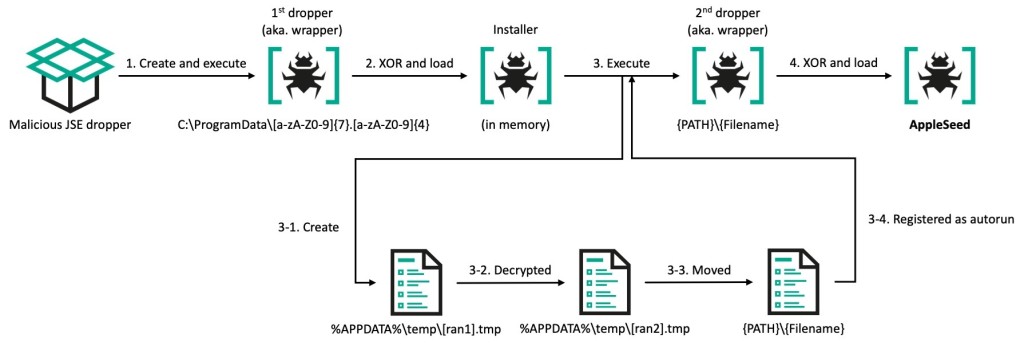
To secure initial access, Kimsuky utilized highly targeted spearphishing emails containing malicious attachments, occasionally leveraging instant messengers to initiate contact. Upon successful initial compromise, the operators utilized diverse droppers formatted as JSE, PIF, SCR, and EXE files, Kaspersky researchers have discovered.
These execution chains subsequently deployed multiple malware families into the target environments, specifically dropping the HelloDoor, httpMalice, MemLoad, httpTroy, AppleSeed, and HappyDoor variants to establish persistent backdoor access.
For post-exploitation persistence and covert command execution, Kimsuky abused legitimate infrastructure. The group leveraged Visual Studio Code (VSCode) tunneling combined with GitHub authentication mechanisms, alongside the remote administration tool DWAgent and Cloudflare Quick Tunnels.
Command-and-control (C2) communications were predominantly routed through free South Korean hosting domains to obfuscate malicious network traffic.
Global Targets and Sector Focus
The cyberespionage campaigns predominantly targeted public and private entities within South Korea. However, the geographic scope expanded as PebbleDash attacks emerged in Brazil and Germany, prioritizing organizations within the defense sector.
At the same time, the AppleSeed malware cluster demonstrated a distinct focus on compromising government organizations.
In October 2025, TigerJack malware was distributed via malicious VSCode extensions, infecting over 17,000 developers. In March 2026, a GitHub phishing campaign targeted developers with fake VS Code alerts urging them to patch fabricated CVEs.
Early this year, FBI warned a Kimsuky spearphishing campaign targeted the U.S. with malicious QR codes (quishing).
In other recent news, Suspected Belarusian state-nexus actors target Ukraine with a new Cobalt Strike cyberespionage campaign.