VoIP Providers, Preferred by Attackers for High-Volume, Cheaper Email Scams that Reuse Phone Numbers
- VoIP provider abuse: Six of the ten largest scam campaigns relied on VoIP infrastructure due to the ease of API-driven provisioning.
- Extended number lifespan: The median phone number lifespan reached approximately 14 days, effectively evading reputation-based security filters.
- Cross-campaign recycling: Scammers reused numbers across different subject lines, brands, and file formats in seemingly unrelated lures to impersonate multiple brands simultaneously.
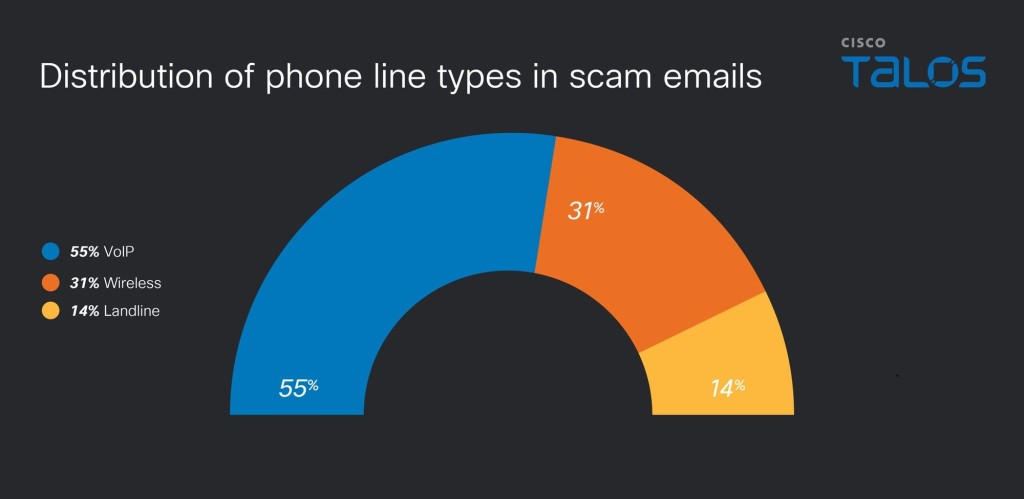
Threat actors heavily abuse VoIP (Voice over Internet Protocol) providers to execute large-scale operations. Between February 26 and March 31, 2026, Cisco Talos researchers observed that six of the ten largest monitored scam campaigns relied directly on VoIP infrastructure, while they recently began collecting phone numbers in emails as a critical indicator of compromise.
To maximize the reach of their infrastructure, attackers actively recycle the same phone numbers across disparate campaigns. Talos observed threat actors embedding identical numbers across completely different subject lines and targeted brands.
Threat Infrastructure and Lifespan
During the study period, Talos identified 1,652 unique phone numbers across campaigns impersonating established brands, including PayPal, Geek Squad (Best Buy), McAfee, and Norton LifeLock. The research highlights specific operational continuity tactics.
Researchers noted that 57 phone numbers, representing about 3.4% of the dataset, were reused across multiple consecutive days. Furthermore, 108 numbers, or roughly 6.5%, remained active for more than one day, yielding a median phone number lifespan of about 14 days.
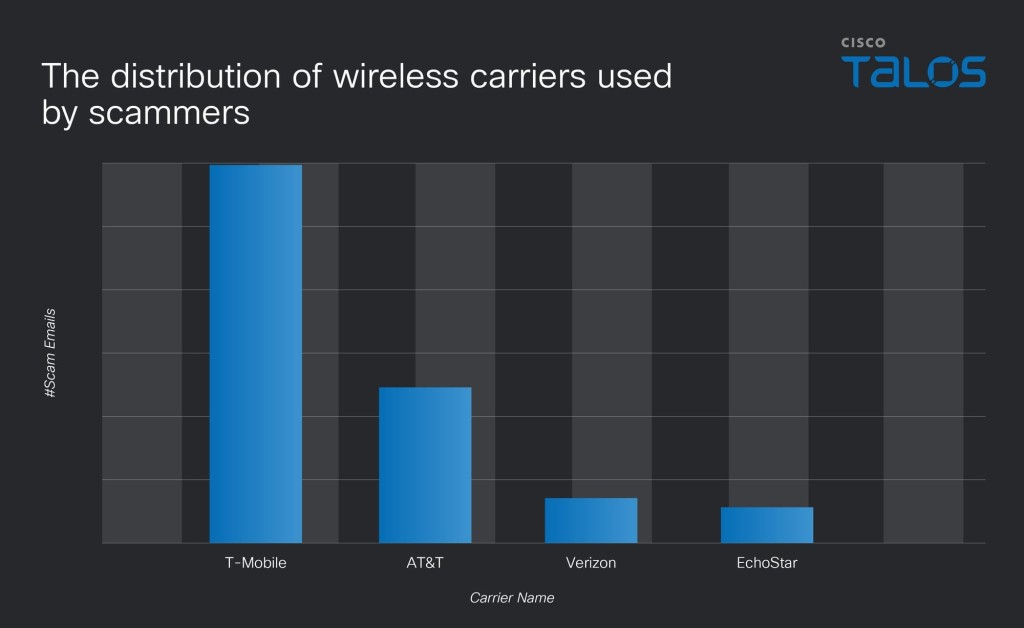
When analyzing specific service providers, Talos found Sinch to be the most commonly abused VoIP provider. Conversely, Verizon and NUSO registered as the least abused providers during the observation period.
“VoIP has become the primary medium for scam campaigns due to its cost-effectiveness, ease of deployment, and API-driven automation,” the report said. “Because these platforms are designed for automation and high-volume traffic, they are frequently exploited by threat actors for rapid, API-driven number provisioning.”
Attack Volume and Campaign Clustering
Threat actors leverage specific telephony assets for high-volume distributions. In one notable instance, scammers used a single phone number, +1 804-713-4598, in 117 scam emails in a single day.
Additionally, operators deployed the same phone numbers across various attachment formats, specifically packaging their lures within HEIC, JPEG, and PDF files to bypass conventional email security filters.
Attackers use specific VoIP grouping and clustering techniques to bypass security filters, appear legitimate, and maintain high-volume operations in scam emails and related smishing or callback scams. One of the most common tactics is sequential number grouping, in which scammers purchase Direct Inward Dialing (DID) blocks and rotate numbers.
Bitdefender’s Security Analyst Alina Bizga told TechNadu in a March interview that fraud becomes more accessible as AI tools and Scam-as-a-Service platforms enable coordinated campaigns.
In other recent news, a phishing campaign is impersonating the U.S. Social Security Administration to target over 80 organizations.