Robinhood Phishing Emails Target Users via Account Creation Flaw
- HTML injection exploit: Threat actors abused an account creation flaw to inject arbitrary HTML into legitimate Robinhood account confirmation emails.
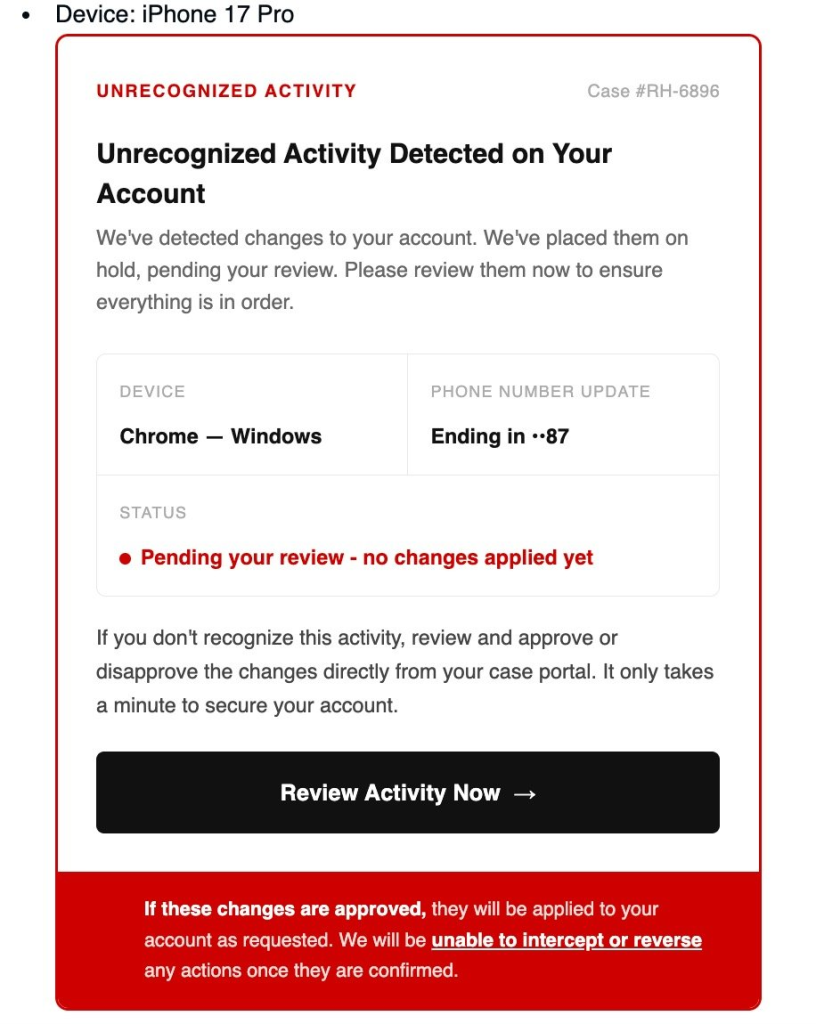
- Spoofed security alerts: The Robinhood phishing emails bypassed standard SPF and DKIM checks, displaying fake unrecognized device warnings to steal user credentials.
- Vulnerability patched immediately: Robinhood resolved the cybersecurity vulnerability by removing the abused metadata field, confirming no customer funds or internal systems were compromised.
Threat actors recently weaponized Robinhood's account registration infrastructure to launch highly convincing credential-harvesting campaigns. By exploiting a critical account creation flaw, cybercriminals injected malicious payloads into automated confirmation emails, successfully manipulating the trading platform's trusted domain to bypass SPF and DKIM email security checks.
Technical Details of the Exploit
Robinhood users recently started receiving emails from the legitimate Robinhood email address [email protected] about purported recent logins or linked devices, each containing an activity review button that linked to a now-down potential phishing site at robinhood[.]casevaultreview[.]com.
Attackers leveraged an HTML injection vulnerability within the platform's onboarding flow. When a new account is registered, Robinhood automatically dispatches a system-generated login notification containing device and location telemetry. Threat actors actively modified these device metadata fields to include malicious HTML payloads.
This sophisticated tactic allowed the Robinhood phishing emails to effortlessly pass SPF and DKIM validation, making them appear completely legitimate to the end user.
“This phishing attempt was made possible by an abuse of the account creation flow,” the company said on X, adding that systems, customer accounts, personal information, and funds were not impacted.
Targeting and Cybersecurity Implications
This Robinhood incident exposes a severe cybersecurity vulnerability inherent in automated email generation systems. Robinhood has since patched the flaw by deprecating the vulnerable Device field from its registration notifications.
To prevent phishing attacks, organizations must mandate rigorous input sanitization and output encoding across all user-supplied metadata fields, ensuring that automated administrative systems cannot be weaponized for advanced social engineering attacks.
Last year, Robinhood Securities and Robinhood Financial agreed to pay the $45 million SEC penalty for failures across multiple operational areas.
This month, a Booking.com data breach exposed sensitive customer information, with reports indicating that cybercriminals are already weaponizing the stolen data for phishing.