Google Ads and Claude.ai Shared Chats Abused to Distribute Mac Malware
- Malvertising campaign: Attackers abuse Google Ads and legitimate Claude.ai shared chats to push macOS malware.
- Terminal commands weaponized: Fake installation guides trick users into executing malicious shell scripts on their machines.
- MacSync variant: The payload systematically harvests browser credentials, cookies, and macOS Keychain contents.
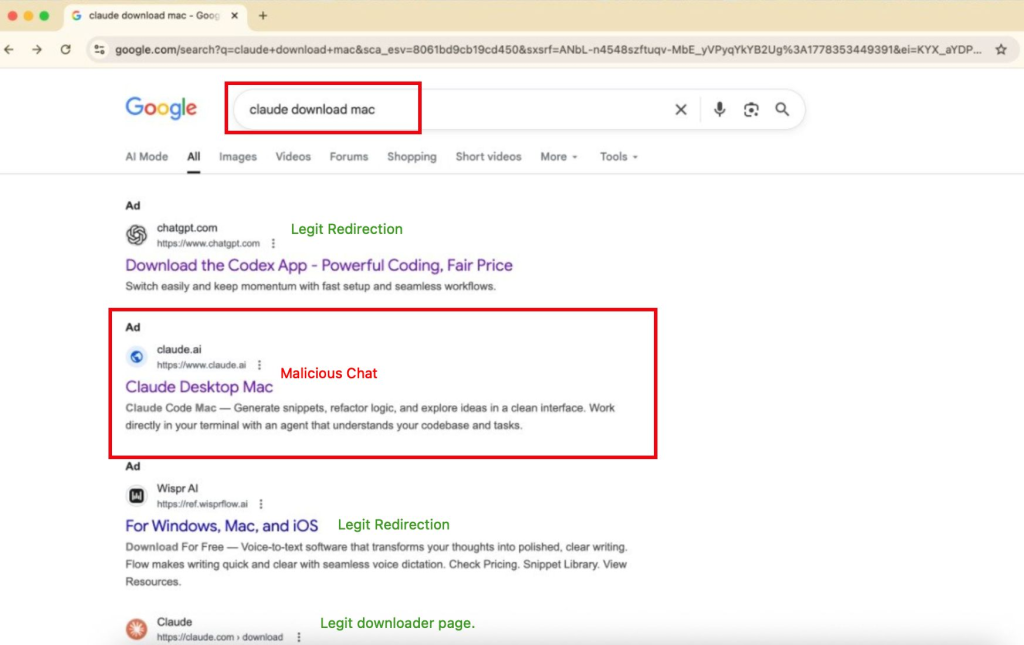
Attackers abuse Google Ads and legitimate Claude.ai shared chats to distribute malware targeting macOS systems in an active malvertising campaign. Individuals searching for "Claude mac download" may encounter sponsored search results that deceptively list claude.ai as the verified target website, cybersecurity researchers warn.
Weaponized Claude Shared Chats
The malvertising campaign was initially spotted by Berk Albayrak, a security engineer at Trendyol Group. Albayrak identified a specific Claude.ai shared chat that masqueraded as an official "Claude Code on Mac" installation guide, falsely attributed to Apple Support.
During subsequent verification, BleepingComputer discovered a second shared Claude chat operating through an entirely separate infrastructure. Both malicious chats remained publicly accessible at the time of writing.
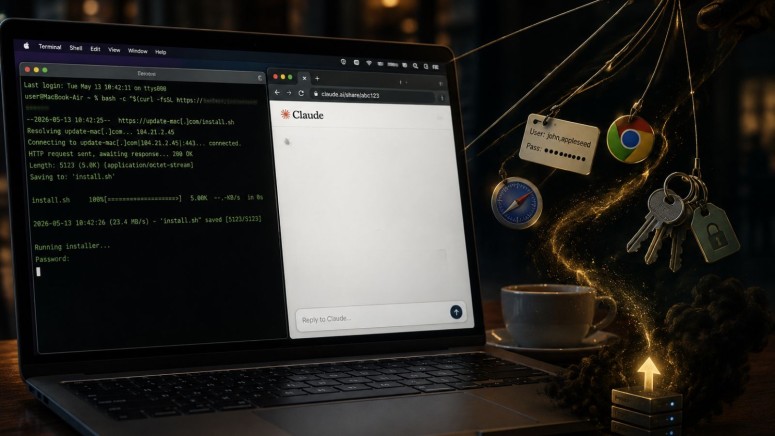
These weaponized chats utilize targeted social engineering, providing deceptive instructions that direct users to open the macOS Terminal and paste specific commands. Executing these commands silently downloads and runs malware on the host operating system.
Payload Execution and Data Exfiltration
The mac campaign deploys a couple of malware variants. One identified variant actively checks the compromised machine for Russian or CIS-region keyboard inputs. If the machine passes this geographic check, the script collects the victim's:
- external IP address,
- hostname,
- OS version,
- keyboard locale.
After transmitting this profiling telemetry to the attacker, it executes a second-stage payload through osascript, the built-in macOS scripting engine.
Albayrak identified another payload variant functioning as a MacSync macOS infostealer, which harvests browser credentials, session cookies, and highly sensitive macOS Keychain contents, transmitting the packaged data directly to the threat actor's command server.
In March, Claude Code was weaponized in a Mexican government cyberattack, exposing roughly 195 million identities. In November, 2025, Chinese state-sponsored GTG-1002 leverageed Claude AI and MCP for cyberespionage targeting tens of organizations.
Early last year, Amos Stealer was distributed to MacOS and Linux users via Google Ads tht promoted fake Homebrew site and a Google Ads phishing campaign targeted Microsoft advertisers.