CISA Warns of Severe CopyFail Linux Vulnerability Under Active Exploitation (CVE-2026-31431)
- Active exploitation: The CopyFail bug is actively exploited and has been added to CISA's Known Exploited Vulnerabilities (KEV) catalog.
- Broad impact: The vulnerability affects Linux kernel versions 7.0 and earlier across major enterprise distributions.
- Mandatory patching: CISA ordered all civilian federal agencies to patch affected infrastructure by May 15.
The U.S. government and the Cybersecurity and Infrastructure Security Agency (CISA) have issued a severe warning regarding the CopyFail Linux vulnerability. Tracked formally as CVE-2026-31431, the critical bug affects Linux kernel versions 7.0 and earlier, and it is currently being actively exploited in the wild.
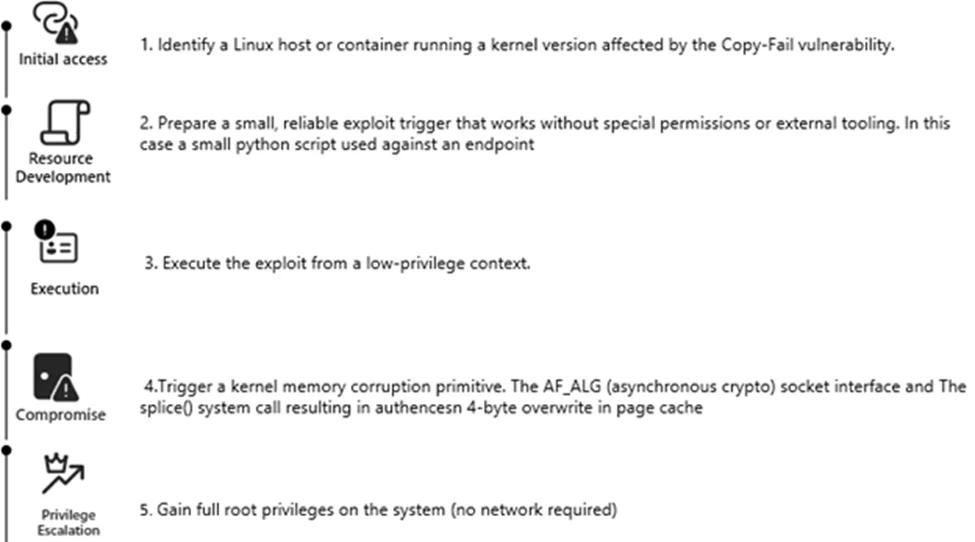
The CopyFail Linux vulnerability, which has been added to CISA's KEV catalog, allows a regular, limited-access user to escalate privileges and gain full administrator access on compromised systems.
Impact on Linux Distributions
Security researchers initially disclosed the flaw to the Linux kernel security team in late March, with a patch released approximately one week later. However, these critical patches have not fully reached many Linux distributions.
“Linux Kernel Incorrect Resource Transfer Between Spheres Vulnerability: Linux Kernel contains an incorrect resource transfer between spheres vulnerability that could allow for privilege escalation,” the CISA advisory states.
Security firm Theori verified the vulnerability affects major enterprise versions, including Red Hat Enterprise Linux 10.1, Ubuntu 24.04 LTS, Amazon Linux 2023, and SUSE 16, according to TechCrunch. Furthermore, developer Jorijn Schrijvershof confirmed that the exploit successfully targets Debian and Fedora distributions, as well as Kubernetes environments.
Attack Chaining and Mitigation Mandates
While the CopyFail vulnerability cannot be exploited autonomously over the internet, Microsoft security analysts report that it can be weaponized when chained with an initial access vector such as Secure Shell (SSH) access, malicious CI job execution, or container footholds.
In response to the active threat landscape, CISA has ordered all civilian federal agencies to patch their affected systems by May 15 to secure critical infrastructure against unauthorized root access.
Earlier this year, Linux was targeted by the VoidLink cloud-native malware framework via a custom plugin API and by the GoBruteforcer botnet.