Trellix Source Code Repository Breach Claimed by RansomHouse
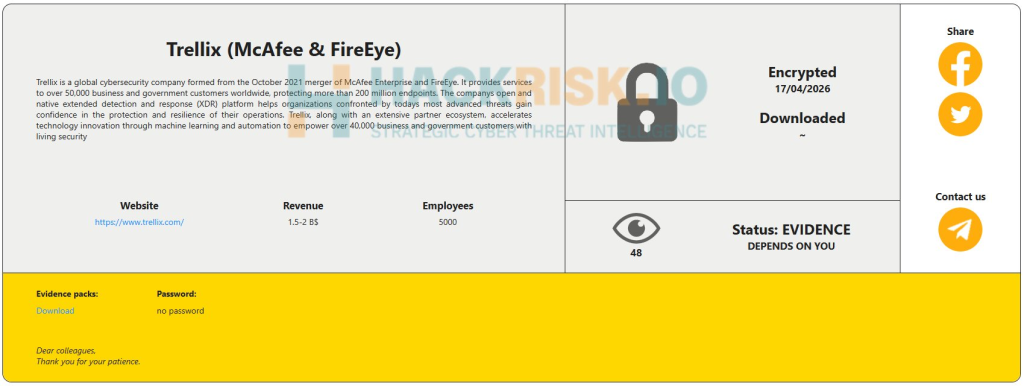
- Threat actor claims: The RansomHouse hacking group claimed responsibility for the cyberattack targeting the Trellix cybersecurity firm.
- Incident status confirmed: Trellix confirmed unauthorized access to a portion of its source code repository on May 8, 2026.
- Distribution process secure: The company’s ongoing investigation found no evidence that the source code release or distribution processes were affected.
The RansomHouse hacking group formally claimed responsibility for a cyberattack against Trellix, which operates within the critical information and communication technology (ICT) sector. The cybersecurity firm recently disclosed unauthorized access to “a portion” of its source code repository.
Forensic Investigation
Trellix has only recently confirmed a security incident, while the RansomHouse threat actor claims the compromise occurred on April 17, 2026. However, the extent of data exposure remains unspecified.
Based on the forensic investigation to date, Trellix said it has found no evidence indicating that its source code release or software distribution processes were affected by the cyberattack.
Furthermore, the firm, which emerged from the merger of McAfee Enterprise and FireEye in October 2021, stated there is no current evidence that the accessed source code has been actively exploited.
Trellix Breach Disclosures
Upon identifying the unauthorized access to its repository, Trellix began working with leading forensic experts to analyze the unauthorized network intrusion and resolve the security matter.
In accordance with established operational procedures, Trellix has also notified relevant law enforcement agencies and intends to share further technical details as appropriate once the comprehensive investigation is complete.
In other recent news, a Woflow data breach exposed nearly 448,000 accounts as a result of a ShinyHunters leak. In early April, ShinyHunters claimed 3 million Salesforce records linked to an alleged Cisco breach stemming from the Trivy supply chain compromise.