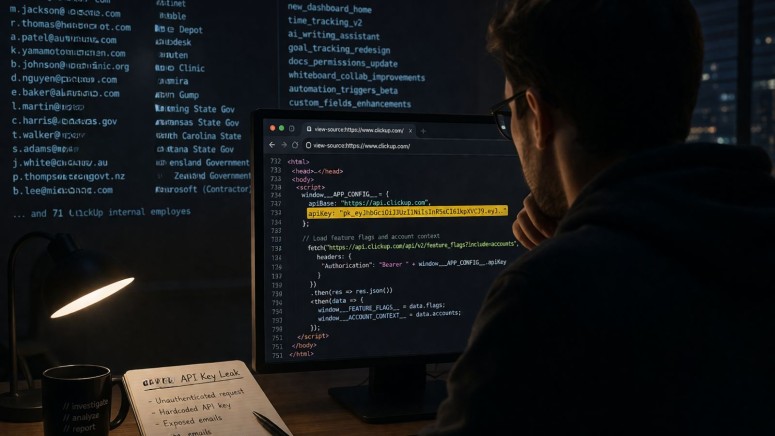
ClickUp Hardcoded API Key Exposes Almost 1,000 Customer Emails, Including Government and Corporate Giants
- Hardcoded API exposure: A ClickUp API key leak exposed nearly a thousand corporate and government emails via an unauthenticated JavaScript file on its homepage.
- Critical organizations affected: This corporate email exposure impacts employees at major security firms like Fortinet and Tenable, creating severe data security risks.
- Unpatched security flaw: Reported via HackerOne in January 2025, this preventable cybersecurity vulnerability remains active and unrotated after 15 months in production.
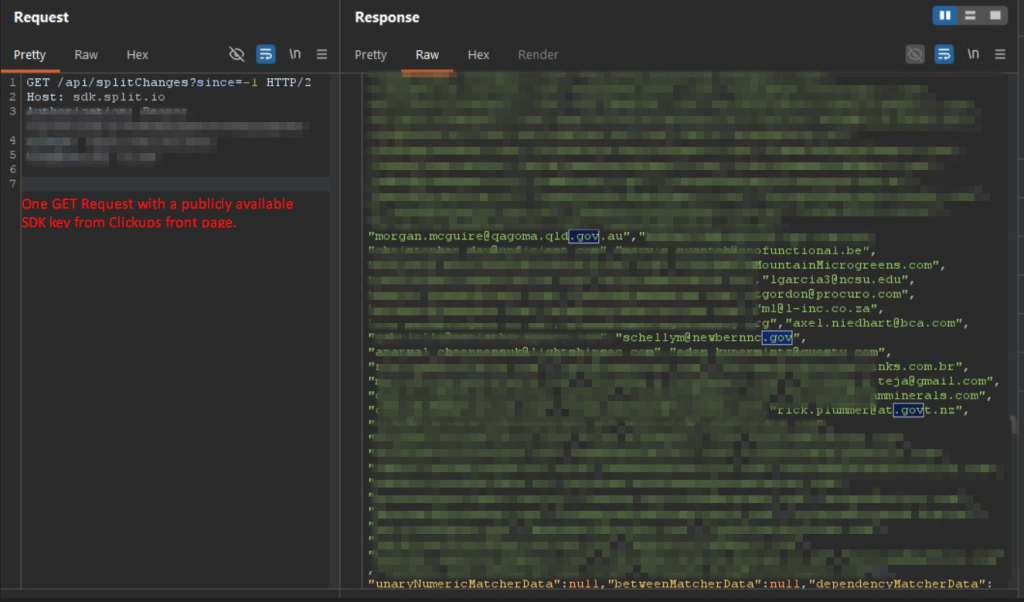
A publicly accessible JavaScript file on the ClickUp homepage has silently leaked 959 email addresses alongside 3,165 internal feature flags. A hardcoded third-party API key embedded in the source code was recently observed, loading before any user authentication occurs.
This massive corporate email exposure impacts workers across well-known companies, U.S. and other governments, and ClickUp itself.
Severe Corporate Email Exposure
A researcher said they could extract these sensitive assets by executing a single unauthenticated GET request, CybersecurityNews has reported. The leak compromises personnel at global enterprise firewall manufacturer Fortinet and Tenable, the developer behind the Nessus vulnerability scanner.
Affected individuals reportedly include employees from:
- Home Depot,
- Autodesk,
- Rakuten,
- Mayo Clinic,
- Permira,
- The Akin Gump law firm.
The exposure also impacts government workers from Wyoming, Arkansas, North Carolina, Montana, Queensland (Australia), and New Zealand, as well as 71 internal ClickUp employees and a Microsoft contractor.
Escalating Data Security Risks
Despite being reported to ClickUp through HackerOne on January 17, 2025, this critical cybersecurity vulnerability remains unpatched in production as of late April 2026, the researcher said, adding that the API key has not been rotated over the past 15 months.
Exposing email addresses from top-tier cybersecurity organizations creates a direct attack surface. Furthermore, the leaked feature flags reveal internal product development signals and beta configurations.
In September 2025, Tenable confirmed a data breach resulting from a compromise of Salesloft and Drift. In February, threat actors leveraged several commercial AI tools to breach 600 FortiGate firewalls.